Zerodium acquiring zero-days in Pidgin, an IM client popular with cybercriminals
Exploit broker Zerodium announced plans today to pay up to $100,000 for zero-days in Pidgin, a multi-protocol instant messaging desktop client and a popular IM tool used in cybercriminal circles.
"We are looking for remote code execution exploits affecting the latest version of Pidgin on Windows and/or Linux," the company said in a message posted on its website today.
"The exploit should work with default installations and should not require any user interaction other than reading a message."
The company, which buys exploits from security researchers and sells them to government and law enforcement agencies, said it would buy Pidgin zero-days at the higher $100,000 price for the next three months, until August 2021, in what the company described as a temporary bug acquisition drive.
The company used acquisition drives in previous years to fill voids in its exploit portfolio or after its customers requested certain vulnerabilities for ongoing operations.
Pidgin has been a popular IM client with cybercrime gangs
But while the Pidgin app has its legitimate use cases, it is almost a given that Zerodium's interest in acquiring Pidgin zero-days comes from the app's broad use in the cybercriminal underground.
Even if the app can be used with several instant messaging (IM) protocols, its primary use case over the years has been to allow users to exchange messages via the XMPP (Jabber) protocol.
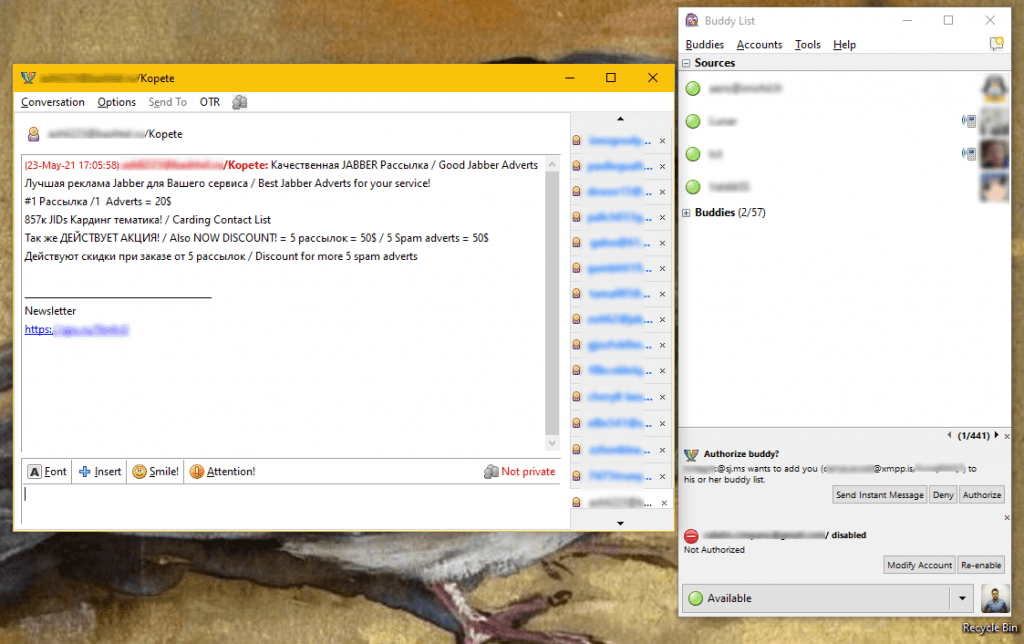
Cybercriminals preferred it because they could register an XMPP/Jabber ID on a secure server that did not save logs and use the ID to reach out and talk to each other to arrange operations or business deas.
To preserve the security of their conversations, criminal groups and underground communities often required each other to use OTR (Off The Record) or GnuPG encryption plugins, Recorded Future threat intelligence analyst Dmitry Smilyanets told The Record in an interview today.
"Cybercriminals shifted from ICQ towards Jabber (XMPP) in the early 2000s," Smilyanets said.
But while Smilyanets said that "having 'zhaba' was a must-have for anyone" in the past, Pidgin and XMPP/Jabber, in general, have been slowly losing ground to new instant messaging services in recent years.
"A new generation of cybercriminals prefer Telegram for day-to-day conversations and deals these days, and TOX as the more secure and anonymous alternative," he said.
Besides Pidgin zero-days, Zerodium is also running other bug acquisition drives for the WordPress CMS and the ISPConfig web hosting panel, two tools often used in cybercrime hosting infrastructure.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.



