CISA adds Spring4Shell vulnerability, Apple zero-days to exploited catalog
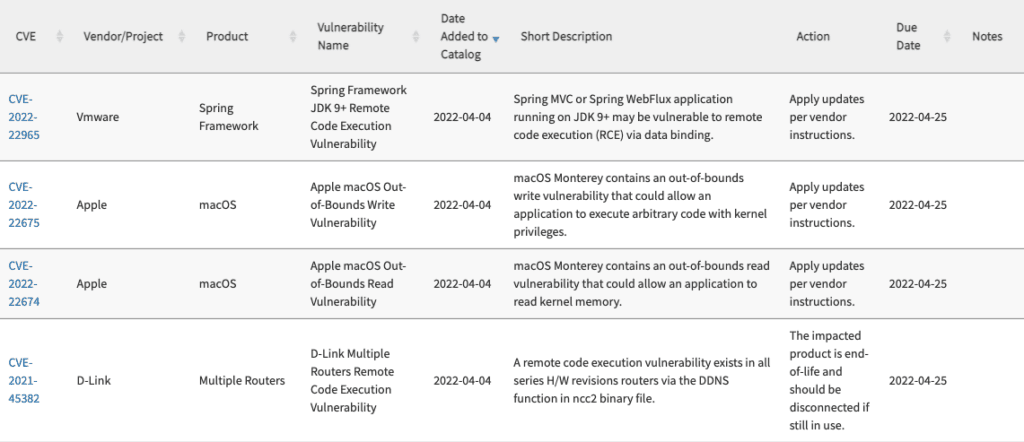
The Cybersecurity and Infrastructure Security Agency (CISA) added four new vulnerabilities to its catalog of exploited bugs, including the much-discussed “Spring4Shell” remote code execution (RCE) vulnerability.
In addition to the CVE-2022-22965 affecting the Spring Framework, CISA included CVE-2022-22675 and CVE-2022-22674, two vulnerabilities affecting macOS Monterey.
The fourth is CVE-2021-45382 – a remote code execution vulnerability affecting D-Link routers.
All four have a remediation date of April 25 and come just days after CISA added seven other bugs to the list, which is compiled based on evidence of active exploitation.
The Spring Framework affected by CVE-2022-22965 provides tools and utilities for Java-based enterprise applications, effectively serving as important “plumbing” used in Java web applications to help reduce the amount of effort required to produce a working application.
On March 31, the company confirmed the zero-day vulnerability and released a patch addressing the issue.
Security company Sonatype noted this week that even though a patch has been released, more than 80% of recent downloads are of potentially vulnerable versions. Cybersecurity company Kasada also found that cybercriminals are using automated vulnerability scanner tools to test thousands of URLs and identify which systems haven’t been patched yet.
The Apple vulnerabilities were highlighted by the tech giant last week. Apple released fixes for both of the zero days but noted that they “may have been actively exploited.”
In its notice, CISA said the D-Link routers impacted by the remote code execution vulnerability cannot be updated because they are end-of-life devices. They urged users to disconnect them if they are still used.
Valtix security researcher Davis McCarthy said that when the routers hit end of life in December 2021, they “became a prime target for exploit development due to the fact they are Internet-facing, always on, and won't receive updates.”
“Compromised routers are frequently used by threat actors to obfuscate their location while launching attacks,” he said.
Hard to remediate
Viakoo CEO Bud Broomhead told The Record that the Spring4Shell and D-Link vulnerabilities stood out most to him as issues that required significant attention and effort.
“Open source vulnerabilities by their nature (like Spring4Shell) are hard for organizations to remediate, especially with manual methods, because of the widespread use of Spring in Java development. Likely this vulnerability will remain exploitable for some time as it requires many organizations to take action to remediate it,” Broomhead said.
“End of life products, like last week’s Dasan routers or this week’s D-Link routers, are also difficult to quickly remediate because these products are widespread, and like many IoT devices often get ‘lost’ within an organization.”
Vulcan Cyber’s Mike Parkin noted that it was interesting the Apple vulnerabilities were added to the list so quickly but said it was likely included due to the “heightened cybersecurity threats posed by the conflict in Ukraine.”
Exploit brokers are willing to pay into the millions for an RCE zero-day and usually do so by the product or operating system, according to McCarthy, who added that the issues impacting Apple products would be “lucrative.”
“If CISA is reporting wide-spread exploitation, it's possible this zero-day was sold to many users, or sold in a pre-packaged exploit kit made available in an underground marketplace,” McCarthy said.
“When paired with CVE-2022-22674, which allows reading from memory in macOS, an adversary could obtain a lot of sensitive information from their target.”
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



