DOJ officials say they recovered most of the Colonial ransomware payment
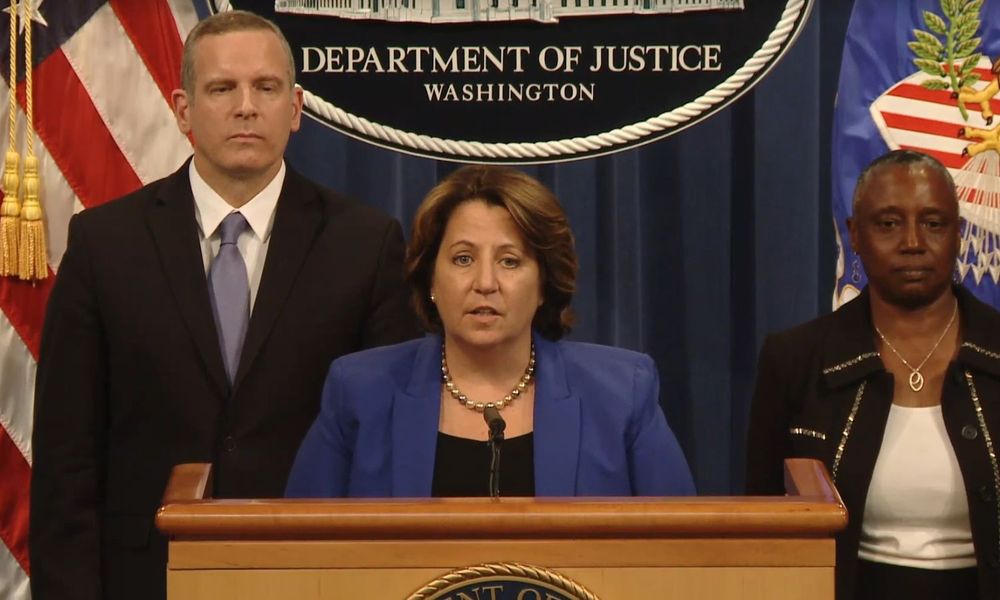
In a video press conference today, US officials said they recovered the vast majority of the $4.3 million that Colonial Pipeline paid to a ransomware gang last month after the hackers encrypted its IT network in a security incident that disrupted fuel supply for the entire US East Coast.
"After Colonial Pipeline's quick notification to law enforcement, and pursuant to a seizure warrant issued by the United States District Court for the Northern District of California earlier today, the Department of Justice has found and recaptured the majority of the ransom Colonial paid to the Dark Side Network in the wake of last month's ransomware attack," said Lisa Monaco, Deputy Attorney General for the US Department of Justice.
According to court documents, officials said they recovered 63.7 Bitcoin out of the 75 Bitcoin payment that Colonial Pipeline sent to the Darkside ransomware gang in early May.
The recovered sum, seized from this Bitcoin account, represents around 85% of the initial ransom payment, which is around the sum that a Darkside affiliate group would keep from the ransom payment, with the rest going to the creators and operators of the Darkside ransomware-as-a-service (RaaS) platform.
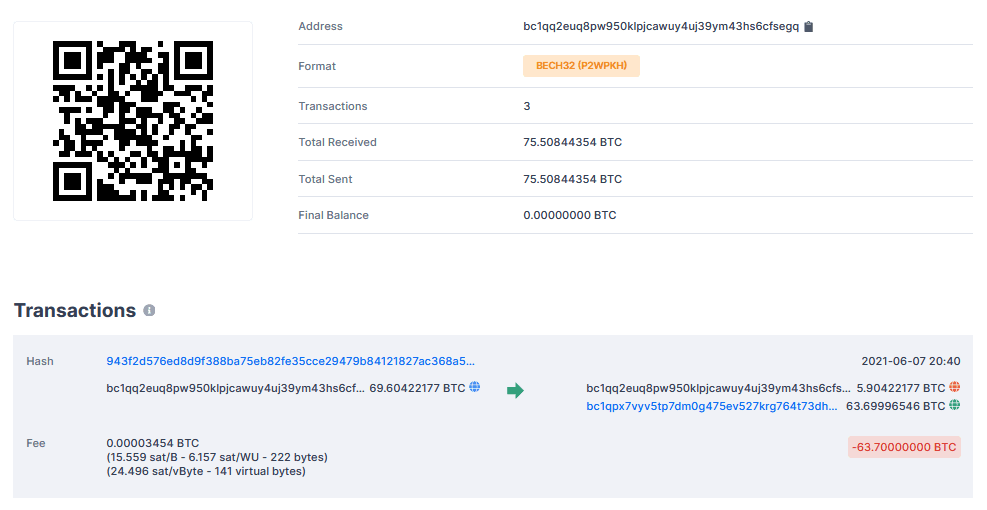
FBI investigators said they tracked the ransom payment across multiple Bitcoin addresses, as the Darkside group moved funds around. They were able to seize the funds after they gained access to one account's private key, which acts as a password for that account.
It is unclear if the FBI received the private key from the Darkside gang or if it was obtained by a third-party and delivered to investigators. On May 14, last month, a week after their attack on Colonial Pipeline, the Darkside gang reported losing control over their servers and Bitcoin stashes.
First major case for the DOJ's new Ransomware Task Force
"The seizure announced today was conducted as part of the Department's recently launched Ransomware and Digital Extortion Task Force, which was established to investigate, disrupt and prosecute ransomware and digital extortion activity," Monaco said.
"This is the Task Force's first operation of this kind," the DOJ DAG added.
In a secret memo sent last week describing the new Ransomware and Digital Extortion Task Force, Monaco instructed federal prosecutors across the US to prioritize and report ransomware incidents "in the same way that we report critical threats to our national security."
FBI Deputy Director Paul Abbate said the FBI is currently tracking more than 100 ransomware gangs that have carried out attacks against US companies, including the Darkside group, which they believe operates out of Russia.
US officials have started paying attention to ransomware attacks last month after two high-profile incidents against Colonial Pipeline and JBS Foods, which disrupted fuel and meat supply across the US.
Following these two incidents last week, the White House National Security Council issued an advisory urging companies to take measures to safeguard their networks against the ever-growing threat coming from ransomware gangs, most of which have operated with impunity and have become more brazen and destructive in recent years.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.