Ukraine arrests operator of DDoS botnet with 100,000 bots
Ukrainian law enforcement announced the arrest of a suspect on accusations of running a giant malware botnet of more than 100,000 infected systems.
Authorities said the suspect used their botnet to launch DDoS attacks, send spam, brute-force user account passwords, scan networks for vulnerabilities, and exploit them.
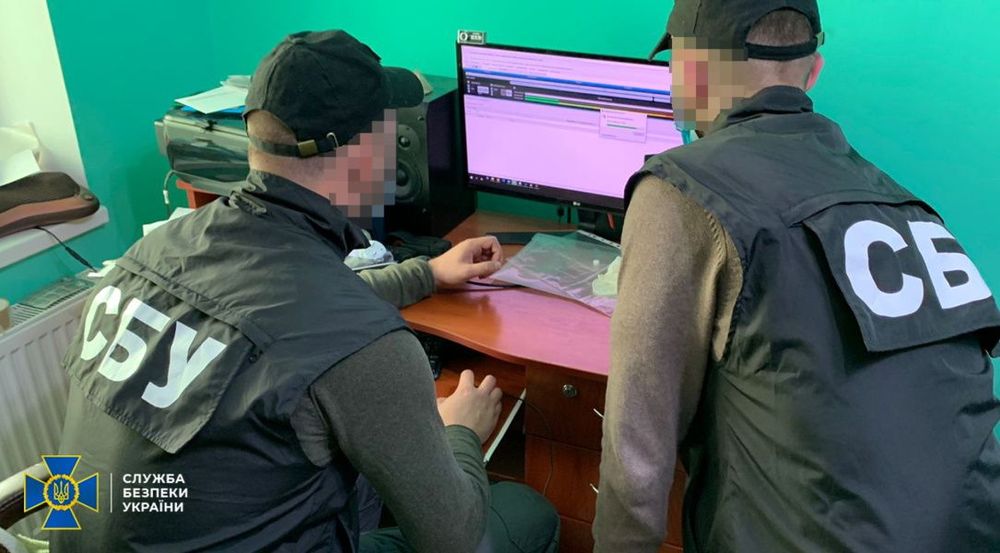
The arrest was announced today by the Security Service of Ukraine (SSU):
- The suspect's name was not released.
- The arrest took place in the Ivano-Frankivsk region, in the Kolomyia district.
- SSU officers searched the suspect's house and seized their computer equipment.
- SSU said the suspect had advertised their services via Telegram and closed-access forums.
- The suspect took payment via WebMoney, a Russian money transfer platform banned in Ukraine.
News of the arrest comes after Russian security firm Rostelecom-Solar helped sinkhole the Meris DDoS botnet and after US authorities charged a Turkish national in connection to the WireX botnet.
It is unclear to which malware botnet the suspect arrested in Ukraine is connected. An SSU spokesperson did not return a request for comment.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.