U.S. gov’t unveils sanctions, charges, bounties on Iranian ransomware actors
The U.S. government unveiled a slate of sanctions, charges and bounties on Wednesday related to a group of Iranian nationals accused of working with the country’s military to launch ransomware attacks against hundreds of American hospitals, governments, nonprofits and businesses.
The Department of the Treasury’s Office of Foreign Assets Control (OFAC) said the hackers had been active since 2020, attacking everything from a New Jersey municipality to a children’s hospital, as well as transportation providers, healthcare practices, emergency service providers, and educational institutions.
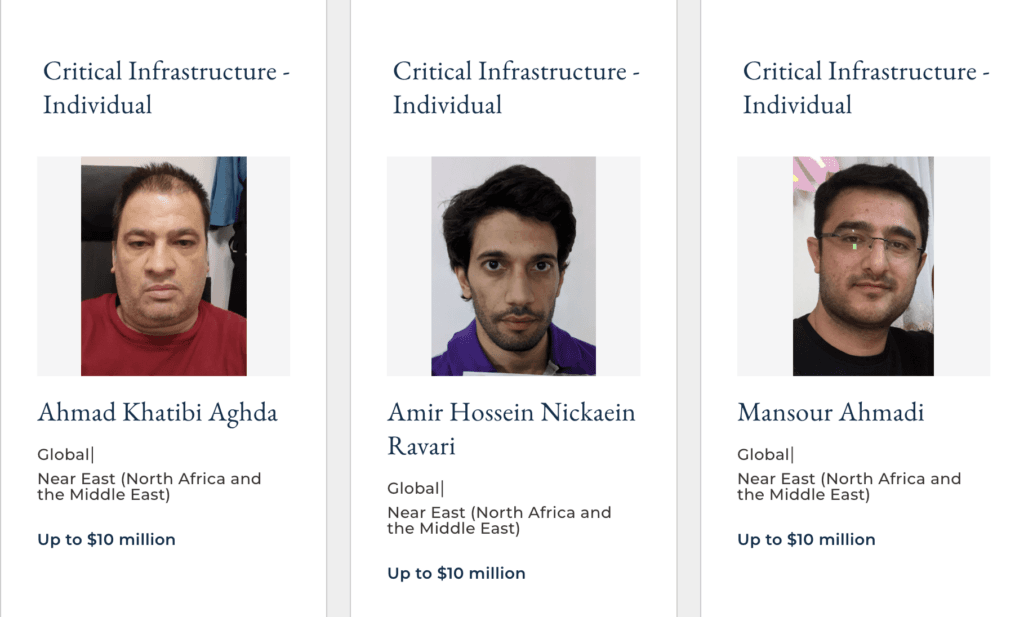
In total, OFAC announced sanctions against 10 Iranians — Mansour Ahmadi; Ahmad Khatibi Aghda; Ali Agha-Ahmadi; Mohammad Agha Ahmadi; Mo’in Mahdavi; Aliakbar Rashidi-Barjini; Amir Hossein Nikaeen Ravari; Mostafa Haji Hosseini; Mojtaba Haji Hosseini; and, Mohammad Shakeri-Ashtijeh.
OFAC also sanctioned two companies — Najee Technology Hooshmand Fater and Afkar System Yazd Company — where the hackers allegedly work.
Officials from the Justice Department, State Department, FBI, U.S. Cyber Command, NSA and Cybersecurity and Infrastructure Security Agency said the men and the companies were “affiliated” with Iran’s Islamic Revolutionary Guard Corps (IRGC).
All are now banned from doing business in the U.S. and three of the men — Mansour, Khatibi, and Nikaeen — were indicted by the U.S. Attorney’s Office for the District of New Jersey for their role in several attacks.
A State Department official told several news outlets ahead of the announcements that the three men were not always working on behalf of Iran's government but sometimes purely out of financial gain. Even if some actions were not directed by government, the official said, they occurred "because the regime permits hackers to largely operate with impunity."
One of the three, Khatibi, is accused of being directly in charge of ransom negotiations with victims. A report from cybersecurity firm SecureWorks revealed that the ransom noted included technological markers tying it directly to Khatibi and Afkar System.
“Ransom-related cyberattacks — like what happened here — are a particularly destructive form of cybercrime,” said U.S. Attorney Philip R. Sellinger for the District of New Jersey.
In February 2021, the three hackers allegedly targeted the Union County township in New Jersey before attacking a Morris County, New Jersey accounting firm in February 2022.
A month later, Khatibi demanded payment of $50,000 in cryptocurrency from another accounting firm that had been attacked.
The indictment lists hundreds of other attacks where the three compromised, encrypted and extorted victims like a regional electric utility company based in Mississippi, a regional electric utility company based in Indiana and a public housing corporation in the State of Washington.
The group also attacked a shelter for victims of domestic violence in Pennsylvania, securing a $13,000 payment; a county-level government in Wyoming; a construction company located in the State of Washington that was engaged in work on critical infrastructure projects; a state bar association, and even targets inside of Iran.
REWARD! Up to $10M for information on Iranian malicious #cyber actors AHMADI, KHATIBI & NICKAEIN. They targeted U.S. critical infrastructure and compromised hundreds of computer networks across the U.S. and abroad. GOT A TIP? Contact RFJ today! https://t.co/jA8oZs6D2o pic.twitter.com/26isfc8fqx
— Rewards for Justice (@RFJ_USA) September 14, 2022
All three men are facing about 20 years in jail but are based in Iran, making arrests unlikely. In an effort to collect tips on their whereabouts, the State Department added the three to its Rewards for Justice (RFJ) program.
Mansour, Khatibi, and Nikaeen each have a $10 million bounty attached to their names. Last week at the Billington Cybersecurity conference, FBI Assistant Director of Cyber Division Bryan Vorndran said the RFJ program had already “borne fruit” since several eastern European hackers were added to the list.
Under Secretary of the Treasury for Terrorism and Financial Intelligence Brian Nelson said ransomware groups associated with the IRGC are “threatening the physical security and economy of the United States and other nations.”
“The Government of Iran has created a safe haven where cyber criminals acting for personal gain flourish and defendants like these are able to hack and extort victims, including critical infrastructure providers,” said Assistant Attorney General Matthew Olsen of the Justice Department’s National Security Division.
“This indictment makes clear that even other Iranians are less safe because their own government fails to follow international norms and stop Iranian cyber criminals.”
In a press release, the U.S. agencies noted that the sanctions on the group will now apply to those considering paying a ransom — a controversial topic among those who feel sanctions are an additional penalty targeting victims.
The agencies said organizations are “strongly discouraged from paying ransoms as doing so does not guarantee files and records will be recovered and may pose sanctions risks.”
The OFAC notice ties the men to groups given a variety of names by cybersecurity companies, including: “APT 35,” “Charming Kitten,” “Nemesis Kitten,” “Phosphorus,” and “Tunnel Vision.”
Exploitation of Log4j, Fortinet, Microsoft Exchange
Alongside the sanctions and bounties, the Cybersecurity and Infrastructure Security Agency (CISA) worked with cyber agencies at several allied nations to release a technical advisory about the tactics used by the hackers in a number of incidents.
The hackers typically target known Fortinet and Microsoft Exchange vulnerabilities to “gain initial access to a broad range of targeted entities in furtherance of malicious activities, including ransom operations,” the agency said.
“In addition to exploiting Fortinet and Microsoft Exchange vulnerabilities, the authoring agencies have observed these APT actors exploiting VMware Horizon Log4j vulnerabilities for initial access. The IRGC-affiliated actors have used this access for follow-on activity, including disk encryption and data extortion, to support ransom operations,” CISA said.
This CSA highlights the ongoing global threat from Iran’s IRGC cyber actors exploiting known vulnerabilities. Collaboration w/our interagency & international partners is key to delivering timely, actionable information to net defenders. Read it here: https://t.co/yg6AmWhqLy pic.twitter.com/UxS9ZOSqnV
— Jen Easterly (@CISAJen) September 14, 2022
Eric Goldstein, Executive Assistant Director at CISA, implored organizations to address the vulnerabilities in the advisory and take other steps to protect systems.
Last week, OFAC released another tranche of sanctions against Iran’s primary intelligence agency and its top official less than two days after Albania cut diplomatic ties with Tehran over an attack on the country’s government websites.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



