Microsoft shares one-click ProxyLogon mitigation tool for Exchange servers
Microsoft has published today a one-click software application that applies all the necessary mitigations for the ProxyLogon vulnerabilities to Microsoft Exchange servers that can't be updated for the time being.
The new tool is named EOMT (or the Exchange On-premises Mitigation Tool), is written in PowerShell, and available for download via Microsoft's official GitHub account.
Microsoft said it released the tool to help companies that don't have dedicated IT or security teams to handle updating their on-premises Exchange servers.
Microsoft has released a new, one-click mitigation tool, the Microsoft Exchange On-Premises Mitigation Tool, to help customers who do not have dedicated security or IT teams to apply security updates for Microsoft Exchange Server. Learn more: https://t.co/IfChAqpcEH pic.twitter.com/xD94M8Czg5— Microsoft Security Intelligence (@MsftSecIntel) March 15, 2021
The OS maker hopes that any company's employee would be able to download the tool on a Windows system running an Exchange mail server and execute the EOMT.ps1 PowerShell script by double-clicking on it.
EOMT script also removes web shells
Once started, the script will install a URL Rewrite configuration on the server, which is enough to mitigate CVE-2021-26855, the initial entry point in a series of four bugs known as ProxyLogon.
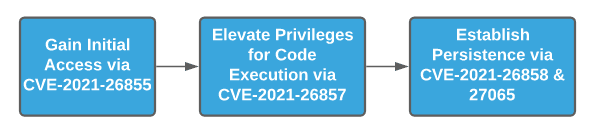
But the tool also includes a copy of the Microsoft Safety Scanner app that will scan the Exchange server for known web shells that have been seen deployed in past ProxyLogon attacks.
Once a web shell is discovered, the Microsoft Safety Scanner app will remove the backdoor and cut off the attacker's access.
Microsoft says the tool can be used to both apply mitigations but also as a way to ensure that past mitigations applied by hand have been installed correctly.
Users who installed patches released on March 2 do not need to run the tool, as the patches provide much better coverage for ProxyLogon attacks.
This also includes an additional set of patches released on March 9 to cover Exchange server versions that have reached end-of-life status.
Attacks on Microsoft have reached a fever pitch after Microsoft disclosed that a group of Chinese state-sponsored hackers known as Hafnium was abusing the four bugs to install backdoors on Exchange servers across the world.
Since the initial disclosure, nine state-sponsored groups have been seen abusing the ProxyLogon vulnerabilities, two crypto-mining groups, and a ransomware gang. Attacks also intensified after the release of a free proof-of-concept exploit.
Last week, Microsoft said that of the roughly 400,000 Exchange servers deployed across the internet, 318,000 appear to have been patched against the ProxyLogon vulnerabilities.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.