Fortinet warns of hackers targeting governments through VPN vulnerability
Fortinet published an advisory this week warning that a critical vulnerability is being exploited by an “advanced actor” to target government networks.
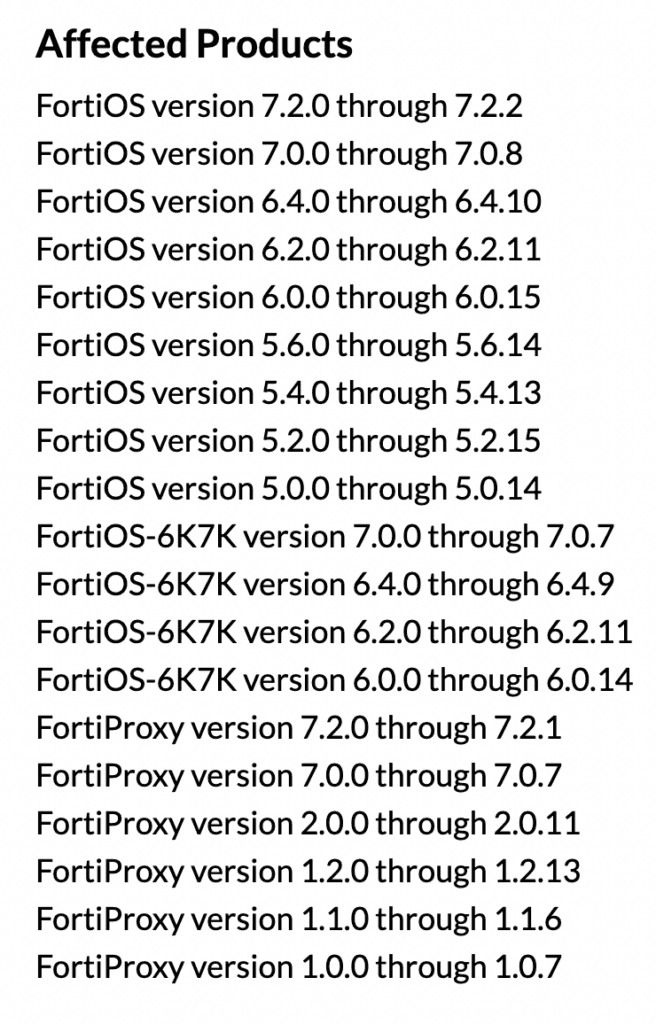
Fortinet published an advisory about the bug – CVE-2022-42475 – and it quickly garnered widespread attention due to its 9.8 CVSS score, ease of use and the large number of FortiOS versions affected.
French security firm Olympe was the first to spot the bug in the wild and Fortinet patched the issue just three days later. Cybersecurity researcher Kevin Beaumont said the bug was being used by ransomware groups.
The Cybersecurity and Infrastructure Security Agency (CISA) published its own advisory about the issue on December 12 urging administrators to look through Fortinet’s advisory.
CISA said an attacker could exploit the vulnerability “to take control of an affected system” and said the vulnerability was already being exploited.
This week, Fortinet released an examination of an exploit for the bug and said the complexity of it “suggests an advanced actor and that it is highly targeted at governmental or government-related targets.”
The company said it got a sample of the malware – which was a variant of a generic Linux implant customized for FortiOS.
“The exploit requires a deep understanding of FortiOS and the underlying hardware. The use of custom implants shows that the actor has advanced capabilities, including reverse-engineering various parts of FortiOS. The actor is highly targeted, with some hints of preferred governmental or government-related targets,” Fortinet said.
“The discovered Windows sample attributed to the attacker displayed artifacts of having been compiled on a machine in the UTC+8 timezone, which includes Australia, China, Russia, Singapore, and other Eastern Asian countries.”
Tenable’s Claire Tills said the critical flaw is a buffer overflow vulnerability – which involves overloading a buffer with more data than it can handle, causing a crash or creating an entry point for attacks.
Tills explained that CVE-2022-42475 could lead to remote code execution in several versions of FortiOS used in SSL-VPNs and firewalls.
“Fortinet SSL-VPNs have been a major target for years now — to the extent that the FBI and CISA issued a dedicated advisory to these flaws and their exploitation in 2021,” she said, referencing several alerts from the FBI and CISA about government hackers using FortiOS vulnerabilities.
“Nation state actors are still known to exploit those legacy vulnerabilities in Fortinet SSL-VPNs. Given that this new vulnerability has already been exploited, organizations should patch CVE-2022-42475 immediately before it joins the ranks of other legacy VPN flaws.”
In 2021, Fortinet also said a cybercriminal gang managed to obtain a collection of access credentials for more than 87,000 FortiGate SSL-VPN devices.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



