Microsoft: 92% of all Exchange servers have been patched or received mitigations for the ProxyLogon bugs
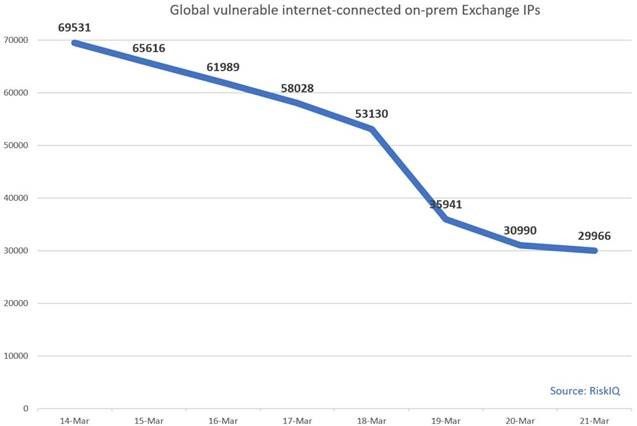
Three weeks after disclosing a major vulnerability in its email server software, Microsoft said today that roughly 92% of all Exchange servers have been patched or received temporary mitigations against the ProxyLogon vulnerabilities and are safe from attacks.
Of a total of 400,000 Exchange email servers deployed on-premises across the world, the OS maker said that around 30,000 are still vulnerable to attacks.
The number has gone down 56% from the 69,500 figure Microsoft reported the week before and down from the 82,000 number the company initially reported on March 12.
In a White House press conference today, Deputy National Security Advisor Anne Neuberger, who is currently leading the investigations into both the SolarWinds and Exchange hacking campaigns, took credit in the name of the Biden administration for the decrease in the number of vulnerable Exchange email servers.
Neuberger said the White House put pressure on the Redmond-based tech giant to make it easier for server owners to fix their systems.
A few days later, Microsoft released the Exchange On-Premises Mitigation Tool, a one-click PowerShell script that would apply all the necessary mitigations to Exchange servers until a more secure patch could be applied.
The tool, available on GitHub, would also scan and remove traces of web shells installed by attackers on vulnerable servers.
Exchange servers have been under attack by multiple Chinese-linked state-sponsored hacking groups even before Microsoft released initial patches on March 2. Those attacks have expanded to cryptocurrency mining groups and ransomware gangs in the meantime and have amplified in scale.
The US and Germany are the two countries most impacted by the ProxyLogon attacks, with the largest number of active Exchange email server installations.
Neuberger said that roughly 10,000 Exchange servers located in the US, from the total of 120,000, have yet to receive a patch or mitigations for the ProxyLogon bugs.
But while some might call the patching pace slow, in reality, it's a spectacular achievement. A similarly dangerous Exchange email server bug (CVE-2020-0688) barely reached a 39% patching rate from February 2020 to October 2020, according to data collected by security firm Rapid7.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.