Researchers warn of hackers widely exploiting bug in Zyxel hardware
A critical vulnerability affecting Zyxel firewalls is being widely exploited by hackers, according to a report published this week by cybersecurity firm Rapid7.
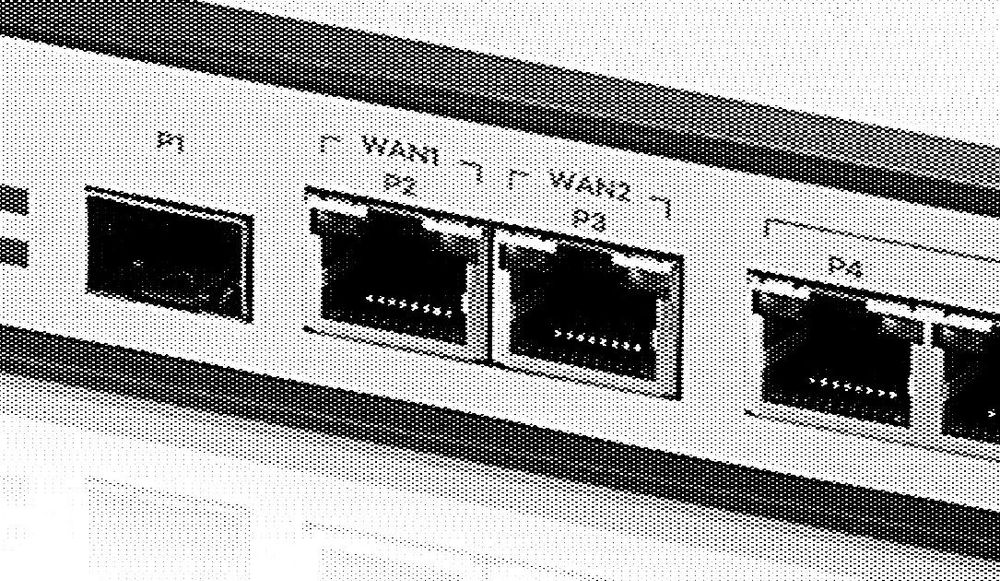
The vulnerability, tracked as CVE-2023-28771, is exploitable in the wide area network (WAN) interface, a port on a device that connects it to the internet. WAN interfaces are commonly found on devices such as routers, switches, and network appliances.
It’s the latest in a series of bugs found in products from Taiwan-based Zyxel, which sells networking hardware and other services, typically to small- and medium-sized organizations.
According to Rapid7, the current vulnerability exists in the default configuration of exploitable devices, and a device does not need to have a VPN configuration to be vulnerable. Successful exploitation of the bug allows hackers to execute malicious code remotely on the target system to install malware.
As of the end of May, the Zyxel vulnerability had been widely used to compromise devices to carry out further attacks through a version of the notorious Mirai botnet, according to Rapid7. Mirai is commonly used to launch distributed denial of service (DDoS) attacks, but is capable of other tasks, too.
Zyxel released patches for CVE-2023-28771 in April and urges users to install them for protection. On Wednesday, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) also published an alert warning that the Zyxel vulnerability is being actively exploited by attackers, urging federal agencies to apply the available update by June this year.
“These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise,” the agency said.
Zyxel has recently fixed two other critical severity flaws, CVE-2023-33009 and CVE-2023-33010, which impact the same firewall and VPN products. These vulnerabilities allow hackers to either cause a denial-of-service situation or run any code they want on the devices that are affected, according to Rapid7. The company drew attention for another bug about a year ago.
Attacks against firewall devices are common. They have been carried out by both cyber-espionage and financially motivated groups. Vendors that had enterprise firewalls abused this way recently include Pulse Secure, Palo Alto Network, Fortinet, Citrix and Cisco.
In March, for example, a suspected state-sponsored hacking group based in China exploited zero-day vulnerabilities in Fortinet firewalls and deployed custom malware to spy on defense, government, tech and telecom organizations. In April, tech giant Cisco warned about attacks on routers allegedly being exploited by Russian military hackers.

Daryna Antoniuk
is a reporter for Recorded Future News based in Ukraine. She writes about cybersecurity startups, cyberattacks in Eastern Europe and the state of the cyberwar between Ukraine and Russia. She previously was a tech reporter for Forbes Ukraine. Her work has also been published at Sifted, The Kyiv Independent and The Kyiv Post.