Cisco: InterPlanetary File System seeing ‘widespread’ abuse by hackers
A new web3 technology is being abused widely by threat actors, according to security researchers from tech giant Cisco.
The InterPlanetary File System (IPFS) is a protocol and peer-to-peer network for storing and sharing data. It is designed to enable decentralized storage of resources on the internet. It was built to be resilient against content censorship, meaning that it is not possible to effectively remove content from within the IPFS network once it’s stored there.
But Cisco Talos researchers said they are seeing “widespread abuse” and have observed “multiple ongoing campaigns that leverage the IPFS network to host their malware payloads and phishing kit infrastructure while facilitating other attacks.”
“IPFS is often used for legitimate purposes, which makes it more difficult for security teams to differentiate between benign and malicious IPFS activity in their networks,” the researchers said.
“Multiple malware families are currently being hosted within IPFS and retrieved during the initial stages of malware attacks.”
The team that runs IFPS did not respond to requests for comment.
According to Cisco Talos, IPFS is currently being leveraged to host phishing kits, which are the websites that phishing campaigns typically use to collect and harvest credentials from unsuspecting victims.
Hackers are also using the technology in their malware distribution campaigns because it provides low-cost storage for malicious payloads while offering resilience against content moderation, effectively acting as “bulletproof hosting” for adversaries.
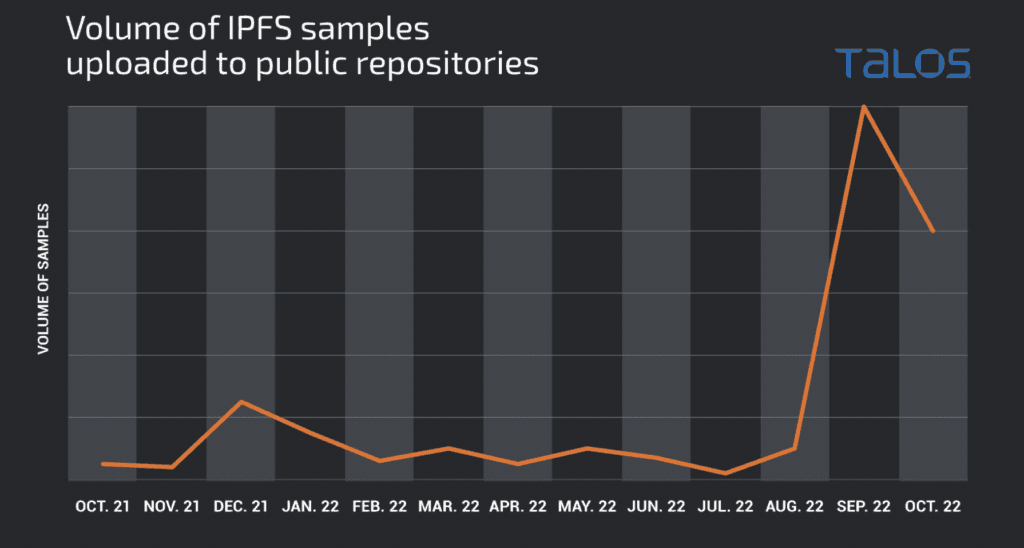
“We have observed various samples in the wild that are currently leveraging IPFS. Throughout 2022, we’ve observed the volume of samples in the wild continuing to increase as this becomes a more popular hosting method for adversaries,” the researchers said.
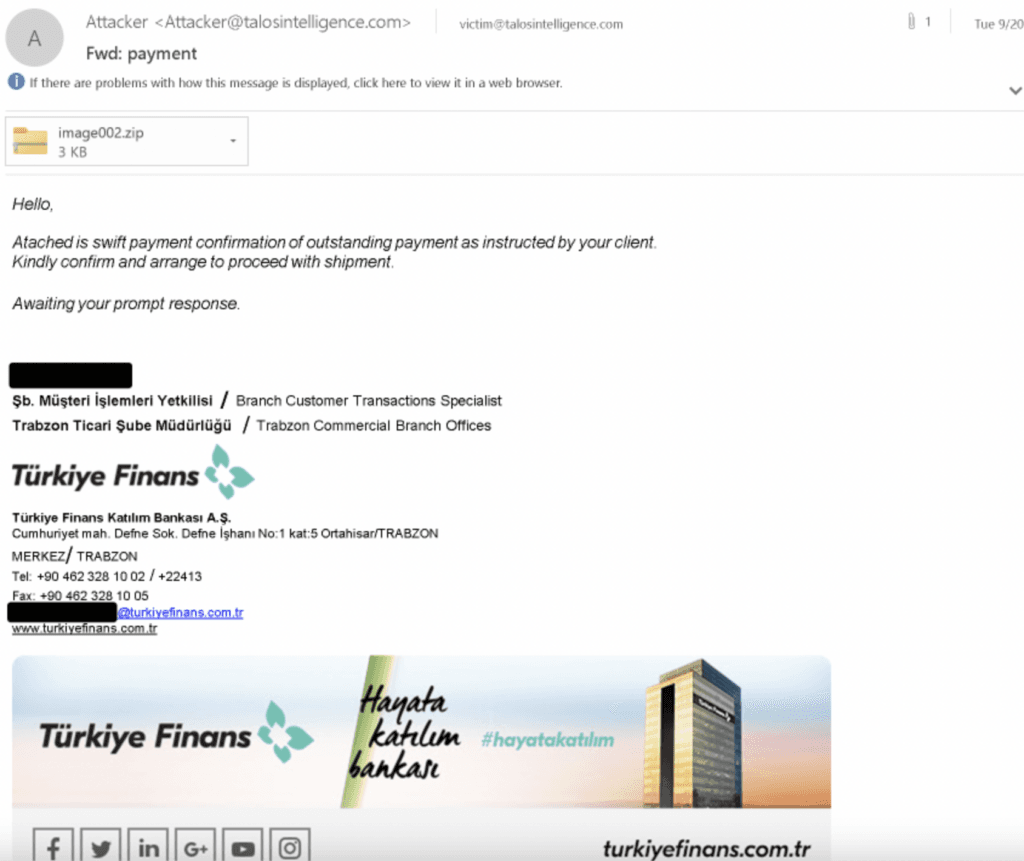
One campaign saw victims receive emails pretending to come from a Turkish financial institution that were actually part of an infection process for the Agent Tesla remote access trojan.
Several other information-stealing tools were also seen leveraging IFPS, according to Cisco Talos.
The company said it expects this kind of activity to continue increasing as more threat actors “recognize that IPFS can be used to facilitate bulletproof hosting, is resilient against content moderation and law enforcement activities, and introduces problems for organizations attempting to detect and defend against attacks that may leverage the IPFS network.”
“Organizations should be aware of how these newly emerging technologies are being actively used across the threat landscape and evaluate how to best implement security controls to prevent or detect successful attacks in their environments,” Cisco Talos said.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.