Massive FluBot Botnet Infects 60,000 Android Smartphones
In the span of just two months, a new Android malware strain named FluBot has infected more than 60,000 devices, with 97% of the victims located in Spain.
First spotted at the start of the year by security firm ThreatFabric (under the name of Cabassous), FluBot's inner workings were described in a report [PDF] published today by Swiss security firm PRODAFT.
New Android banking Trojan “Cabassous” doesn’t yet provide more than classic overlay and SMS stealing features but is the only known active banker using DGA.
— ThreatFabric (@ThreatFabric) January 6, 2021
It uses an RSA based DH scheme to protect the communications with the C2 and obtains relevant C2 addresses using a DGA. pic.twitter.com/NDrBCoiyWn
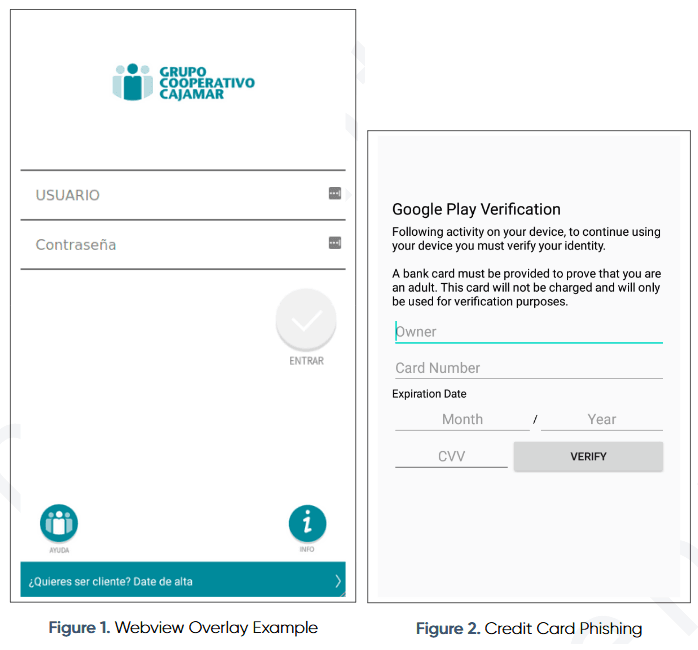
The PRODAFT report paints the picture of a dangerous Android banking trojan that can show fake login screens on top of legitimate apps to collect e-banking credentials and payment card details from device owners.
But such capabilities are also found in other Android malware threats, which are not so widely spread. FluBot's sudden explosion in infection numbers can be explained by the presence of a clever worm-like mechanism inside its code that allows the malware's operator to collect the victim's address book on their command-and-control server.
From this server, PRODAFT said the FluBot gang uses an "SMS load distribution mechanism" to send SMS spam to victims' contacts.
These SMS messages contain different lures to trick recipients into clicking a link. These links usually point to a hacked website where the FluBot gang hosts versions of their malware hidden inside legitimately looking APK files (Android's app file format).
If users download and install these apps—by ignoring all of the operating system's warnings about installing apps from third-party sources—they get infected with a tethered version of the FluBot trojan.
This version doesn't have full control of a device unless victims grant it access to the Android Accessibility service, which allows the malware to execute commands and screen taps, all while being invisible to the device owner.
This allows the FluBot trojan to intercept and block app notifications, set itself as the default SMS app, make USSD and phone calls, and steal the victim's contact lists to enrich the malware gang's SMS spam target list. But more importantly, the Accessibility service is the core feature that will allow the trojan to show its phishing screens on top of other legitimate apps.
FluBot has collected phone numbers for 25% of Spain's population
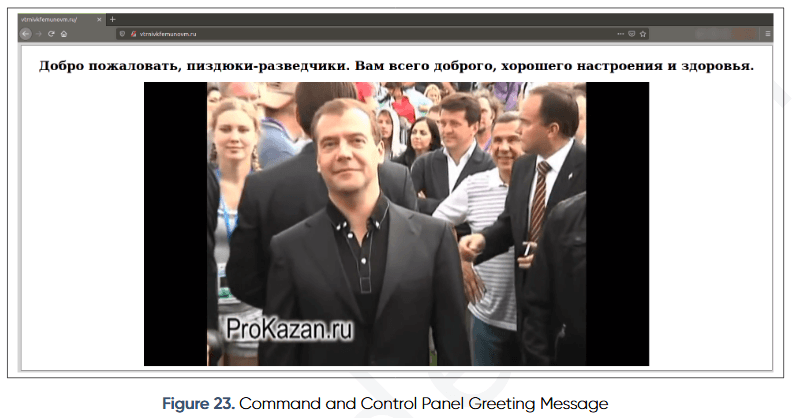
But PRODAFT said it was also able to track down and access the FluBot command and control panel, which is how it was able to determine the number of infected devices.
"Despite its simplistic view, the control panel was able to handle around 60,000 infected device connections without any performance issues," the company said today.
But according to PRODAFT researchers, the most worrying aspect of the FluBot operation was the fact that they spread so quickly in just a two-month span.
"Currently, there are more than 11 million phone numbers collected from the infected devices, which represents 25% of the total population in Spain," the company said.
"We estimate that the malware is capable to collect almost all phone numbers in Spain within 6 months time if no action is taken."
In an interview today, Ahmet Bilal Can, a security researcher at PRODAFT, told The Record that they've notified Spanish law enforcement of their findings, so authorities can take actions against the botnet.
"Our theory is that due to Spain's insufficient mobile banking infrastructure, threat actors find it easier to cash out stolen money and get away with it," Can said—when we asked why the trojan targeted Spanish users more than others.
"Our recent studies on Turkish threat actors also show that they are sharing TTP with Spanish threat actors in order to get into the Spain targeted malware market," he added.
Play Store users safe, but not really
The researcher also told The Record that, for the time being, there is little danger to encounter FluBot-infected apps on the Play Store since it contains plenty of generic banking trojan features.
"FluBot can't bypass checks of Play Protect," Can said. "That's why it's trying to disable Play Protect."
However, the researcher warns that dropper-as-a-service malware operations like Brunhilda could sneak apps on the Play Store on FluBot's behalf and download the trojan at a later date, after they've already compromised devices on their own, deploying FluBot as a second-stage payload.
An additional report on the FluBot malware, in Spanish, is also available from Hispasec, with FluBot being named Fedex Banker [PDF].
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.



