Ransomware tracker: Threat groups focus on vulnerable targets
As the recent attack against Colonial Pipeline shows, ransomware groups consider just about any organization to be fair game.
Vulnerable organizations including healthcare companies and schools have been constantly bombarded with ransomware attacks over the last year, according to data collected by Recorded Future from government agencies, news reports, hacking forums, and other sources. For example, there were 7 hospitals, healthcare systems, and clinics that disclosed ransomware attacks last month, down from a record high of 17 in March and 9 in April 2020.
Ransomware operators seem to be expanding their reach outside the U.S.—5 out of the 7 attacks against healthcare organizations happened abroad, said Allan Liska, a ransomware specialist at Recorded Future who is involved in the analysis. For example, French newspapers reported on a ransomware attack that disrupted the computer systems and telephones at Saint-Gaudens hospital in the Pyrenees.
<html>
<head>
<style>
.overlay-marker {
width: 150px;
height: 50px;
position: relative;
top: 45px;
/* chartArea top */
right: -430px;
/* chartArea left */
z-index: 1;
}
</style>
<title>Ransomware Attacks Against Healthcare Organizations</title>
<script type = "text/javascript" src = "https://www.gstatic.com/charts/loader.js"></script>
<script type = "text/javascript">
google.charts.load('current', {packages: ['corechart','line']});
</script>
</head>
<body>
<div class="overlay-marker">
<img src="https://www.recordedfuture.com/wp-content/uploads/logo-primary-black-2020.svg" height="15">
</div>
<div id="Health_container" style = "width: 550px; height: 400px;"></div>
<script language = "JavaScript">
function drawHealthChart() {
// Define the chart to be drawn.
var data = new google.visualization.DataTable();
data.addColumn('string', 'Month');
data.addColumn('number', 'Incidents');
data.addRows([
['01/20', 5],
['02/20', 6],
['03/20', 5],
['04/20', 9],
['05/20', 12],
['06/20', 4],
['07/20', 7],
['08/20', 9],
['09/20', 16],
['10/20', 13],
['11/20', 3],
['12/20', 9],
['01/21', 4],
['02/21', 7],
['03/21', 17],
['04/21', 7],
]);
// Set chart options
var options = {
chart: {
title: 'Ransomware Attacks Against Healthcare Organizations',
subtitle: 'Source: Recorded Future. Graphs can be repurposed with attribution.',
},
hAxis: {
title: 'Month',
},
legend: {
position: 'none'
},
series: {
0:{color:'#fc791b'},
},
'width':550,
'height':400,
};
// Instantiate and draw the chart.
var chart = new google.charts.Line(document.getElementById('Health_container'));
chart.draw(data, options);
}
google.charts.setOnLoadCallback(drawHealthChart);
</script>
</body>
</html>
“While the United States is still a big target for big game hunting ransomware attacks, the attackers are expanding their attack surface and looking at other targets,” Liska said. “I think this also reflects better reporting of ransomware attacks in [other] countries as well.”
Attacks against school systems also remained high, despite declining slightly from March. There were 9 disclosed attacks against schools in April, which compares to 13 during the previous month and 1 incident in April 2020.
Based on data from last year, there’s the possibility that ransomware attacks against schools could drop significantly over the summer—there were no reported ransomware attacks against schools in May 2020, and only one attack in June.
<html>
<head>
<style>
.overlay-marker {
width: 150px;
height: 50px;
position: relative;
top: 45px;
/* chartArea top */
left: 430px;
/* chartArea left */
z-index: 1;
}
</style>
<title>Ransomware Attacks Against Schools</title>
<script type = "text/javascript" src = "https://www.gstatic.com/charts/loader.js"></script>
<script type = "text/javascript">
google.charts.load('current', {packages: ['corechart','line']});
</script>
</head>
<body>
<div class="overlay-marker">
<img src="https://www.recordedfuture.com/wp-content/uploads/logo-primary-black-2020.svg" height="15">
</div>
<div id="Gov_container" style = "width: 550px; height: 400px;"></div>
<script language = "JavaScript">
function drawGovChart() {
// Define the chart to be drawn.
var data = new google.visualization.DataTable();
data.addColumn('string', 'Month');
data.addColumn('number', 'Incidents');
data.addRows([
['01/20', 4],
['02/20', 5],
['03/20', 5],
['04/20', 1],
['05/20', 0],
['06/20', 1],
['07/20', 6],
['08/20', 9],
['09/20', 10],
['10/20', 8],
['11/20', 4],
['12/20', 3],
['01/21', 1],
['02/21', 7],
['03/21', 13],
['04/21', 9]
]);
// Set chart options
var options = {
chart: {
title: 'Ransomware Attacks Against Schools',
subtitle: 'Source: Recorded Future. Graphs can be repurposed with attribution.',
},
hAxis: {
title: 'Month',
},
legend: {
position: 'none'
},
series: {
0:{color:'#fc791b'},
},
'width':550,
'height':400,
};
// Instantiate and draw the chart.
var chart = new google.charts.Line(document.getElementById('Gov_container'));
chart.draw(data, options);
}
google.charts.setOnLoadCallback(drawGovChart);
</script>
</body>
</html>
Perhaps the biggest drop in ransomware figures comes from extortion sites, which a wide variety of operators have set up to pressure victims into paying demands. Over the last two years, it has become common for ransomware attackers to steal sensitive data from victims before encrypting their information and devices—they then post a small amount of this data on extortion sites, threatening to sell or publicly reveal the rest of the data if the ransom isn’t paid. About one-in-six ransomware payments carries a sanctions violations risk, The Record reported Tuesday.
Last month, there were only 106 victims posted on extortion sites tracked by Recorded Future, down from 261 in March and 521 in December 2020.
<html>
<head>
<style>
.overlay-marker {
width: 150px;
height: 50px;
position: relative;
top: 45px;
/* chartArea top */
left: 430px;
/* chartArea left */
z-index: 1;
}
</style>
<title>Victims on ransomware extortion sites</title>
<script type = "text/javascript" src = "https://www.gstatic.com/charts/loader.js"></script>
<script type = "text/javascript">
google.charts.load('current', {packages: ['corechart','line']});
</script>
</head>
<body>
<div class="overlay-marker">
<img src="https://www.recordedfuture.com/wp-content/uploads/logo-primary-black-2020.svg" height="15">
</div>
<div id="Extortion_container" style = "width: 550px; height: 400px;"></div>
<script language = "JavaScript">
function drawExtortionChart() {
// Define the chart to be drawn.
var data = new google.visualization.DataTable();
data.addColumn('string', 'Month');
data.addColumn('number', 'Incidents');
data.addRows([
['02/20', 11],
['03/20', 17],
['04/20', 48],
['05/20', 57],
['06/20', 73],
['07/20', 154],
['08/20', 91],
['09/20', 172],
['10/20', 265],
['11/20', 179],
['12/20', 521],
['01/21', 328],
['02/21', 270],
['03/21', 261],
['04/21', 106]
]);
// Set chart options
var options = {
chart: {
title: 'Victims on Ransomware Extortion Sites',
subtitle: 'Source: Recorded Future. Graphs can be repurposed with attribution.',
},
hAxis: {
title: 'Month',
},
legend: {
position: 'none'
},
series: {
0:{color:'#fc791b'},
},
'width':550,
'height':400,
};
// Instantiate and draw the chart.
var chart = new google.charts.Line(document.getElementById('Extortion_container'));
chart.draw(data, options);
}
google.charts.setOnLoadCallback(drawExtortionChart);
</script>
</body>
</html>
Although Liska said the decline could be a reflection of victims choosing to negotiate before their data gets exposed, it is also possible that attacks from these groups are decreasing. “I don't like to predict trends based on one month of data… but I think it reflects a true, but probably temporary, slowdown in the number of attacks,” he said. However, there will “undoubtedly be a resurgence in attacks at some point [as] there is simply too much money in ransomware for attackers to stop.”
Two ransomware task forces—one from the U.S. Department of Justice and one from a public/private consortium of several dozen organizations—were also announced in April with the aim of curbing ransomware attacks going forward. Both were formed in part due to the increasing losses caused by ransomware and the urgency of the issue, which only increased last week when Colonial Pipeline announced that it had to shut down 5,500 miles of fuel pipelines after suffering a ransomware attack that has since been attributed to Darkside.
Although it’s difficult to quantify the total number of ransomware attacks, Michael Daniel, president of the Cyber Threat Alliance and a co-chair of the public/private Ransomware Task Force, said in an interview with The Record that there is a clear trend in all the measurements of a steady rise in attacks.
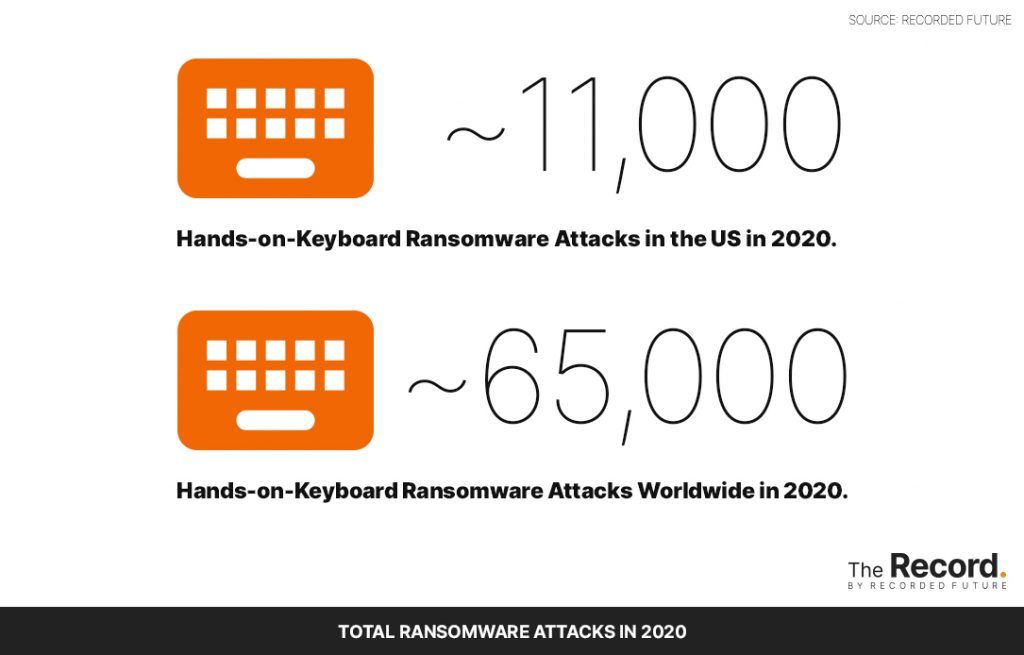
While the vast majority of ransomware incidents are “one shot” attacks that only target a single machine, Liska estimates that there were about 11,000 hands-on-keyboard attacks in the U.S. and about 65,000 such attacks worldwide in 2020 that required some level of advanced targeting. The estimates are based on an analysis of data shared by major ransomware operators in addition to research developed by Valery Marchive, chief editor at LeMagIT in France, on the ratio of victims who pay ransomware demands.
The Record by Recorded Future allows outside organizations to share and distribute graphs from this ongoing project with proper attribution.
Adam Janofsky
is the founding editor-in-chief of The Record from Recorded Future News. He previously was the cybersecurity and privacy reporter for Protocol, and prior to that covered cybersecurity, AI, and other emerging technology for The Wall Street Journal.



