Fortinet warns customers after hackers leak passwords for 87,000 VPNs
Networking equipment vendor Fortinet has notified customers today that a cybercriminal gang has assembled a collection of access credentials for more than 87,000 FortiGate SSL-VPN devices.
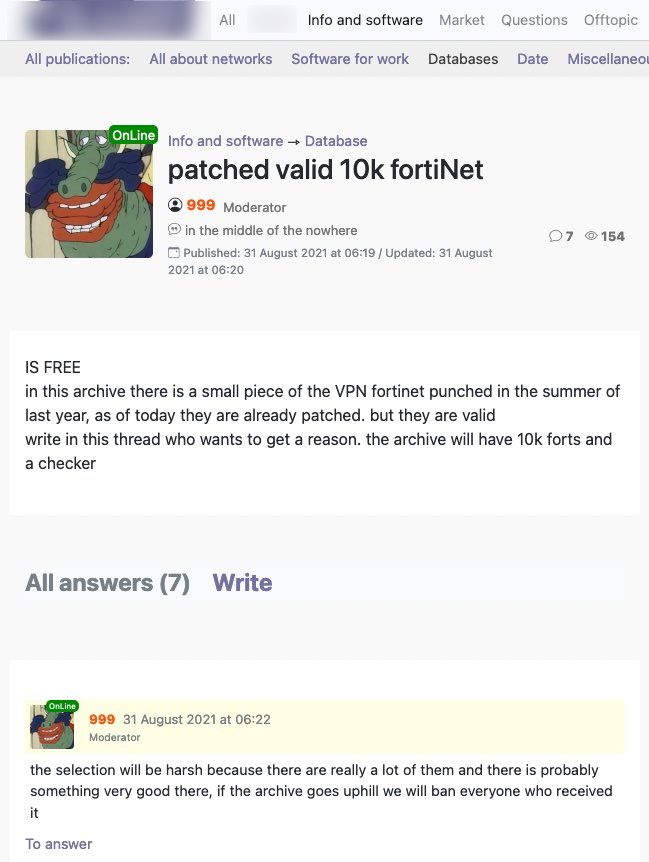
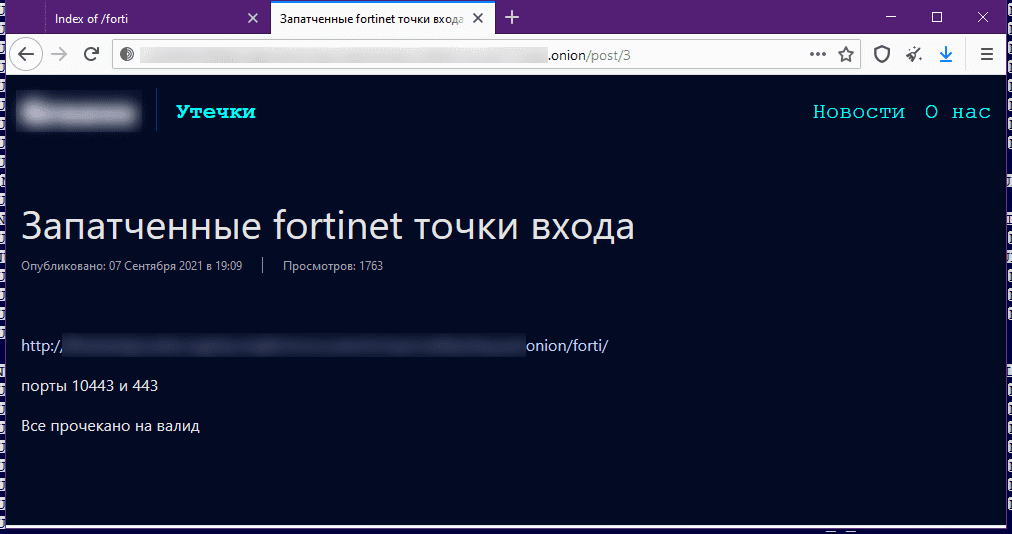
"This incident is related to an old vulnerability resolved in May 2019," the company said in a blog post following an inquiry from The Record sent on Tuesday, when a small portion of this larger list was published on a private cybercrime forum hosted on the dark web, and later on the website of a ransomware gang, known to have close affiliations with the same forum.
"These credentials were obtained from systems that remained unpatched against FG-IR-18-384 / CVE-2018-13379 at the time of the actor's scan," Fortinet said.
Sources familiar with the existence of this collection told The Record the list had been compiled more than a year ago and had been sold in private circles to different threat actors, including groups who carried out ransomware attacks.
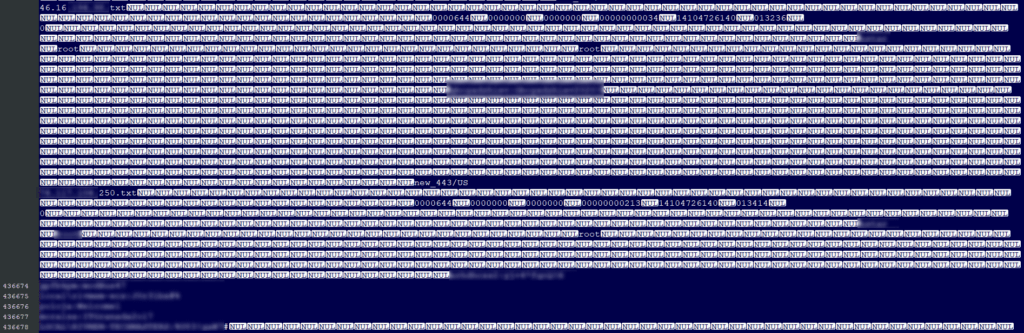
While it would be illegal to grab Fortinet credentials and check if they were still valid, as this would amount to a CFAA violation, The Record was able to find two security researchers who tested the credentials from the sample leaked on the dark web hacking forum earlier this week.
The researchers, who publicly admit to being "gray hats" but still did not want their names included in this article for legal reasons, said that from a list of 502,677 credentials, belonging to around 22,500 Fortinet VPNs, the vast majority (varying from 80% to 90%, depending on scan) did not work anymore, or the login screen was protected by a two-factor authentication system.
This would explain why this small sample from a larger 87,000 collection would be leaked from professional data traders and their closed circles into the public domain.
In the meantime, Fortinet is recommending that companies who use Fortinet SSL-VPN devices apply the patch for CVE-2018-13379, released back in May 2019, and rotate passwords for all device accounts after they install the patch.
In its blog post earlier today, the company pointed out that it had warned its customers five different times about this issue until now — in May 2019, August 2019, July 2020, April 2021, and again in June 2021.
While there are many reasons for delaying a patch, running crucial devices such as a FortiGate SSL-VPN system unpatched for two years has no excuse and amounts to derelict of duty on the part of some system administrators, especially after several cybersecurity agencies warned that Fortinet devices were among the favorite entry points for obth ransomware gangs and cyber-espionage groups alike.
A list of the IP addresses for the 22,500 Fortinet SSL-VPN devices shared as part of the smaller sample leaked on the dark web earlier this week is available on GitHub, stripped of any credentials, which would allow Fortinet device owners to test if their systems were included on this leak.
The Record has not named the hacking forum and ransomware gang who leaked this information because we are aware that the group had tried to use the leak to create awareness for their "services" and drive new users to their sites. Some of the group's members gleefully rejoiced earlier when their leak was covered by several news outlets earlier this week and their names were mentioned.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.