US Nuclear Security Administration criticized by watchdog over cybersecurity failures
The U.S. agency that maintains and modernizes the country’s nuclear stockpile was criticized by a government watchdog this week for lackluster cybersecurity policies that endangered both IT and operational technology networks.
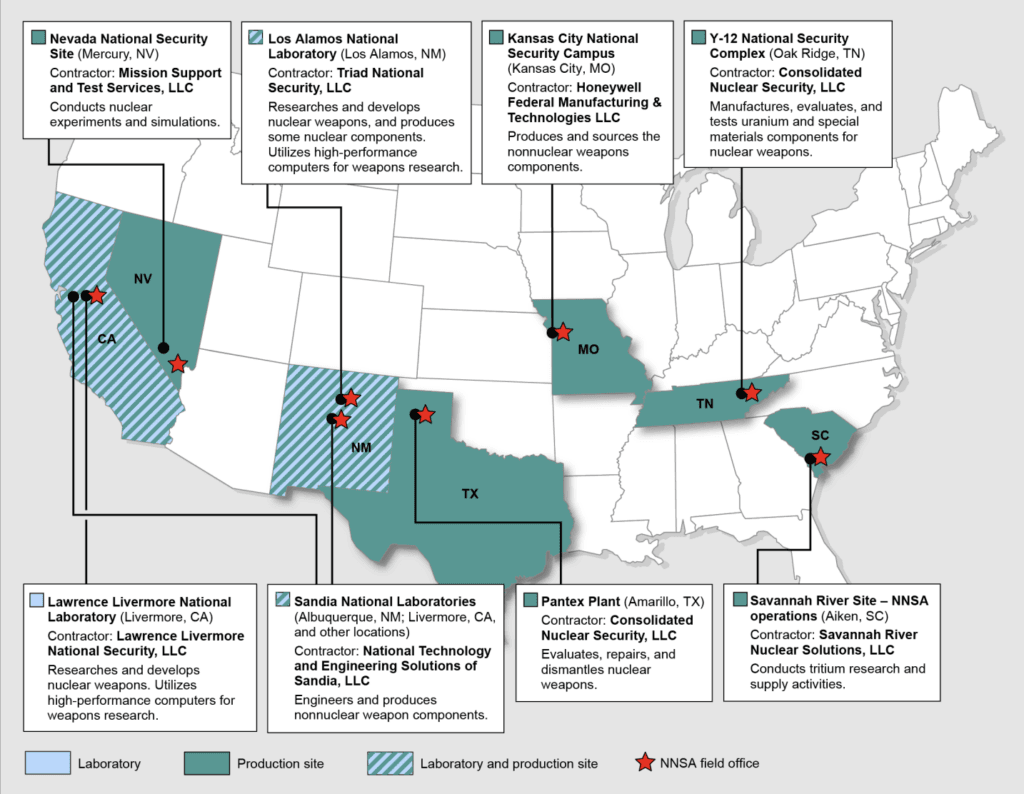
The U.S. Government Accountability Office (GAO) published an 81-page report on Thursday outlining the cybersecurity failings of the National Nuclear Security Administration (NNSA) — a separately-organized agency within the Department of Energy (DOE) tasked with managing U.S. nuclear weapons at eight laboratory and production sites across the country.
According to the GAO, NNSA and its contractors haven't fully implemented six federally-mandated cybersecurity practices — which include implementing foundational risk management practices and more.
For the traditional IT environment used for weapons design, the NNSA partially implemented all of the practices but had not fully implemented a continuous monitoring strategy “because their strategy documents were missing key recommended elements.”
“Without such elements, NNSA and its contractors lack a full understanding of their cybersecurity posture and are limited in their ability to effectively respond to emerging cyber threats,” GAO said.
The NNSA’s operational technology environment — which involves manufacturing equipment and building control systems with embedded software — had not fully implemented a risk management program and specific guidance for contractors, according to GAO.
One part of the report highlighted by the GAO was the security practices around the nuclear weapons IT environment, which includes any IT in or in contact with weapons. Most of the security practices were implemented with these systems, but the GAO noted that the NNSA has not developed a cyber risk management strategy to address nuclear weapons IT-specific threats.
“The absence of such a strategy likely constrains NNSA’s awareness of and responses to such threats. NNSA’s cybersecurity directive requires contractors to oversee their subcontractors’ cybersecurity measures, but contractors’ efforts to provide such oversight are mixed, and three of seven contractors do not believe it is a contractual responsibility,” the GAO said.
“An NNSA official proposed adding an evaluation of such oversight to its annual contractor performance evaluation process, but NNSA could not provide evidence that it had done so. These oversight gaps, at both the contractor and NNSA level, leave NNSA with little assurance that sensitive information held by subcontractors is effectively protected.”
The GAO cited a 2021 ransomware attack on Sol Oriens — a technology research and development subcontractor to an NNSA contractor — as an example of the risks faced by the agency's uneven management of contractors.
The attack “led to the unauthorized disclosure and public posting of invoices for NNSA contracts and descriptions of research and development projects managed by defense and energy contractors.”
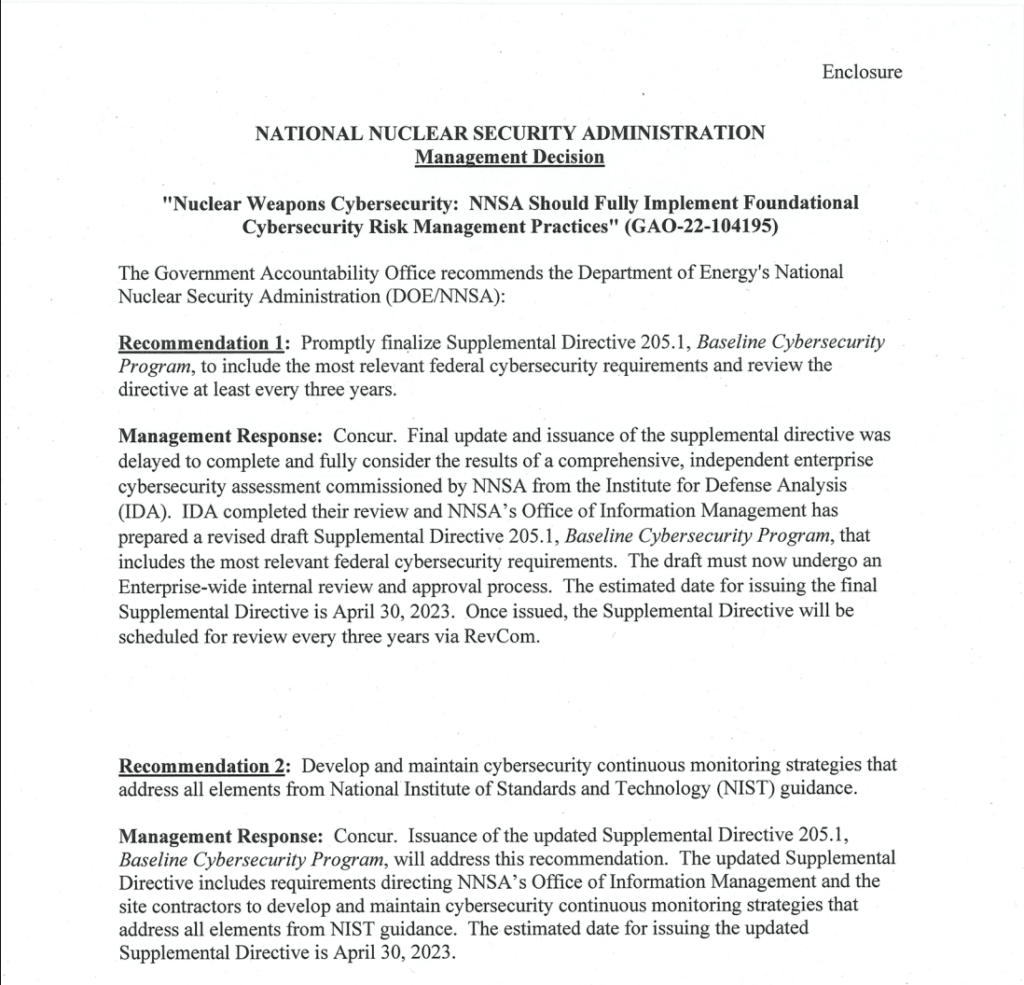
GAO made nine recommendations to NNSA that included mandates to fully implement an IT continuous monitoring strategy, determine the resources needed for OT efforts, create a nuclear weapons risk strategy and improve how it monitors subcontractor cybersecurity.
An NNSA spokesperson told The Record that the DOE and NNSA “recognize the importance of cybersecurity, including nuclear weapon cybersecurity” and have “taken positive steps to address the ever-growing digital threat to our programs.”
“DOE/NNSA appreciates GAO’s observations on our efforts so far and we have outlined specific actions planned to address each recommendation,” the spokesperson said.
‘Out of sync’
Deeper in the report, GAO researchers found that NNSA’s OT environment is "vast and highly complex, encompassing hundreds of thousands of systems potentially at risk” across the country. The size of the OT environment made the agency’s missteps particularly concerning, according to the report.
“NNSA’s OTA initiative is still in its inception phase after 3 years and is proceeding at a pace out of sync with the potential scope and severity of the cybersecurity risk present in this environment,” the report said.
“By creating a business case for the OTA activity that it can feed into NNSA’s existing budgeting process, NNSA will be better positioned to marshal the attention and resources necessary to develop an OT cybersecurity risk management framework that aligns with foundational risk management practices—a vital activity of national security interest.”
Policies in other departments and environments “fall short” of what is needed to address the kind of cybersecurity threats an agency like NNSA faces, GAO said.
GAO was even more concerned about contractor oversight, noting that NNSA “has an urgent need to swiftly” clarify cybersecurity measures around subcontractors.
The report implies that NNSA needs “greater assurance that information handled by contractors and subcontractors is consistently and effectively protected.”
The report includes responses from NNSA to each recommendation about ways the agency plans to address the issues — which ranged from the creation of specific cybersecurity programs to more outlined cybersecurity roles and annual contractor reviews.
A draft of the report was initially shown to the Secretaries of Defense and Energy, and the Administrator of the National Nuclear Security Administration.
“In its comments, reproduced in appendix IX, NNSA agreed with our recommendations and described planned actions to address them. NNSA and contractor representatives from NNSA’s sites also provided technical comments, which we incorporated as appropriate,” GAO said.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



