Wire Transfer Scams Are Getting More Costly
Law enforcement officials have warned companies for years about the huge losses associated with business email compromise attacks, in which criminals scam victims into making large wire transfer payments. New data suggests these attacks are getting even more costly.
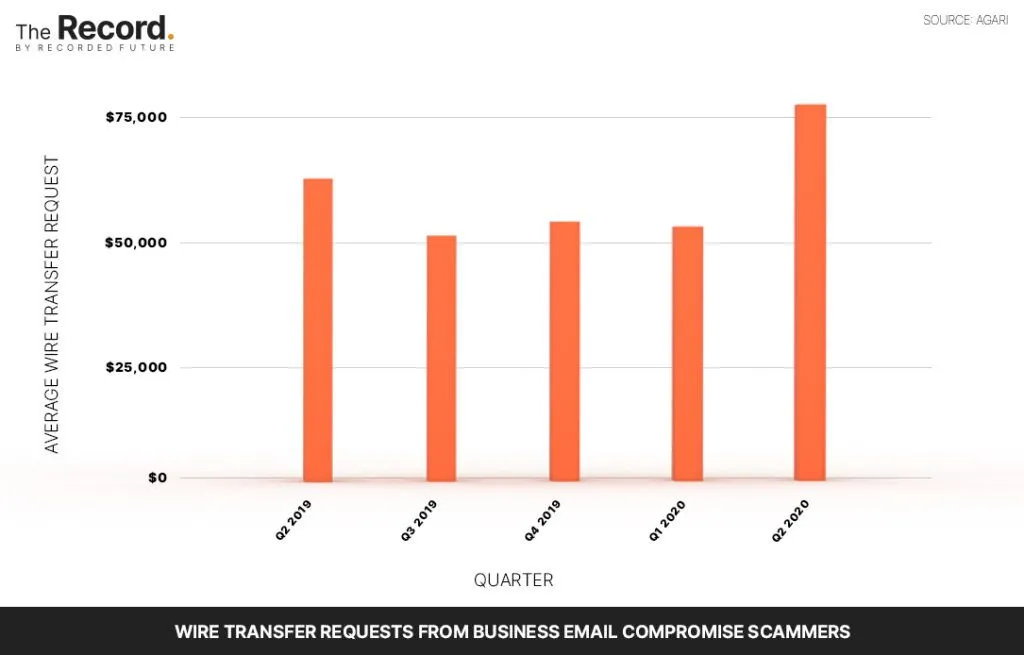
The average wire transfer attempt made by BEC scammers rose to more than $80,000 in the second quarter of 2020, up from $54,000 in the first quarter, according to a recent report from the Anti Phishing Working Group.
BEC scams can take many forms, but they generally involve impersonating an executive and sending a phishing email to an employee asking them to make a wire transfer to an account owned by the attacker. The FBI considers it one of the most financially damaging online crimes: Between June 2016 and July 2019, more than 166,000 business email compromise incidents were reported to the FBI’s Internet Crime Complaint Center totalling more than $26 billion in exposed losses.
Crane Hassold, senior director of threat research at Agari, the cybersecurity firm that conducted the recent study, said the data shows that while the average wire transfer attempt has spiked, the median attempt has remained about the same. “What that means is there’s a small number of actors asking for a substantial amount of money,” according to Hassold.
One active group in particular, called Cosmic Lynx, has been asking for wire transfers in the six and seven-figure range. The group often impersonates legitimate attorneys and crafts their attacks to look like mergers and acquisitions deals, which can net them giant payouts.
Cosmic Lynx and other BEC scammers tend to be industry agnostic, but they generally target Fortune 500 firms and other large multinational organizations that regularly make sizable wire transfers, Hassold said.
“We have sophisticated actors moving into this space and crafting their attacks in ways that allow them to ask for more money,” he said.
The FBI and financial institutions are sometimes able to recover funds if incidents are reported, Hassold said. But to prevent these incidents in the first place, organizations should have a process of verifying all wire transfer requests and other outgoing payments — for example, employees might be required to follow up email requests with a phone call, according to Hassold.
Adam Janofsky
is the founding editor-in-chief of The Record from Recorded Future News. He previously was the cybersecurity and privacy reporter for Protocol, and prior to that covered cybersecurity, AI, and other emerging technology for The Wall Street Journal.



