Hackers are spreading malware via trending TikTok challenge: report
Hackers are using a popular TikTok challenge to get people to download information-stealing malware, according to a new report from cybersecurity firm Checkmarx.
The campaign takes advantage of a TikTok trend called the “Invisible Challenge” in which people use a special video effect called “invisible body” to pose naked. The effect produces a blurred, contoured image of a person.
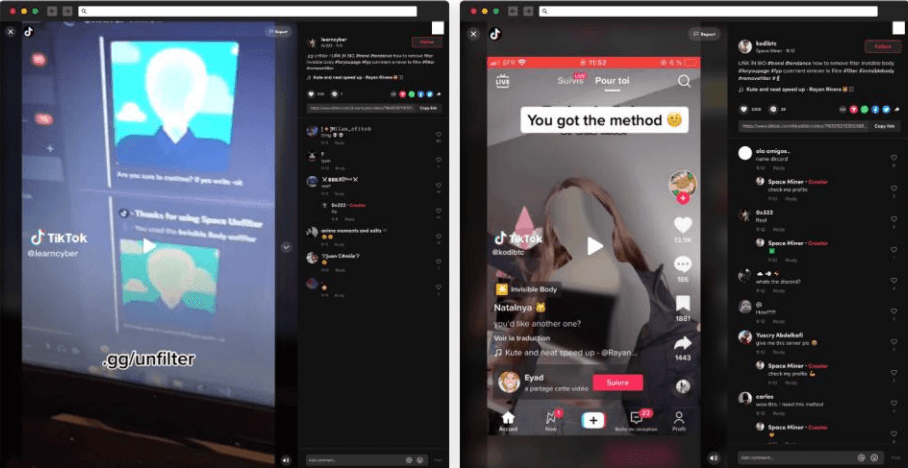
The hackers posted their own TikTok videos with links to fake software called “unfilter” that claims to be able to remove the TikTok filters and expose people’s naked bodies. The malware is hidden in malicious Python packages.
Guy Nachson, supply chain security researcher at Checkmarx, told The Record that the hackers’ videos reached more than a million views in only a few days and the GitHub repo hosting the attacker’s code was listed on GitHub’s daily trending projects.
More than 30,000 members have joined the Discord server created by the attackers so far and this number continues to increase as this attack is ongoing, Nachson added.
“We can't say the exact number of people who ran the malware, but this is the first time we have seen that kind of activity and publicity that flies under the radar,” he explained.
“What alarms us the most is his use of legitimate services – Tiktok, Discord and GitHub. The attacker used an open-source malicious code (W4SP-stealer) hosted on GitHub, uploaded his project to GitHub, and used a TikTok trend to trick people into using his malicious project. Further, he built a community around his project.”
TikTok did not respond to multiple requests for comment.
The #invisiblefilter tag has over 25 million views and Checkmarx said TikTok users @learncyber and @kodibtc posted videos on TikTok promoting a software app able to remove the “invisible body” feature. The videos also included an invite link to the Discord server “discord.gg/unfilter” that had the software.
Once the invite link is clicked and the Discord server is joined, users are taken to a page where the hackers shared naked videos of people allegedly resulting from the “unfilter” software.
In addition to the Discord link, a private message is sent with a request to star the GitHub repository 420World69/Tiktok-Unfilter-Api. This GitHub repository purports to have an open-source tool that can remove the invisible body effect trending on TikTok.
Within the GitHub repository’s files is a malicious package that has been reported and removed multiple times. So far, the repository has 103 stars.
“This campaign is linked to other malicious Python packages, ‘tiktok-filter-api,’ ‘pyshftuler,’ and ‘pyiopcs,’ and since this is an ongoing attack we’re keeping track of new updates,” the researchers said.
After being reported multiple times, the attacker decided to move the malicious part of the Python package to the requirements.txt file listing.
Whenever the security team at Python deletes the hacker’s packages, the person quickly improvises and creates a new identity or simply uses a different name, the researchers explained.
The researchers said this was a concerning example of how social media and the software supply chain are being manipulated by attackers.
“These attacks demonstrate again that cyber attackers have started to focus their attention on the open-source package ecosystem. We believe this trend will only accelerate in 2023,” they said.
“As we see more and more different attacks on the ecosystem, it is critical to expedite the flow of information on these attacks across all parties involved (package registries, security researchers, developers) to protect the open-source ecosystem against those threats.”
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



