US Dept of Health warns of ‘increased’ Royal ransomware attacks on hospitals
The U.S. Department of Health and Human Services (HHS) warned hospitals and organizations in the healthcare sector to stay on alert for attacks from the Royal ransomware group, a relatively new gang that emerged in September.
In an alert released this week, HHS said attacks by the group on healthcare facilities are increasing and that the group typically demands ransoms between $250,000 and $2 million.
“Due to the historical nature of ransomware victimizing the healthcare community, Royal should be considered a threat to the HPH sector,” officials said.
“Royal is an operation that appears to consist of experienced actors from other groups, as there have been observed elements from previous ransomware operations. While most of the known ransomware operators have performed Ransomware-as-a-Service, Royal appears to be a private group without any affiliates while maintaining financial motivation as their goal.”
Like most ransomware groups, the gang steals sensitive data and threatens to leak it to pressure victims into paying ransom – known as “double-extortion attacks.”
HHS noted that the operation previously used an encryptor from ransomware group BlackCat but now uses one from another group named Zeon – which they said generates a “ransomware note that was identified as being similar to Conti’s.”
Conti was one of the most prolific ransomware groups, launching high-profile attacks on institutions including the government of Costa Rica, until it disbanded in May.
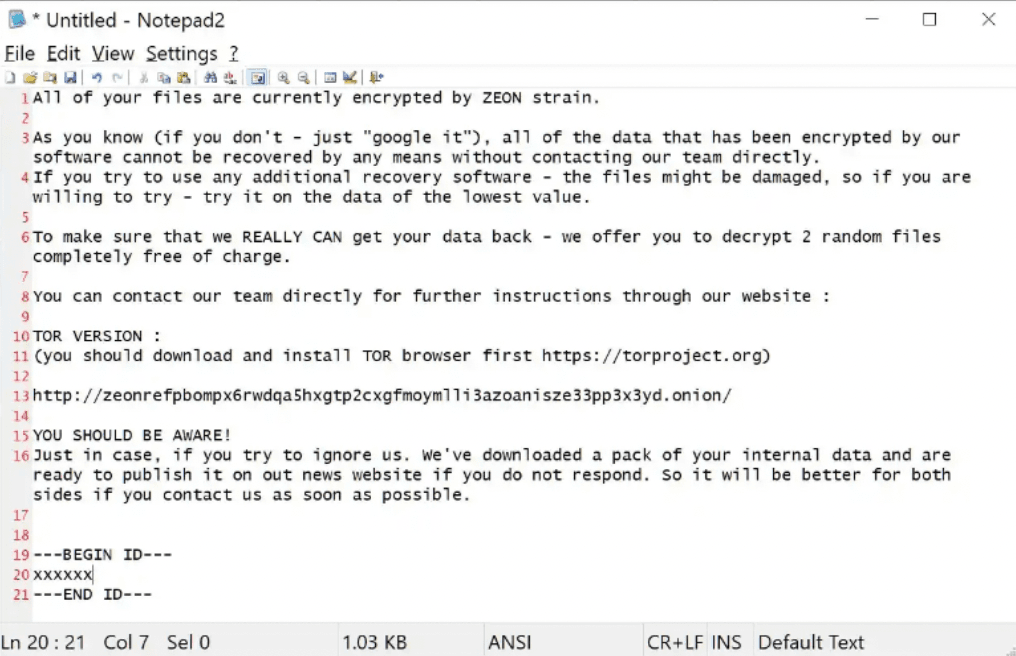
The ransomware works to delete all copies of data on a network, and once files are encrypted the extension is changed to “.royal.”
“Royal is a newer ransomware, and less is known about the malware and operators than others. Additionally, on previous Royal compromises that have impacted the HPH sector, they have primarily appeared to be focused on organizations in the United States,” HHS said.
“In each of these events, the threat actor has claimed to have published 100% of the data that was allegedly extracted from the victim.”
The advisory notes that the group typically uses phishing to gain entry to systems before compromising credentials and moving laterally within a system. The group has also been seen exploiting vulnerabilities affecting VPN servers and other products.
HHS also referenced a Microsoft report released two weeks ago that found multiple actors spreading the Royal ransomware. That report found that the group used Google Ads in one of their campaigns of attacks – which includes dozens of law firms and businesses across the U.S. as well as one of the most popular motor racing circuits in the United Kingdom.
The researchers said in late October they discovered a “malvertising” campaign where the hackers – which they track as DEV-0569 – used Google Ads to redirect users to a download site with malicious files. Microsoft said it reported the abuse of the traffic distribution system to Google.
“DEV-0569 notably relies on malvertising, phishing links that point to a malware downloader posing as software installers or updates embedded in spam emails, fake forum pages, and blog comments,” the Microsoft researchers said.
HHS echoed those findings, saying the gang has been seen embedding malicious links in malvertising, phishing emails, fake forums, and blog comments. They have also seen the group use an organization’s contact forum that can bypass email protections, and placing malicious installer files on legitimate looking software sites and repositories.
Recorded Future senior security architect Allan Liska said last month that while the Royal ransomware group is new, it appears to be made up of experienced hackers that previously worked as affiliates for other ransomware groups.
“They have been known to use multiple ransomware types and unlike a lot of current ransomware groups which randomly generated extensions for encrypted files, they use the .Royal extension,” he explained.
“They were also seen earlier this year using callback phishing campaigns. While this attack is not new, it is uncommon for ransomware groups.”
HHS has released multiple reports on ransomware groups this year, including ones on the Cuba, Venus, Lorenz and Hive ransomware groups.
Stephan Chenette, CTO at AttackIQ, noted that the warning comes immediately after CommonSpirit Health confirmed that a recent ransomware attack exposed the data of over half a million patients.
Knowing the procedures used by the adversary helps inform organizations’ security programs and assists in building a more resilient, proactive defensive and responsive security program that protects patient information, Chenette added.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



