Not just ransomware: Schools and universities are increasingly targeted by impersonation scams
Last August, the IT security staff at the University of Maryland, Baltimore County noticed a phishing email that was unusually intricate.
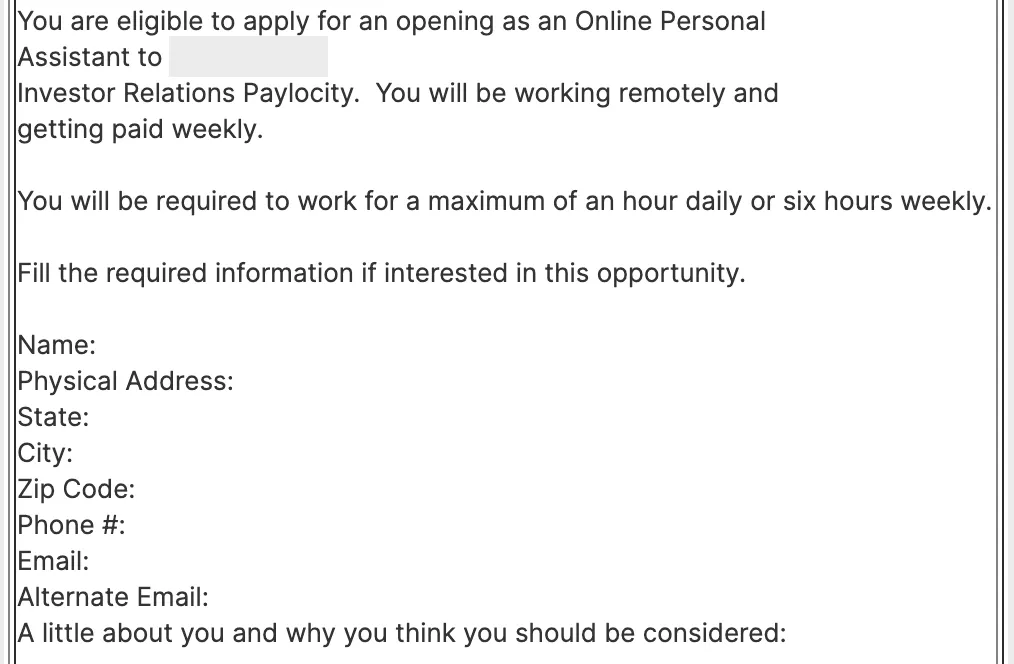
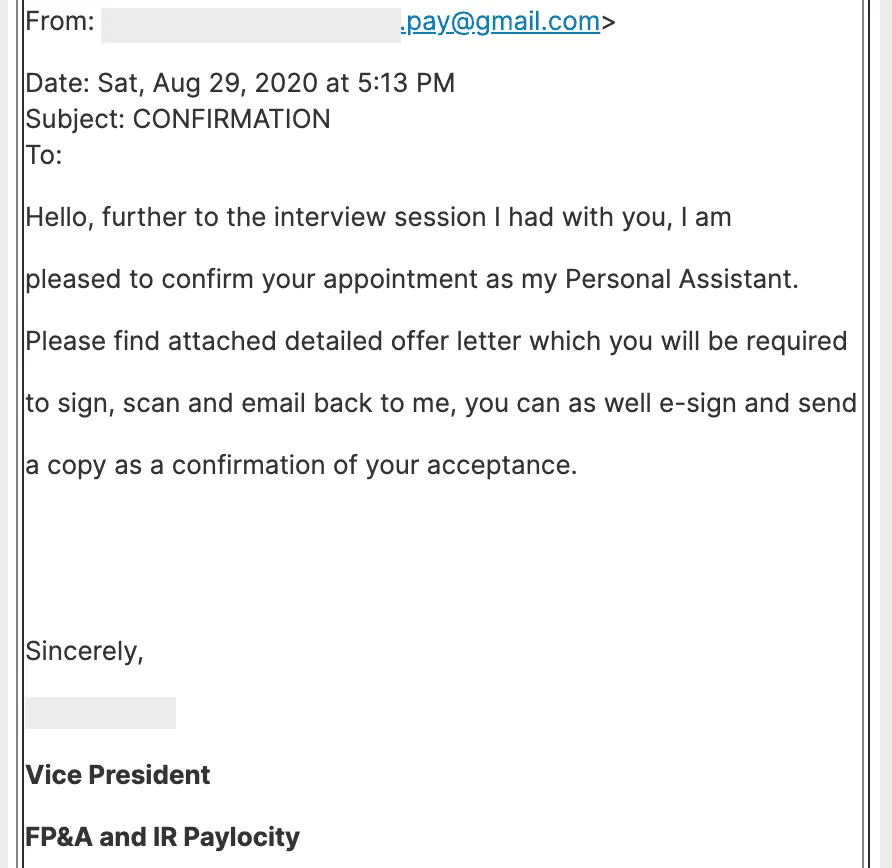
Unlike obvious scams that ask for gift cards using typo-laden text, the email was a fake job application allegedly sent by someone working for a real investor relations executive at Paylocity. The email asked interested candidates to send basic information, including a phone number and email address, as well as “a little about you and why you think you should be considered” for an executive assistant role. Students who went through with the application process eventually received a follow-up email that appeared to come from the Paylocity executive, confirming their appointment as his personal assistant and asking them to fill out hiring paperwork.
The scam was similar to legitimate emails that came from companies in the past, said UMBC’s chief information security officer Mark Cather. “We actually do see emails that are almost the same—an executive looking for an assistant—but when we contact them, they’re legitimate,” he said. “The scammers have been getting better at their craft… They’re going after universities and individual departments because it’s a smaller, more trusted network.”
Schools and universities, which were once seen as poor targets for financially-motivated cybercrime, are now awash in impersonation scams and other attacks. On March 30, the IRS warned students and staff at educational institutions of an “ongoing IRS-impersonation scam that appears to primarily target educational institutions, including students and staff who have ‘.edu’ email addresses.” The agency has received a number of reports recently of tax refund scams and phishing attempts targeting people at these institutions, it said.
Another common scam over the last two years that has ensnared countless university staff—at institutions including the University of Albany, Harvard University, the University of Houston, and the University of Iowa—involve impersonations of department heads. Attackers often closely research their targets, and may include signatures in their emails that list legitimate information, like their office location, telephone number, and degree qualifications.
At Rollins College, a visiting professor almost sent one of these impersonators $700 before he realized it was a scam—a technical glitch led him to only lose $75, according to The Sandspur, the college’s news site. Like the incident at UMBC, the scam involved follow-ups: the first email asked for the visiting professor’s phone number, after which he received a text message asking for assistance.
Although cyberattacks are increasing across a number of sectors, there are a few reasons why students and staff are being targeted, cybersecurity experts said. Universities by nature try to facilitate open ecosystems, where researchers can easily collaborate with people at other institutions and the local community. They may also be less willing than for-profit organizations to invest in adequate security tools and personnel. And young students may be more trusting and susceptible to scammers who reach out to them.
Ransomware attacks against schools have also risen sharply in recent years, which has received extensive attention due to the disruptions it causes. There were 13 publicly disclosed ransomware attacks against schools in March, compared to 7 in February and 5 in March 2020, according to data collected by Recorded Future.
Cather said he’s particularly alert at the beginning of the semester, and warns new students to be cautious. “Scammers target the August and September timeframe, because incoming freshmen have a lot of things up in the air—classes are new, it’s the first time they’re handling money. Their entire life structure is Jell-O at that point,” he said. “Impersonators look for those patterns when you’re out of balance or stressed.”
A spokesperson for Paylocity said the company has seen these types of impersonation incidents increasing in general, and recommends its employees to carefully monitor their social media accounts for suspicious activity or impersonators. “We have trained our employees and are driving external awareness to alert people how to identify illegitimate messages used in fraud scams,” including double-checking email addresses and checking that the hiring manager knows intimate details about the position.
One challenge with these scams is that there’s not an easy way to stop them. “Unfortunately there’s not much someone like this executive can do,” said Cather. “The best they can do is make some kind of public posting that says if you see a job offer from me, I’m being impersonated.”
Adam Janofsky
is the founding editor-in-chief of The Record from Recorded Future News. He previously was the cybersecurity and privacy reporter for Protocol, and prior to that covered cybersecurity, AI, and other emerging technology for The Wall Street Journal.



