US Treasury sanctions cryptocurrency exchange linked to ransomware operations
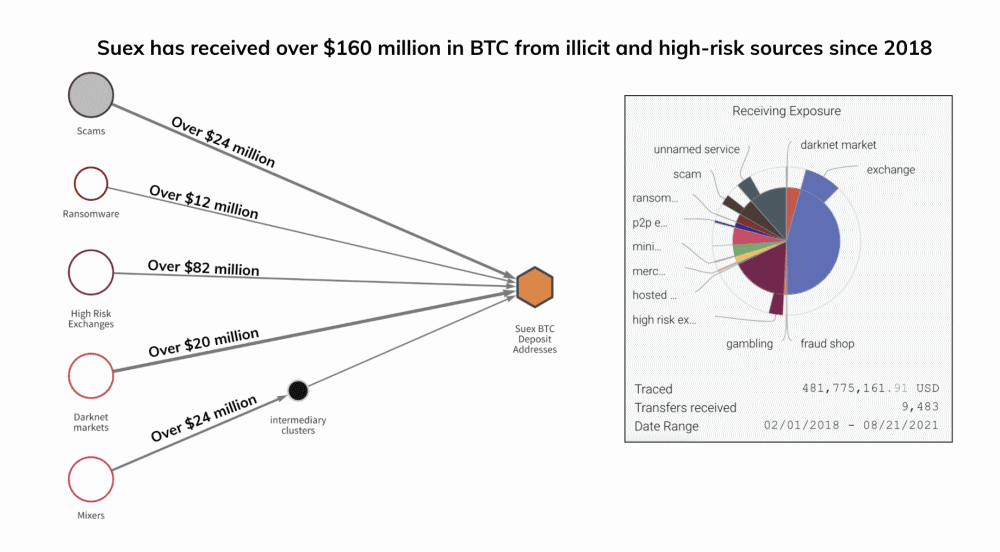
The US Treasury Department has imposed sanctions today on cryptocurrency exchange portal Suex for helping ransomware, and other cybercrime groups, launder more than $160 million in illicit funds between 2018 and 2021.
Registered in the Czech Republic but owned by Russian nationals, the exchange operated via the Suex.io website [archived] and out of headquarters in Moscow and Sankt Petersburg.
"Since opening its doors in 2018, Suex has moved hundreds of millions of dollars worth of cryptocurrency, mostly in Bitcoin, Ether, and Tether, much of which is from illicit and high-risk sources," said Chainalysis, a company that analyzes and tracks blockchain transactions.
"Suex has received over $481 million in Bitcoin alone since becoming active in February 2018, based on the value at the time of transfers," the Chainalysis team added in a report on Suex's activity published today after the Treasury sanctions.
"In Bitcoin alone, Suex's deposit addresses hosted at large exchanges have received over $160 million from ransomware actors, scammers, and darknet market operators."
More than $12 million of these transactions were linked to ransom payments made to gangs like Ryuk, Conti, Maze, and others, Chainalysis said.
The Suex portal appeared to have been set up with the primary role of helping cybercrime operators launder their profits. Despite activating for three years, the Suex portal never moved large sums of money and was so small that it never made it on the Coinmarketcap Exchange Ranking.
Treasury officials estimated that roughly 40% of all known Suex transactions have been "associated with illicit actors."
As a result of today's sanctions, the exchange's US-based assets have now been frozen, and US entities are forbidden from doing business with Suex, risking fines or sanctions themselves.
The Treasury also published a list of 25 cryptocurrency accounts known to be operated by Suex for daily transactions.
- 12HQDsicffSBaYdJ6BhnE22sfjTESmmzKx (BTC)
- 1L4ncif9hh9TnUveqWq77HfWWt6CJWtrnb (BTC)
- 13mnk8SvDGqsQTHbiGiHBXqtaQCUKfcsnP (BTC)
- 1Edue8XZCWNoDBNZgnQkCCivDyr9GEo4x6 (BTC)
- 1ECeZBxCVJ8Wm2JSN3Cyc6rge2gnvD3W5K (BTC)
- 1J9oGoAiHeRfeMZeUnJ9W7RpV55CdKtgYE (BTC)
- 1295rkVyNfFpqZpXvKGhDqwhP1jZcNNDMV (BTC)
- 1LiNmTUPSJEd92ZgVJjAV3RT9BzUjvUCkx (BTC)
- 1LrxsRd7zNuxPJcL5rttnoeJFy1y4AffYY (BTC)
- 1KUUJPkyDhamZXgpsyXqNGc3x1QPXtdhgz (BTC)
- 1CF46Rfbp97absrs7zb7dFfZS6qBXUm9EP (BTC)
- 1Df883c96LVauVsx9FEgnsourD8DELwCUQ (BTC)
- Bc1qdt3gml5z5n50y5hm04u2yjdphefkm0fl2zdj68 (BTC)
- 1B64QRxfaa35MVkf7sDjuGUYAP5izQt7Qi (BTC)
- 0x2f389ce8bd8ff92de3402ffce4691d17fc4f6535 (ETH)
- 0x19aa5fe80d33a56d56c78e82ea5e50e5d80b4dff (ETH)
- 0xe7aa314c77f4233c18c6cc84384a9247c0cf367b (ETH)
- 0x308ed4b7b49797e1a98d3818bff6fe5385410370 (ETH)
- 0x2f389ce8bd8ff92de3402ffce4691d17fc4f6535 (USDT)
- 0x19aa5fe80d33a56d56c78e82ea5e50e5d80b4dff (USDT)
- 1KUUJPkyDhamZXgpsyXqNGc3x1QPXtdhgz (USDT)
- 1CF46Rfbp97absrs7zb7dFfZS6qBXUm9EP (USDT)
- 1LrxsRd7zNuxPJcL5rttnoeJFy1y4AffYY (USDT)
- 1Df883c96LVauVsx9FEgnsourD8DELwCUQ (USDT)
- 16iWn2J1McqjToYLHSsAyS6En3QA8YQ91H (USDT)
Today's sanctions are also the first ones levied by the US Treasury against a cryptocurrency exchange portal that's still operating.
In 2017, US officials sanctioned accounts with the BTC-e exchange, but the sanctions came after the FBI had already shut down the portal and arrested its owner.
The Treasury also sanctioned the Helix cryptocurrency mixing service, but just like the BTC-e sanctions, these also came after the FBI apprehended the service's owner.
The move to sanction Suex comes after the Biden administration said last week it was preparing to crack down on intermediaries that prop up the ransomware ecosystem, with cryptocurrency exchanges being number one on that list.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.


