West conducting cyber ‘sabotage’ on Russia, deputy foreign minister claims
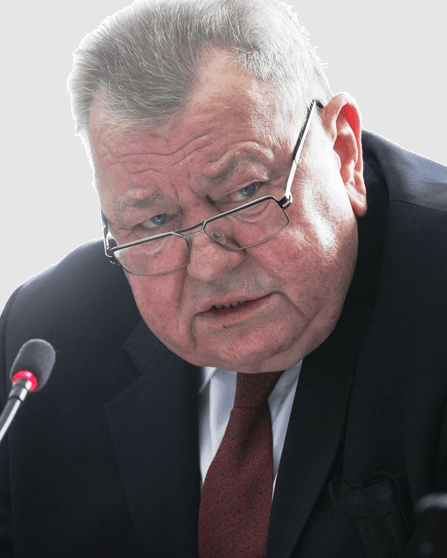
The United States and European Union are conducting a campaign of cyber “sabotage” against Russia, the country’s deputy foreign minister Oleg Syromolotov claimed on Thursday.
Cyberattacks against Russian “information resources and infrastructure facilities have increased significantly,” he said, since the beginning of its invasion of Ukraine. Syromolotov, a former deputy director and counterintelligence chief for the FSB, told the state-owned news agency RIA Novosti “the countries of North America and the European Union” are to blame.
Though Syromolotov was scant on details of attacks, his claims of an uptick in cyberattacks on the country reflect recent research from cybersecurity firms. Slovakia-based ESET, for example, recently found that Russia was the country most targeted with ransomware at the start of 2022.
Syromolotov said the Pentagon and the National Security Agency “boast that they are conducting offensive operations against other independent states under the pretext of protecting 'democracy', human rights” — a claim which misrepresents an interview with NSA chief General Paul Nakasone in which he said that U.S. Cyber Command has “conducted a series of operations across the full spectrum; offensive, defensive, [and] information operations.” Syromolotov did not attribute any specific incident inside Russia to the U.S.
“Sophisticated cyber means are used to mislead our citizens, to discredit the actions of the Armed Forces of the Russian Federation and government bodies,” he said. “Recently, experts from the Harvard Kennedy School recognized that the United States is the world leader in propaganda and the spread of lies,” he added, although it’s unclear what he was referring to.
The Record has asked a Russian Ministry of Foreign Affairs spokesperson whether he was speaking about a recent collaboration between Stanford Internet Observatory and Graphika which identified a relatively unsuccessful pro-Western influence operation on social media.
The deputy minister also accused Western corporations, or “monopolies”, of involvement “in the implementation of aggressive plans.”
“At the forefront is the infamous Microsoft, which subordinates the digital independence of states to U.S. interests and thereby facilitates potential hacking operations.”
Perhaps most significantly, Syromolotov accused the U.S. military and intelligence apparatus of “encouraging Russophobia among the hacker international,” indicating that a portion of the attacks against Russia are being conducted by non-state actors.
Back in June, another MFA spokesperson, Alexander Krutskikh, said "more than 65,000 'armchair hackers' from the United States, Turkey, Georgia, and EU countries regularly took part in coordinated DDoS attacks” against Russian targets, adding “in total, 22 hacker groups are involved in illegal operations against Russia.”
The ‘armchair hackers’
Oleg Shakirov, an independent Russian researcher focusing on U.S.-Russia cyber diplomacy, who is currently a visiting scholar at Tufts University, told The Record: “Since the very start of the war Russia has been constantly under attack from pro-Ukrainian groups, the most visible (but not the most capable) among whom is IT Army of Ukraine.”
But because these incidents are sometimes unreported by the victims and also exaggerated by the hacking groups themselves, it is “hard to see the comprehensive picture” of what is taking place inside Russia, added Shakirov.
Some of the incidents were relatively simple distributed denial-of-service (DDoS) attacks, he explained, although even these can have tangible effects. “For instance a DDoS campaign against EGAIS [the Unified State Automated Information System], a system for tracing alcohol products, caused some producers to halt production lines because they could not ship their goods without sending data via EGAIS.”
In other situations the hacker groups claimed to have targeted critical infrastructure, such as in a recent attack targeting St. Petersburg’s regional energy supplier LOESK. “A group known for a RuTube hack in May claimed they managed to hack into a major power supply firm in the Leningrad region, cause some power outages and steal data,” explained Shakirov.
“LOESK put out a statement saying ‘the attack was completely neutralized’ and outages prevented. Indeed, there is no evidence so far to prove that any significant disruptions occurred. At the same time LOESK’s website was down for more than a week and clients were tasked with submitting documentation in the physical form to the firms central office rather than online.”
Ukraine’s IT Army took credit for the attack in an online video, claiming that it was conducted in response to Russian strikes on Ukrainian energy facilities, but Shakirov warned against taking this at face value.
“The video claims that the attack was carried out on October 12, after the strikes on October 10. Whereas LOESK website showed a message about the attack on October 8 and the first complaint from a client was posted on its VK discussion board on October 9.”
Pro-Ukraine hacker groups have also claimed to have bricked Russian routers alongside attacking satellites and UPS (uninterruptible power supply) systems in data centers in the country, however if these operations had any effects then they do not appear to have been reported inside Russia.
There is evidence of successful operations on the Telegram channel for the IT Army of Ukraine, a volunteer collective which has directed a range of different operations, from denial-of-service attacks against the Russian Federal Tax Service to distributing files stolen from Russian companies.
In response to a question from RIA Novosti about cyber fraud inside Russia, the deputy minister alleged that the criminal gangs behind it were "often backed by U.S. intelligence agencies and their allies", while also claiming that the “special military operation” – the invasion of Ukraine – had disrupted their ability to target Russia.
Alexander Martin
is the UK Editor for Recorded Future News. He was previously a technology reporter for Sky News and a fellow at the European Cyber Conflict Research Initiative, now Virtual Routes. He can be reached securely using Signal on: AlexanderMartin.79



