YouTube channels found using pirated video games as bait for malware campaign
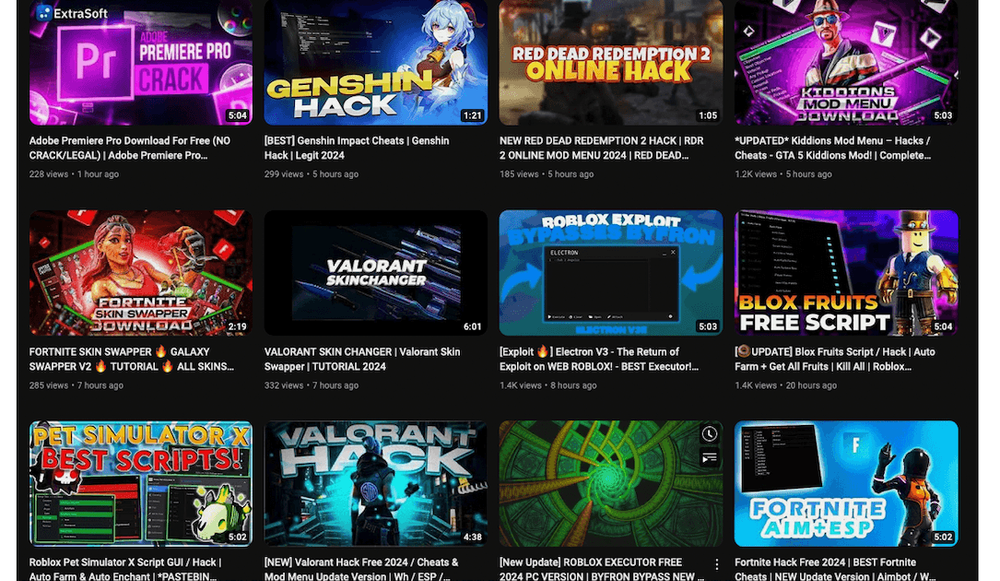
Hackers are distributing malware through multiple YouTube channels that promote cracked or pirated video games, according to researchers at Proofpoint.
In a report released on Wednesday, the cybersecurity company said it has been tracking a campaign where hackers put links in YouTube video descriptions allegedly taking victims to other sites where information-stealing malware like Vidar, StealC and Lumma Stealer can be delivered.
“The videos purport to show an end user how to do things like download software or upgrade video games for free, but the link in the video descriptions leads to malware,” the researchers explained.
The recent campaign is the latest example of how the popular Google-owned video platform can be leveraged by threat actors, including cybercriminal groups and even state-backed operations.
In this case, many of the accounts “appear to be compromised or otherwise acquired from legitimate users, but researchers have also observed likely actor-created and controlled accounts that are active for only a few hours, created exclusively to deliver malware,” Proofpoint said. “Third-party researchers have previously published details on fake cracked software videos used to deliver malware.”
Selena Larson, senior threat intelligence analyst at Proofpoint, noted that while there were a variety of different video games used as lures to get people to click on the malicious URL, many were popular with younger people, including children.
The possibility that threat actors could impact kids’ online experiences is very concerning, Larson warned, noting that it’s also likely that children have less experience with identifying potentially malicious content and have a higher likelihood of interacting with it.
“It’s also likely most of these threats would impact consumers playing on home computers, and these would have lots of personal and sensitive information that a threat actor could then use for financial gain,” she explained.
Proofpoint reported more than 24 accounts and videos distributing malware and YouTube promptly removed them.
YouTube told Recorded Future News that it has policies in place banning users from putting content in the description boxes that violates the platform’s community guidelines. This includes malware, a spokesperson explained.
The YouTube official explained that the platform uses “a combination of machine learning and human review” to enforce its policies, and the systems “proactively monitor videos and livestreams to detect and remove deceptive behavior.”
In Q4 of 2023, YouTube removed more than 20.5 million channels for violating Community Guidelines.
“The overwhelming majority of these channels were terminated for violating our spam policies. YouTube removed more than 1.1 billion comments in Q4 2023, the majority of which were spam. 99+% of removed comments were detected automatically,” the spokesperson said.
MediaFire and Discord
Proofpoint mostly saw malware being distributed through MediaFire URLs that had malicious files but the researchers also identified instances where hackers put Discord links into a video description. The Discord channels linked had files available for download that contained the malware.
In one example, an account with about 113,000 subscribers was either compromised or sold to a threat actor who began using it maliciously, Proofpoint said. The account previously published videos in Thai but went dormant for about one year. After that gap in time, 12 new videos were posted in English, all within 24 hours and all related to video games or software cracks.
The account was also verified with a gray check mark — lending it credibility with users. Each of the videos had descriptions with links to malicious content.
According to Proofpoint, some of the videos had more than 1,000 views, but the researchers are unsure if the view counts are legitimate or inflated through bots.
Another example shared by the cybersecurity firm involved a video offering gamers enhancements for their in-game characters. In the description was a MediaFire link that took victims to a file that downloaded and installed Vidar Stealer malware.
Multiple comments on the video attested to the legitimacy of the video’s offering and Proofpoint said it believes the accounts were created to rubber stamp the malicious links.
In several other examples found by the researchers, the videos offered users access to Empress — a video game cracker who specializes in breaking anti-piracy software. One video offered “cracked” versions of the League of Legends game that had links to files named “empress.exe.” The file was actually the Vidar Stealer malware.
Difficult to attribute
Proofpoint was not able to identify the hackers behind the campaign and could not attribute it to any tracked threat actor or group, noting that the activity was bunched into multiple distinct clusters.
“The techniques used are similar, however, including the use of video descriptions to host URLs leading to malicious payloads and providing instructions on disabling antivirus, and using similar file sizes with bloating to attempt to bypass detections,” they said.
“Based on the similarities of the video content, payload delivery, and deception methods, Proofpoint assesses that the actors are consistently targeting non-enterprise users.”
The researchers are not sure how many YouTube accounts may be compromised.
The hackers were targeting video game players because they typically “do not have the same resources or knowledge to defend themselves from attackers compared to enterprises,” the researchers said.
Even though most of the compromises outlined will not lead to large financial windfalls, the video game players typically do have access to some kinds of credit cards, cryptocurrency or other personal information that could be sold.
Google’s Threat Analysis Group previously warned that hackers were reaching out to prominent YouTubers for product reviews, urging them to download apps and provide video reviews of them. The apps typically had malware attached that allowed them to steal the YouTube login credentials and take over the account.
Hackers have similarly taken over YouTube accounts to promote crypto scams or other political messages.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.