Windows 10, iOS 15, Ubuntu, Chrome fall at China's Tianfu hacking contest
Chinese security researchers took home $1.88 million after hacking some of the world's most popular software at the Tianfu Cup, the country's largest and most prestigious hacking competition.
The contest, which took place over the weekend of October 16 and 17 in the city of Chengdu, was won by researchers from Chinese security firm Kunlun Lab, who took home $654,500, a third of the total purse.

The competition, now at its fourth edition, took place using the now-classic rules established by the Pwn2Own hacking contest.
In July, organizers announced a series of targets, and participants had three-to-four months to prepare exploits that they would execute on devices provided by the organizers on the contest's stage.
Researchers had three 5-minute attempts to run their exploits, and they could register to hack multiple devices if they wished to increase their winnings.
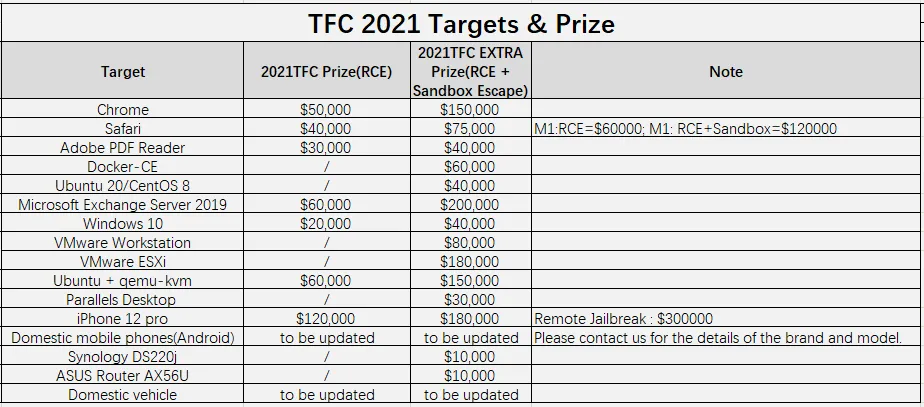
This year's edition included a list of 16 possible targets and was one of the Tianfu Cup's most successful editions, with the 11 participants mounting successful exploits against 13 targets.
The only ones that were not hacked included Synology DS220j NAS, Xiaomi Mi 11 smartphone, and a Chinese electric vehicle whose brand was never revealed — for which no participant even registered to attempt an exploit.
On the other hand, successful exploits were mounted against nearly everything else, as follows:
- Windows 10 - hacked 5 times
- Adobe PDF Reader - 4 times
- Ubuntu 20 - 4 times
- Parallels VM - 3 times
- iOS 15 - 3 times
- Apple Safari - 2 times
- Google Chrome - 2 times
- ASUS AX56U router - 2 times
- Docker CE - 1 time
- VMWare ESXi - 1 time
- VMWare Workstation - 1 time
- qemu VM - 1 time
- Microsoft Exchange - 1 time


Most of the exploits were privilege escalation and remote execution bugs; however, two exploits presented at the Tianfu Cup this year stood out.
The first was a no-interaction remote code execution attack chain against a fully patched iOS 15 running on the latest iPhone 13. The second was a simple two-step remote code execution chain against Google Chrome, something that has not been seen in hacking competition in years.
The iPhone 13 Pro Safari escaped from prison remotely, and Chian Pangu won the highest single bonus of $300000 in history.@mj0011sec pic.twitter.com/rrCa1cGcnN
— HBS (@HUC_hbs) October 16, 2021
First confirmed entry for day1 of TianfuCup, Kunlun Lab @S0rryMybad pwned Google Chrome to get Windows system kernel level privilege with only two bugs. First time since 2015 as I remembered https://t.co/xy1dTzl1GV
— mj0011 (@mj0011sec) October 16, 2021
But while the Tianfu Cup hacking contest will take all the news headlines in the coming days, the event also included a separate trade show and cybersecurity conference, which this year was keynoted by Qi Xiangdong, chairman of security firm QiAnXin, and also included sections dedicated to smart vehicle security, IoT security, artificial intelligence security, and smart city security.
However, all eyes were on this year's competition for another reason, namely that one of the iOS exploits showcased at last year's competition was used in a cyber-espionage campaign carried out by the Beijing regime against its Uyghur population.
The discovery came to reinforce the belief among western security experts that Beijing forbade Chinese security researchers from participating in hacking contests held abroad back in 2017 in order to better harness their exploit-creating capabilities for its own operations.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.


