QNAP warns of zero-day vulnerability in latest DeadBolt ransomware campaign
Data-storage hardware vendor QNAP warned customers this weekend that the DeadBolt ransomware group is using a recently patched zero-day vulnerability in its latest campaign.
QNAP’s security team told The Record that it discovered a new DeadBolt campaign on the morning of September 3. If a network-attached storage (NAS) device is exposed to the internet and installs the application Photo Station, the spokesperson said, it would be "in the high risk."
QNAP did not share a CVE for the vulnerability or go into detail about what happened. But the company said in an advisory that it fixed the Photo Station vulnerability within 12 hours of its use by DeadBolt actors and urged users to take a range of actions to protect themselves, including making sure their devices are not exposed to the internet, as they have cautioned in the past.
Users should also take snapshots of their systems or have backups to make sure their information is not lost in the event of an infection.
The company also suggested using the photo management software QuMagie in QNAP NAS devices instead of Photo Station.
Months of attacks
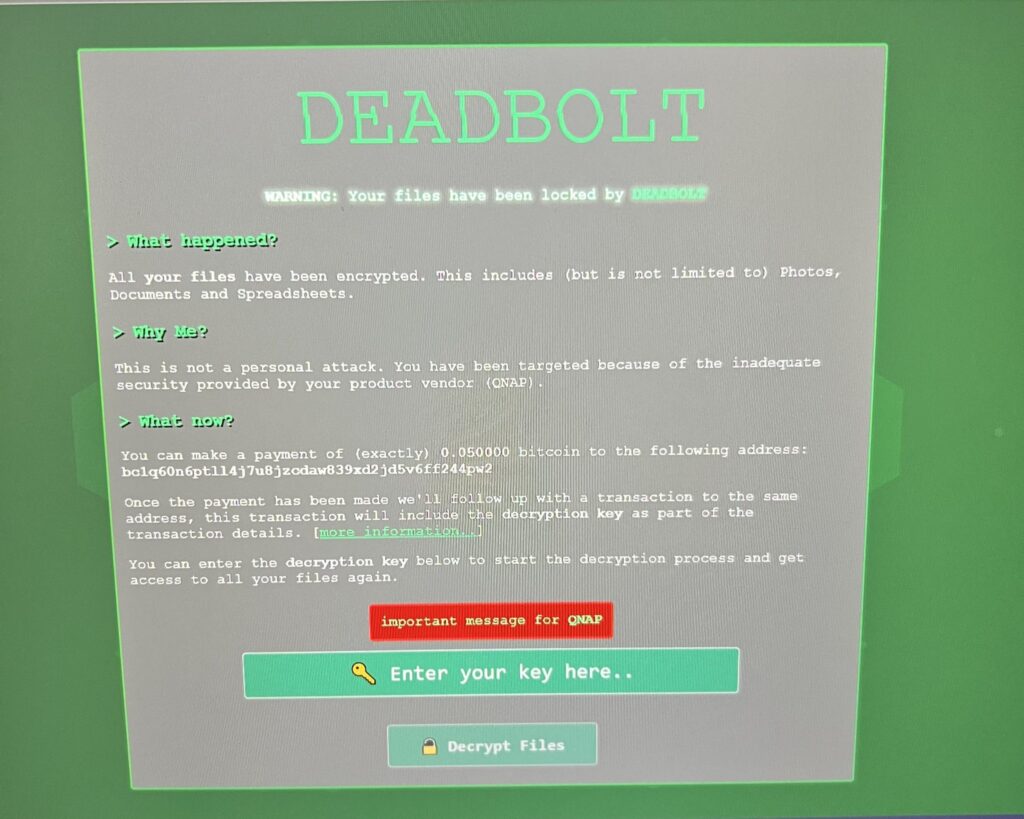
Since January, thousands of QNAP customers using the company’s NAS devices have reported being attacked by the DeadBolt ransomware group, which demands a ransom of 0.03 Bitcoin ($1,100) for the decryption key.
After the initial attacks affecting about 3,600 devices January, the group continued to resurface with campaigns in March, May, and June this year. Reddit and other message boards have been flooded with customers lamenting the loss of files that included family photo albums, wedding videos and more. Dozens of users took to Reddit to complain that they were among those attacked in the latest campaign.
In a note to QNAP, the hackers demanded 5 Bitcoin ($93,900) to reveal details about the alleged zero-day vulnerabilities they initially used to attack its users and another 50 Bitcoin ($939,000) to release a master decryption key that would unlock all of the victims’ files.
QNAP would not say if it has considered paying the ransom for the universal decryption key when asked by The Record but a spokesperson said the company’s research has shown the group is attacking “legacy versions with known vulnerabilities which have security updates available.”
I just got hacked. Ransomware named DeadBolt found an exploit in @QNAP_nas storage devices, encrypting all files. They ask $1,000 from individuals or $1.8 million from QNAP. I have 50tb of data there, none of it essential or sensitive, but it hurts a lot. Time for a fresh start. pic.twitter.com/E8ZkyIbdfp
— Lex Fridman (@lexfridman) January 27, 2022
“We urge users, don't expose NAS on the internet. In addition, keep not only firmware but also all applications up to date for safety,” a spokesperson said.
After the initial infections in January, the company urged users to update to the latest version of QTS, the Linux-based operating system developed by the Taiwanese company to run on its devices.
But eventually QNAP took more drastic actions, pushing out an automatic, forced update for all customers’ NAS devices to version 5.0.0.1891, the latest universal firmware, which was released last December.
Some users have also disputed QNAP’s insistence that only devices that have not been updated are being attacked.
Security company Emsisoft released its own version of a DeadBolt decryptor after several victims reported having issues with the one they received in exchange for paying a ransom.
However, it only works with a decryption key supplied by the operators of the DeadBolt ransomware through a ransom payment.
QNAP users who got hit by DeadBolt and paid the ransom are now struggling to decrypt their data because a forced firmware update issued by @QNAP_nas removed the payload that is required for decryption. If you are affected, please use our tool instead. https://t.co/6fvO8ntvrU
— Fabian Wosar (@fwosar) January 30, 2022
Security company Censys reported that of the total 130,000 QNAP NAS devices sold, 4,988 services “exhibited the telltale signs of this specific piece of ransomware.”
Censys managed to track the Bitcoin wallet transactions associated with an infection and found that of the previous batch of victims, 132 paid ransoms totaling about $188,000. The company also created a dashboard to track the number of victims around the world.
The majority of the most recent infections are taking place in the U.S., Germany and the United Kingdom.
Other companies’ storage devices have also been attacked. The users of Asustor’s NAS hardware were warned in February of potential DeadBolt ransomware infections after dozens took to Reddit and other message boards to complain of attacks.
QNAP has previously warned of different ransomware strains being used to target their users, including the Checkmate ransomware and the ech0raix ransomware.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



