QNAP: Checkmate ransomware group targeting customers through SMB Services
Taiwanese hardware vendor QNAP sent out a warning on Thursday about a new ransomware called Checkmate that is being used to target customers via Server Message Block (SMB) services exposed to the internet.
In an advisory, QNAP’s security team said the issue was recently brought to their attention and that they are in the process of investigating the ransomware.
“Preliminary investigation indicates that Checkmate... employs a dictionary attack to break accounts with weak passwords,” QNAP explained, referring to a strategy in which hackers systematically enter every word in a dictionary as a way to break into a password-protected device. QNAP did not respond to follow-up questions about how they knew the Checkmate ransomware group was using this method as opposed to others.
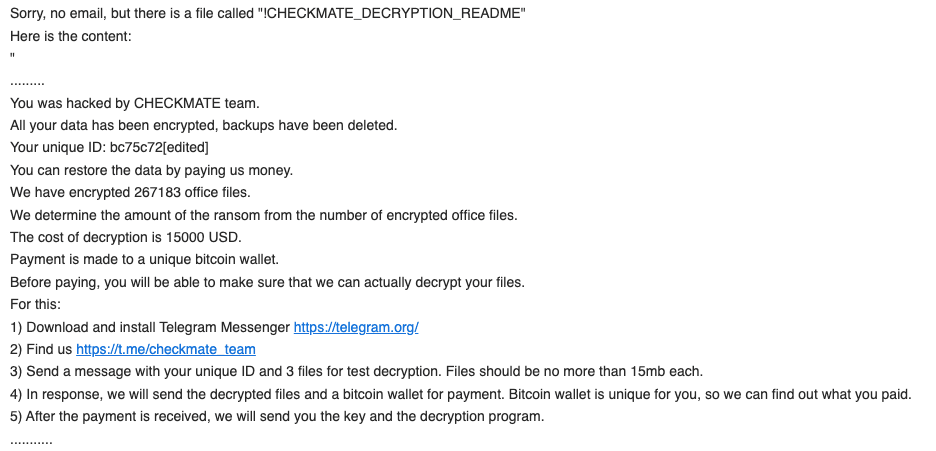
“Once the attacker successfully logs in to a device, they encrypt data in shared folders and leave a ransom note with the file name "!CHECKMATE_DECRYPTION_README" in each folder. We are thoroughly investigating the case and will provide further information as soon as possible.”
SMB is a client-server communication protocol used to share access to a variety of devices, files and more. QNAP recommended its users disconnect their SMB service from the internet and urged others to limit their exposure by using VPN services.
The company did not respond to requests for comment about how many devices have been infected.
Several QNAP users took to a BleepingComputer forum to say they were affected by the Checkmate ransomware last month and hit with a ransom note demanding $15,000 in bitcoin.
QNAP has been dealing with several ransomware groups attacking their customers over the last two years, most recently facing hundreds of attacks from the Deadbolt ransomware group.
While the company has repeatedly claimed the group was exploiting an old vulnerability, several users said they had been attacked through an updated version.
About two weeks ago, the company said it was investigating yet another Deadbolt campaign targeting users of its network-attached storage (NAS) devices.
It is unclear where members of Deadbolt are based but the ransomware group emerged in January and launched attacks on thousands of NAS devices around the world.
Security company Censys reported that of the total 130,000 QNAP NAS devices sold, 4,988 of them “exhibited the telltale signs of this specific piece of ransomware.”
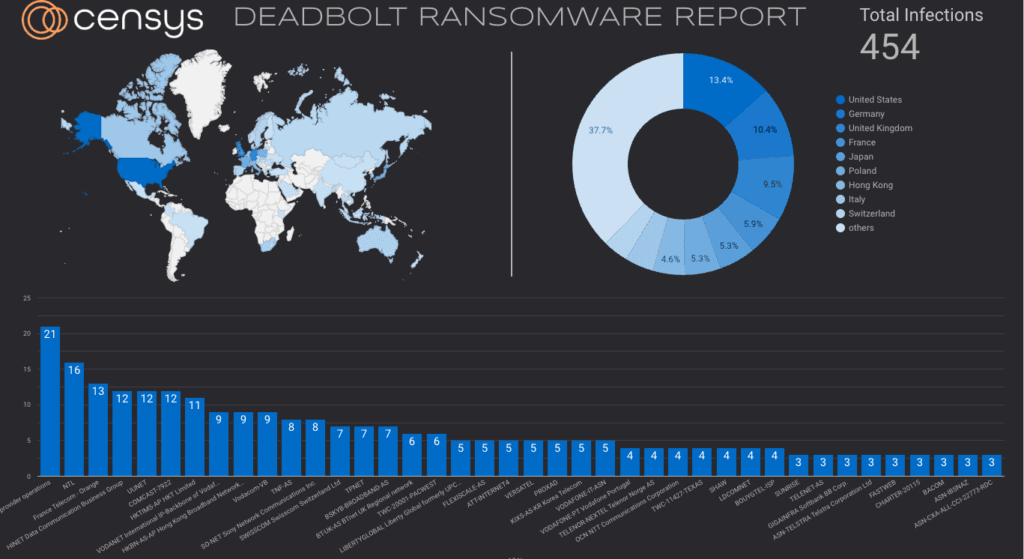
In May, Censys managed to track the Bitcoin wallet transactions associated with an infection, finding that 132 victims had paid ransoms totaling about $188,000. The company also created a dashboard to track the number of victims around the world.
Most of the recent infections have occurred in the United States, Germany and the United Kingdom.
After a brief respite following the January attacks, Censys said more than 1,000 QNAP devices were infected with the Deadbolt ransomware in March.
Other companies’ devices have also been attacked. Users of Asustor’s NAS hardware were warned in February of potential Deadbolt ransomware infections after dozens of people took to Reddit and other message boards to complain of attacks.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



