Unpatched bug allows takeover of Horde webmail accounts, servers
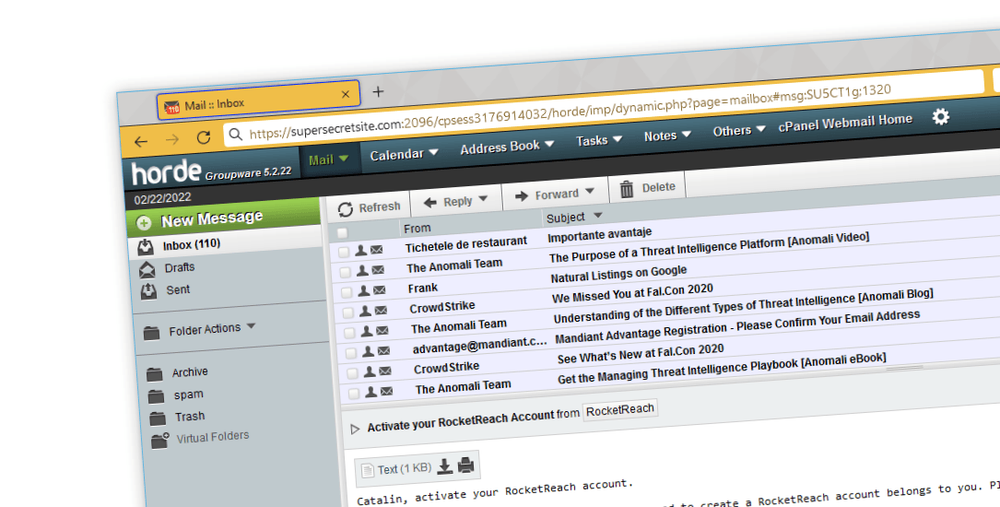
Companies that use Horde to view emails in their browsers are advised to change a default setting in their webmail application to avoid having email accounts hijacked using a dangerous vulnerability that was disclosed today and has yet to be patched by the Horde team.
Discovered by SonarSource vulnerability researcher Simon Scannell, the vulnerability has existed in the Horde webmail app since late 2012 and resides in the feature that takes OpenOffice documents and creates previews to show inside the browser window.
This process involves taking the OpenOffice document's XML and XSLT files and converting them into HTML and CSS that can be used to show a preview of the document inside Horde's preview pane.
In a report published today, Scannell said that a threat actor could add malicious XML code to an OpenOffice document that exploits how this conversion takes place to generate malicious JavaScript code that, when executed inside a user's Horde inbox, would run malicious commands on behalf of the attacker.
The vulnerability, categorized as a stored cross-site scripting (XSS) issue, can allow attackers to retrieve a user's inbox or modify account settings.
"If an attacker succeeds in targeting an administrator with a personalized, malicious email, they could abuse this privileged access to take over the entire webmail server," Scannell also added.
The vulnerability is considered a critical issue not only because of its possible consequences but also because of Horde's large userbase.
The webmail app is one of the three webmail clients that ship by default with cPanel, an advanced control panel used by the vast majority of today's web hosting companies, which means the webmail app is installed on tens of millions of websites, if not more, all of which are now exposed to attacks.
No patch available, but there's a way to block attacks
Scannell said that despite their efforts to contact the Horde project last August, the maintainers have failed to remain in contact with the researchers and have not responded to any follow-up emails about a possible patch, with the vulnerability remaining unpatched at the time of writing.
An email to the Horde team inquiring about the SonarSource report and a possible upcoming patch for this issue was not returned before publication.
Scannell said that despite the severity of the issue they discovered, there is at least a way to mitigate and prevent attacks—namely, by disabling the rendering of OpenOffice attachments inside the Horde webmail app.
"To do so, administrators can edit the config/mime_drivers.php file in the content root of their Horde installation," Scannell said, recommending that Horde server owners change this option to 'disable' => true.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.