Facebook will let bug hunters submit joint reports
Social media giant Facebook updated today its bug bounty program to allow security researchers to submit joint reports and split bug bounty payouts.
Facebook said it introduced the new feature, which it calls Researcher Collaboration Payouts, to allow researchers to work in groups and benefit from each other skillsets in order to discover complex vulnerabilities in its platforms.
"To make collaboration among researchers easier, our program now supports splitting bounty payouts between multiple researchers on one submission," the Facebook security team said today.
Facebook said it decided to roll out this feature on its primary bug bounty platform after it saw researchers collaborate with great results at its annual BountyCon events.
Instead of working alone, several researchers worked together and found "complex bug chains with higher security impact that individual researchers may not have noticed," Facebook said today.
The feature was announced earlier today and is already live in the Facebook bug bounty portal.
The feature can be enabled from the "Collaboration Settings" section in the researcher's account settings.
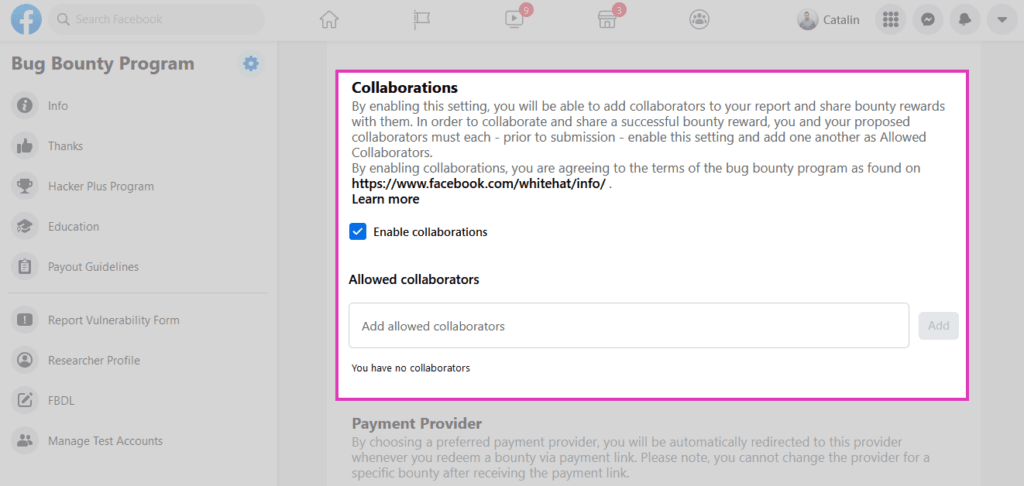
Once enabled, researchers will be able to add one or more collaborators. Each collaborator on a submission must allow each of the other collaborators within their Researcher Settings, Facebook said.
"Once this is done, an individual can act as the submitter and add up to five collaborators to a report submission. The submitter must nominate the percentage of the total reward to be issued to each collaborator if the report results in a bounty payout," Facebook added.
The ability to submit joint bug reports isn't new, and bug bounty platforms like HackerOne and Bugcrowd have similar features, John Jackson, a senior penetration tester at Trustwave, told The Record earlier today.
Last month, Facebook rolled out another interesting update to its bug bounty program, announcing that the company would pay extra for bugs that take its engineers longer to fix.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.