FBI: Colonial Pipeline was hit with Darkside ransomware
The U.S. Federal Bureau of Investigation confirmed on Monday that the attack that shut down one of the country’s largest pipelines over the weekend was caused by Darkside ransomware.
Although the statement was short—the only thing the FBI added was that it continues “to work with the company and our government partners on the investigation”—it provides valuable details for network defenders both inside and outside of critical infrastructure sectors.
The Darkside group was first spotted by cybersecurity researchers around August 2020, according to data collected by Recorded Future, and is believed to be run by former affiliates of other ransomware families who decided to develop their own code. In recent months, the group has gained attention both for its attacks and also its statements around the organizations it targets and avoids.
For example, in January the group declared that they no longer attack healthcare providers, companies that participate in the development and distribution of COVID-19 vaccines, and funeral service organizations including morgues, crematoria, and funeral homes.
“We are apolitical, we do not participate in geopolitics, do not need to tie us with a defined government and look for other our motives,” the group wrote in a recent statement on its dark web site. “Our goal is to make money, and not creating problems for society. From today we introduce moderation and check each company that our partners want to encrypt to avoid social consequences in the future.”
DarkSide #ransomware Leaks Press Center: pic.twitter.com/NNmv0UphQw
— (@ddd1ms) May 10, 2021
Policymakers in the U.S. estimate that the vast majority of the nation’s critical infrastructure—perhaps as much as 80-90%—is owned by the private sector. Although the group has not made any statements about pipelines and other energy infrastructure, they seem to consider organizations like Colonial Pipeline fair game. Additionally, the group has been tied to at least one previous attack on the energy sector.
In February, Darkside ransomware operators claimed responsibility for an attack targeting Companhia Paranaense de Energia, or Copel, a state-owned electric utility company in Brazil. The group claimed to have exfiltrated over 1,000 GB of data, including network maps, backup schemes and schedules, and domain zones for Copel’s main site.
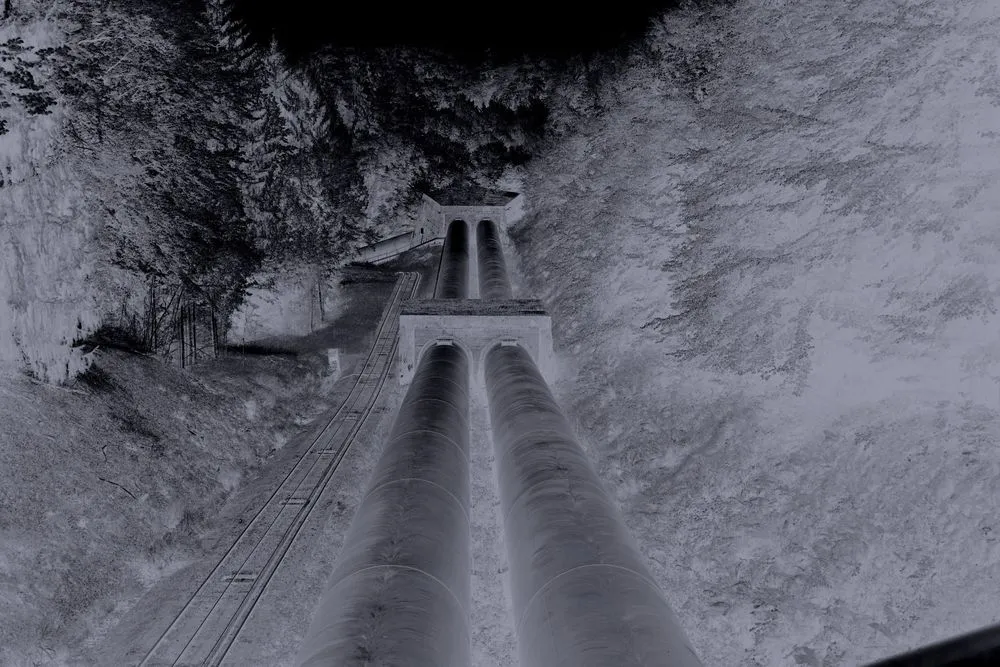
Colonial Pipeline, founded in 1962, operates about 5,500 miles of pipeline that delivers gasoline, diesel, jet fuel, home heating oil, and other fuel through Southern and Eastern U.S. In response to the attack, the Department of Transportation's Federal Motor Carrier Safety Administration issued a regional emergency declaration on Sunday for 17 states and Washington, D.C., to keep fuel supply lines open, Axios reported.
According to data collected by Recorded Future, Darkside was the first ransomware variant to formally offer a way for people to buy breach information related to publicly traded companies, which could then be used to make trades against the stock. In April, the group made an announcement on its extortion website asking those interested to use a contact form to submit a request for information—the group promised to provide detailed information about the uncooperative victims whose data will be published in the near future.
Recent research from cybersecurity firms including Cybereason and Varonis have found some patterns in the groups tactics, techniques, and procedures (TTPs). These include obtaining valid accounts for initial access and lateral movement, abusing exposed or unsecured remote services for initial access and lateral movement, enumerating network shares and local drives, and executing the payload via scheduled tasks.
“The DarkSide group is a relatively new player in the game of ransomware. Despite being a new group, though, the DarkSide team has already built itself quite a reputation for making their operations more professional and organized,” Cybereason researchers said. “The group has a phone number and even a help desk to facilitate negotiations with victims, and they are making a great effort at collecting information about their victims - not just technical information about their environment, but more general information about the company itself, like the organization’s size and estimated revenue.”
Adam Janofsky
is the founding editor-in-chief of The Record from Recorded Future News. He previously was the cybersecurity and privacy reporter for Protocol, and prior to that covered cybersecurity, AI, and other emerging technology for The Wall Street Journal.