White House blames Russia for latest digital attacks on Ukraine
A senior White House official on Friday blamed Russia’s military intelligence agency for flooding the websites of Ukrainian defense agencies and banks with phony traffic earlier this week, which briefly knocked them offline and ratcheted up fears of an invasion by Moscow.
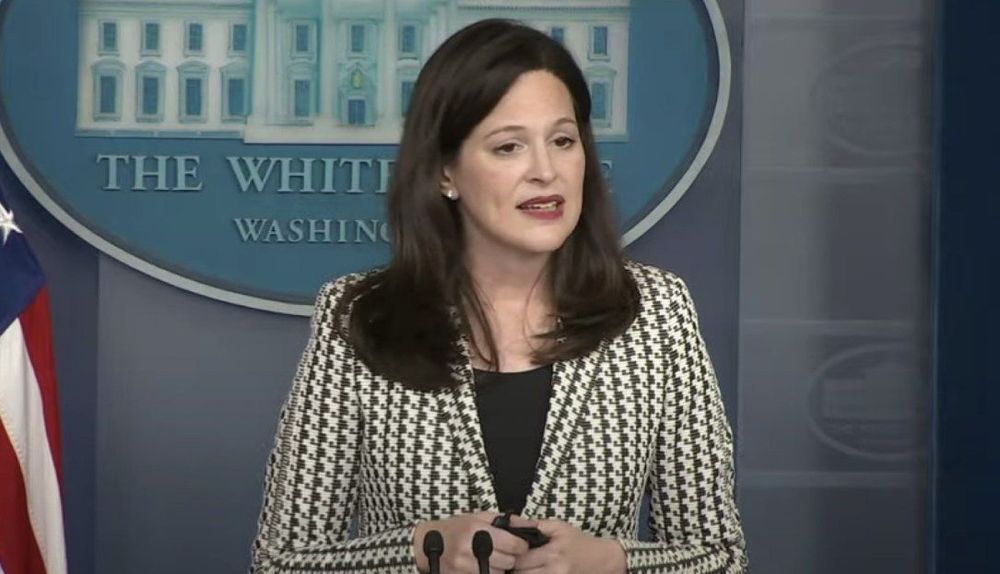
“We have assessed that Russia was responsible for the distributed denial of service attacks that occurred earlier this week,” Anne Neuberger, the deputy national security adviser for cyber and emerging technology, said during a White House press briefing.
She said the U.S. has technical information that links the Russian Main Intelligence Directorate, or GRU, to the so-called distributed denial of service (DDoS) attacks that downed the web sites for Ukraine’s Ministry of Defense and Armed Forces as well as two major banks.
Infrastructure run by the intelligence service “was seen transmitting high volumes of communication to Ukraine-based IP addresses and domains,” according to Neuberger.
The U.S. shared the intelligence supporting its attribution with Ukrainian and European partners, she added, describing the attacks as "consistent with what a Russian effort could look like in laying the groundwork" for more disruptive hacks accompanying an invasion of the former Soviet satellite state.
The incidents occurred as Russia has massed as many as 190,000 troops along Ukraine’s borders. Moscow previously claimed it was scaling back troops at the border, assertions that Western countries have found to be false.
While not as destructive as other kinds of malicious activity, DDOS attacks can have the psychological impact of undermining public confidence in institutions, both public and private. Ukrainian officials called this week's denial attacks the worst in the country’s history.
Neuberger admitted the speed of the attribution was “unusual” but that the administration went ahead “because of a need to call out the behavior quickly, as part of holding nations accountable when they conduct disruptive or destabilizing cyber activity.”
The United Kingdom quickly joined in the attribution.
"This activity is yet another example of Russia's aggressive acts against Ukraine," the country's Foreign, Commonwealth & Development Office said in a statement.
Neuberger said the U.S. also believes Russian cyber actors likely have targeted the Ukrainian government, including military and critical infrastructure networks, “to collect intelligence and pre-position to conduct disruptive cyber activities.”
She said that since November the U.S. has intensified its support of Ukraine’s government, specifically network defenders, to help them respond to and recover from cyber incidents and strengthen the resilience of the country's critical infrastructure.
Neuberger stressed that there are “currently no specific or credible cyber threats to the homeland.”
“We are confident that we have worked closely with the private sector to press critical infrastructure owners and operators in the private sector to take the necessary steps to deploy cyber defenses,” she said after being asked if the private sector is prepared for potential spillover from a digital assault on Ukraine.
Neuberger declined to discuss what kind of hacks against the U.S. or its allies might trigger a retaliatory response from Washington.
She did say that attacks against infrastructure are “of significant concern” and “outside the boundaries of international norms.”
Neuberger pointed to the power, communications and water sectors as three areas where infrastructure has “digitized quickly” and “need to catch up” in terms of security and resilience.
Martin Matishak
is the senior cybersecurity reporter for The Record. Prior to joining Recorded Future News in 2021, he spent more than five years at Politico, where he covered digital and national security developments across Capitol Hill, the Pentagon and the U.S. intelligence community. He previously was a reporter at The Hill, National Journal Group and Inside Washington Publishers.