Log4Shell, ProxyLogon and Atlassian bug top CISA's list of routinely exploited vulnerabilities in 2021
The Cybersecurity and Infrastructure Security Agency (CISA) urged companies and other organizations Wednesday to take a long, hard look at its list of the top 15 routinely exploited vulnerabilities in 2021.
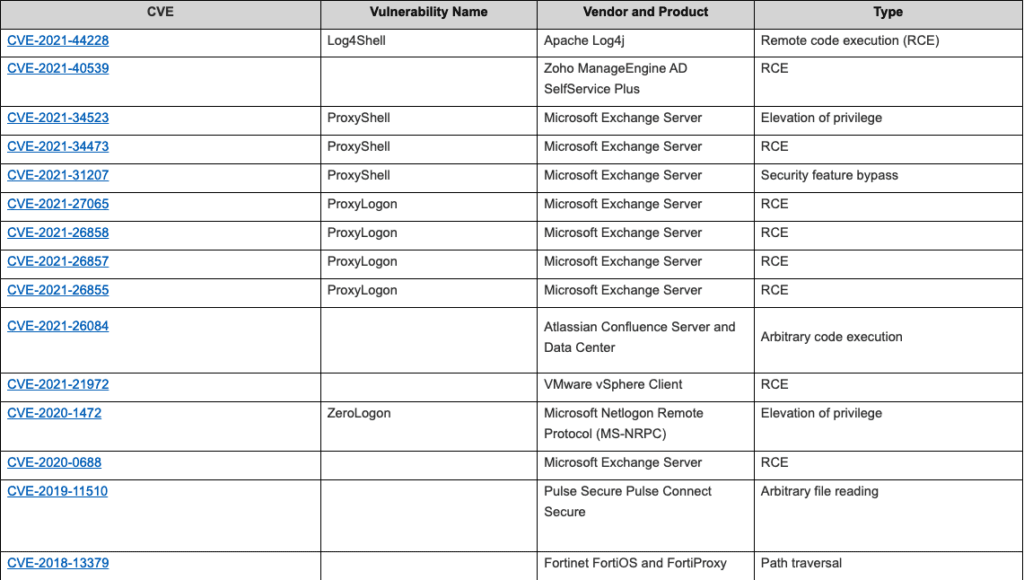
Log4Shell, Microsoft bugs ProxyLogon and ProxyShell as well as a vulnerability affecting Atlassian products topped the list.
“We know that malicious cyber actors go back to what works, which means they target these same critical software vulnerabilities and will continue to do so until companies and organizations address them,” CISA Director Jen Easterly said in a statement.
“CISA and our partners are releasing this advisory to highlight the risk that the most commonly exploited vulnerabilities pose to both public and private sector networks,” Easterly said.
We know these CVEs were frequently exploited in 2021, including some disclosed in 2020 or earlier. Mitigate and patch. These are the unlocked doors! https://t.co/LjMkdqaIVo
— Rob Joyce (@NSA_CSDirector) April 27, 2022
CISA published the list alongside cyber agencies from the other countries in the Five Eyes intelligence partnership.
The National Security Agency (NSA), Federal Bureau of Investigation (FBI), Australian Cyber Security Centre (ACSC), Canadian Centre for Cyber Security (CCCS), New Zealand National Cyber Security Centre (NZ NCSC), and the United Kingdom’s National Cyber Security Centre (NCSC-UK) worked alongside CISA to compile the list.
CISA noted that three of the top 15 routinely exploited vulnerabilities were also routinely exploited in 2020: CVE-2020-1472 which affects Windows products; CVE-2018-13379, which affects networking equipment vendor Fortinet; and CVE-2019-11510, which impacts Pulse Secure products.
The government agencies explained that for most of the top exploited vulnerabilities, researchers or other actors released proof-of-concept code within two weeks of the vulnerability’s disclosure, which they believe was “likely facilitating exploitation by a broader range of malicious actors.”
When asked whether CISA wanted researchers and analysts to stop releasing proof-of-concept code or wait a certain period of time, a CISA spokesperson told The Record that proof of concept code "provides a net benefit to network defenders, allowing them to validate patches and test mitigations."
"CISA recommends researchers and analysts wait at least two weeks to release proof of concept code, as observations indicate they can be exploited by malicious actors if released before mitigations are widely available or implemented," the spokesperson said.
CVE-2021-26084 — the Atlassian bug — was cited as one instance where a proof of concept was released within a week of its disclosure, quickly making it one of the most routinely exploited vulnerabilities.
“Attempted mass exploitation of this vulnerability was observed in September 2021,” the notice explained.
In addition to the much-discussed, widely abused Log4j vulnerability and the Microsoft Exchange email server bugs, the top 15 list includes CVE-2021-40539 and CVE-2021-21972, remote code execution (RCE) vulnerabilities affecting products from Zoho and VMware.
The Zoho vulnerability was used in the headline-grabbing attack on The Red Cross last year.
“We are seeing an increase in the speed and scale of malicious actors taking advantage of newly disclosed vulnerabilities,” said Lisa Fong, Director of the New Zealand Government Communications Security Bureau’s National Cyber Security Centre (NCSC).
She added that the advisory “underscores the importance of addressing vulnerabilities as they are disclosed.”
Vulnerabilities affecting Microsoft Netlogon Remote Protocol (MS-NRPC), Microsoft Exchange Server, Pulse Secure Pulse Connect Secure, Fortinet FortiOS and FortiProxy rounded out the list.
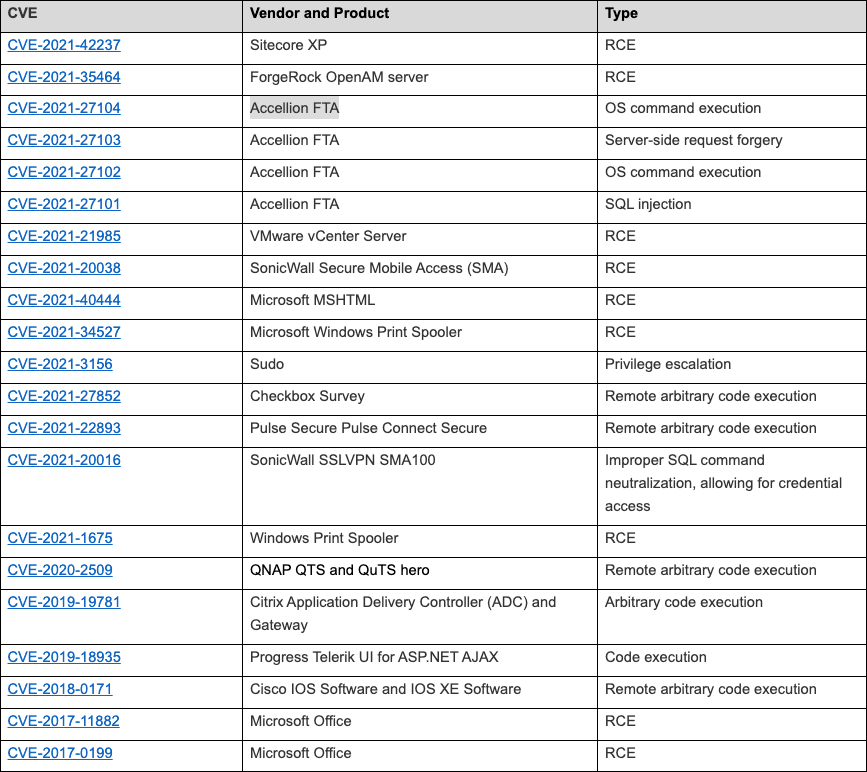
The government agencies included a second list of other vulnerabilities they saw being routinely exploited in 2021 that included bugs in products from Accellion, SonicWall, Sudo, Checkbox Survey, QNAP and Citrix.
"This report should be a reminder to organizations that bad actors don't need to develop sophisticated tools when they can just exploit publicly known vulnerabilities," said NSA Cybersecurity Director Rob Joyce. "Get a handle on mitigations or patches as these CVEs are actively exploited.”
The notice includes links to patches for all of the vulnerabilities and mitigation steps organizations should take.
In recent weeks, several cybersecurity firms have warned that Log4Shell is still an issue despite the global campaign to patch the vulnerability after it first emerged in December.
This morning, Symantec said an unnamed engineering company with energy and military customers was hacked by the North Korean government using the Log4j vulnerability.
Yotam Perkal, vulnerability researcher at cybersecurity firm Rezilion, released a report that found 55% of applications contain an obsolete version of Log4j in their latest versions.
About 90,000 machines and 68,000 public-facing internet servers are still vulnerable to Log4Shell, according to Perkal, who added that the time to patch the vulnerable containers exceeded 100 days and on average took 80 days.
David Wolpoff, CTO of security company Randori, told The Record that Log4j "was one of the worst vulnerabilities I’ve seen in my career, and no doubt will have long-lasting impacts."
"The breadth of the issue and the difficulty in determining what was affected means that this will have a long tail to it," Wolpoff explained.
"Many of the impacted applications were also really critical applications: Vmware Horizon provides virtualized desktops; Jamf and Mobileiron provide device management (sometimes fleet-wide).
Cyber insurance company Coalition also shared data showing how the Microsoft Exchange vulnerabilities impacted cyber claims last year. Of their policyholders, 1,000 were exposed during the initial set of Exchange vulnerabilities.
Organizations with less than $25 million in revenue that used Microsoft Exchange had a 103% increase in claims relative to organizations that didn’t use the tool.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.