Attacks on Exchange servers expand from nation-states to cryptominers
The ongoing mass exploitation campaign targeting Microsoft Exchange email servers has expanded in less than a week to include attacks from multiple nation-state hacking groups and cybercrime operations alike.
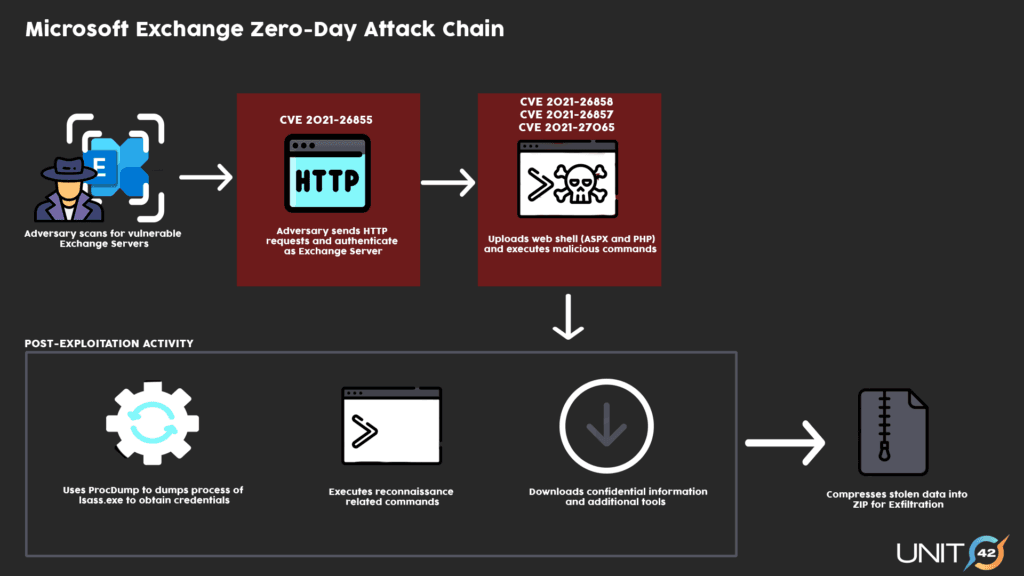
The attacks —first disclosed last week by Microsoft— are related to four vulnerabilities that security researchers are calling ProxyLogon.
The four bugs can be chained together to provide attackers with a way to authenticate on Exchange servers as an admin user and then install malicious programs.
According to the ProxyLogon website, details about two of the four bugs were discovered last year and reported to Microsoft in early January by Orange Tsai, a security researcher at security firm DEVCORE.
Microsoft initially planned to fix the two issues during the March 2021 Patch Tuesday, but in parallel with the initial bug report, two security firms (Volexity and Dubex) began detecting attacks against their customers using mysterious Exchange vulnerabilities, which they reported to Microsoft.
When the OS maker connected the reported attacks with the ProxyLogon bug reports, Microsoft responded by releasing last Tuesday emergency security patches for Exchange servers, urging companies across the world to patch their on-premises email servers.
At the time, Microsoft said that initial attacks exploiting these four vulnerabilities were being carried out by a new hacking group the company was tracking as Hafnium, a group the company formally linked to the Chinese government, based on previously observed activity.
Other threat actors join ProxyLogon exploitation
But as news of the attacks and the severity of the four vulnerabilities began to spread, so did the attacks.
By Friday, March 5, several security firms came out to confirm not only Hafnium attacks but a free-for-all against Exchange servers, with exploitation attempts originating from separate clusters of activity.
For example, ESET reported attacks from the LuckyMouse, Tick, and Calypso APTs, but also "a few additional yet-unclassified clusters."
FireEye also reported seeing attacks from three different clusters the company was tracking as UNC2639, UNC2640, and UNC2643.
Furthermore, security firm Red Canary also reported seeing activity originating from the cybercrime sector, with one group using the Exchange flaws to install web shells on infected servers and then install the DLTminer malware. Other reports came from security firm Binary Defense.
Attacks from multiple threat actors were also confirmed by Microsoft in an update to its original Hafnium blog post.
But while attacks at the start of last week were limited to one group, reports from Wired and KrebsOnSecurity on Friday confirmed that the ever-increasing number of attackers had moved into indiscriminate mass-exploitation against any Exchange server left connected to the internet without a patch, with the number of hacked servers being estimated in the real of "astronomical" and tens of thousands, per US government sources.
Intrusions reported all over the globe, not just US
And the attacks didn't target just Exchange email servers at US companies. Over the past week, security agencies in the Netherlands, the Czech Republic, and Norway reported responding to ongoing Exchange intrusions in their countries.
Victimized organizations who have admitted so far to Exchange intrusions include the Czech Minister of Labour and Social Affairs and the post offices of Prague, and the European Banking Authority.
Other countries, such as Australia, the United Kingdom, Germany, Romania, Austria, Sweden, Finland, Spain, New Zealand, France, Singapore, Hungary, Ireland, Canada, and Italy, have released national security alerts, warning companies and government organizations to patch on-premises Exchange servers as soon as possible.
However, even if these countries have not reported attacks, security vendors are now seeing attacks all over the globe, with Kaspersky reporting a spike in attacks targeting Germany, Malwarebytes reporting ProxyLogon-related web shells on at least 1,000 customer systems, and HuntressLabs seeing at least 1,500 infected systems.
There is a general consensus in the cybersecurity community that these attacks are as bad as it gets, and that many of these intrusions will materialize into something way worse.
The initial attacks were conducted by nation-state threat actors seeking to exfiltrate sensitive communications from web servers, but the fact that cybercrime groups are now getting involved also means that many of the web shells planted on Exchange servers will soon be weaponized for mass data theft, extortions, and even ransomware attacks.
Lots of free tools available
However, the response of the cybersecurity community has been extremely helpful for all those involved over the weekend in patching Exchange servers.
Besides releasing patches last week, Microsoft has also followed through and released indicators of compromise associated with known attacks, so companies can prepare defenses and sift through logs.
In addition, the OS maker also released a PowerShell script to search Exchange servers for the presence of an intrusion and known web shell indicators, and a similar script was also released by the CERT-Latvia team over the weekend.
Furthermore, over the weekend, Microsoft has also updated the Microsoft Support Emergency Response Tool (MSERT) to detect signs of intrusions on servers where Microsoft Defender is not installed and wouldn't be able to automatically detect ProxyLogon indicators.
Besides the original patches, Microsoft also released additional updates for Exchange servers that had reached end-of-life and are now unsupported.
Today, PwnDefend has also released a list of IP addresses associated with servers scanning and exploiting Exchange email servers over the past few weeks.
The commoditization of these attacks and ProxyLogon exploits was not a surprise, as most bad bugs eventually get exploited; however, the speed at which attacks moved from the realm of nation-state attackers to regular cybercrime operations was surprising, especially since no public detailed bug description or proof-of-concept code was ever made public.
This suggests the ProxyLogon bugs were easy to spot using a basic technique known as patch-diffing, and the vulnerability is also likely very easy to weaponize even for attackers with little technical expertise.
All in all, back in December, it would have been hard to believe that another cybersecurity issue could have made everyone forget about the damage caused by the SolarWinds supply chain attack, but we sometimes forget how intertwined the tech ecosystem really is and that there are far more popular products than the SolarWinds Orion app.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.