AirDrop bugs expose Apple users' email addresses, phone numbers
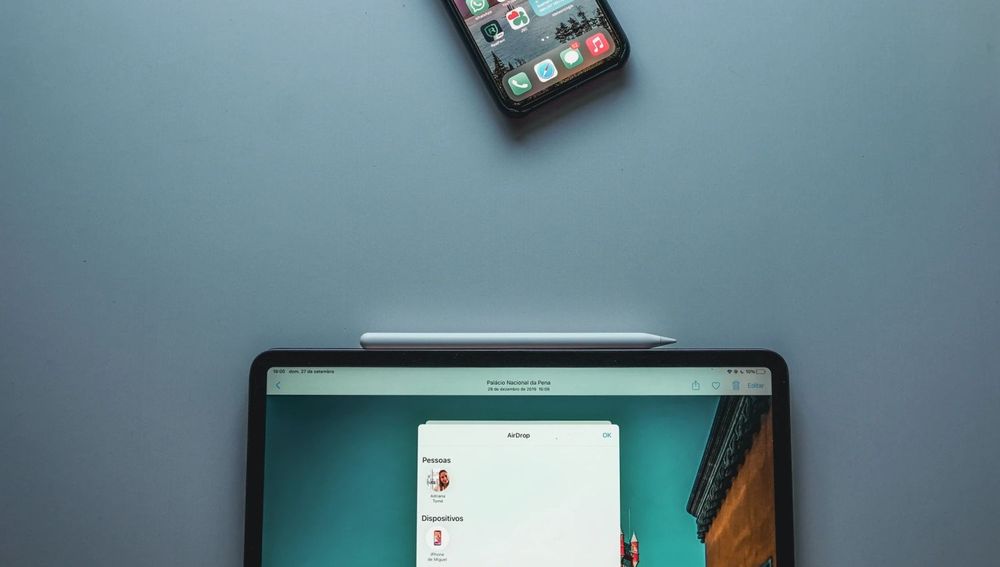
A team of academics from a German university said it discovered two vulnerabilities that can be abused to extract phone numbers and email addresses from Apple's AirDrop file transfer feature.
The two bugs reside in the authentication process during the initial phase of an AirDrop connection, where devices try to discover each one another and determine if they belong to users who know each other (by checking if a device/user's phone number is in the other device's contacts list).
Under the hood, the Apple devices exchange AWDL (Apple Wireless Direct Link) packets that contain information about the devices and their owners, such as technical specs and personal data, including phone numbers, Apple IDs, or email addresses.
To protect the data from being intercepted, Apple scrambles these details with a SHA256 hashing function.
But academics from the Technical University of Darmstadt in Germany said that if AirDrop is enabled on an Apple system, the device broadcasts these discovery packets in all directions and at all times.
A threat actor in close physical proximity (Bluetooth range) to a target can use an off-the-shelve WiFi card to intercept these messages and then crack parts of the hashed data to recover various personal details.
Apple has known of these issues since May 2019
In 2019, this research team published a first paper [PDF] where they described various methods to recover details from an AirDrop connection, such as phone status, WiFi status, OS version, buffer availability, and others.
Today, the same research team published a second paper [PDF] where they extended their original work to show how additional details like phone numbers and email addresses can also be recovered.
The research team said it notified Apple of their findings on two occasions, in May 2019 and October 2020, and even suggested a new custom PrivateDrop protocol to prevent these leakages, but have yet to receive an answer from Apple if the company plans to fix any of the reported problems.
More than 1.5 billion Apple devices currently support AirDrop connections. The issues most likely also impact AirPlay connections, which also use the AWDL protocol and similar discovery procedures.
Reached out via email, Apple did not wish to comment.
The Darmstadt team plans to present their findings later this year, in August, at the USENIX security conference.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.