UK says its offensive cyber operations are ‘accountable, precise, and calibrated’
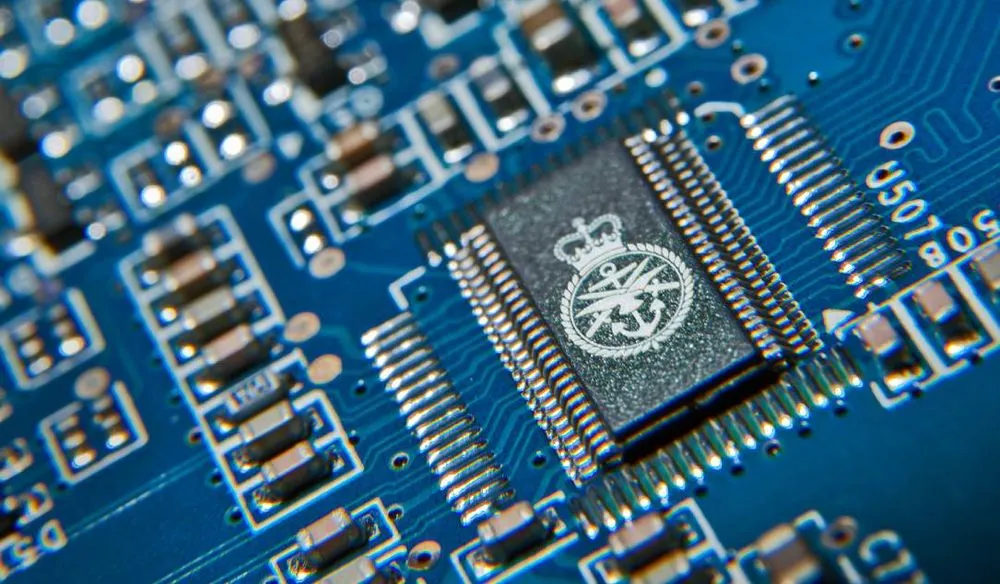
As the role of cyber operations in international statecraft continues to grow, the United Kingdom’s National Cyber Force (NCF) has published a paper arguing that its activities are fundamentally different from those of its adversaries.
In contrast to the “reckless” cyberattacks which U.K. says Russia and China have engaged in — namely the destructive NotPetya and Microsoft Exchange operations — Britain’s offensive hacking activities are designed to be “accountable,” “precise,” and “calibrated,” the NCF explained.
In the paper published on Tuesday, offering the most detailed explanation of Britain’s offensive cyber capability to date, the agency said it was “right that we enable greater transparency and engage with the public more widely than has been done before,” and said doing so was a crucial part of “demonstrating the UK’s commitment to being a responsible and democratic cyber power.”
As part of this public engagement, the document was launched following an event at Dartmouth House in London’s Mayfair on Monday morning where the British intelligence and security agency GCHQ hosted a number of academics specializing in cyber conflict research, although journalists were not invited.
Attendees who spoke to The Record on the condition of anonymity said the document was a positive contribution towards global discussions about cyber conflict, although they regretted that there were no specific examples in the paper of the NCF’s activities and the “strong ethical component” involved in operational planning.
The NCF’s document stated its work is covert “and we therefore do not reveal details of individual operations.”
“Indeed the intent is sometimes that adversaries do not realise that the effects they are experiencing are the result of a cyber operation.”
The document comes out as the NCF for the first time publicly avows its new chief, James Babbage, who has been an intelligence officer at GCHQ for nearly 30 years.
Babbage — who is not related to Charles Babbage, the inventor of the mechanical computer — is the commander of the NCF, effectively a two-star rank equivalent to a major general. He formerly served on secondment to the Ministry of Defence (MoD) and completed a tour as a liaison officer in the U.S.

‘A shared vision’
The NCF was formally founded in 2020 to consolidate the different offensive cyber activities undertaken across the British services. It includes staff from GCHQ, the Secret Intelligence Service, and the MoD.
It is not yet fully staffed as there is a shortage of personnel with the appropriate skills across the British military and intelligence communities, and its new permanent base in the village of Samlesbury in Lancashire has not been built. But ultimately the NCF is expected to be “made up of a roughly equal share of personnel from the MoD and the intelligence agencies.”
The NCF is currently “carrying out operations on a daily basis,” according to the document, which intends to outline “some of the operational principles that lie behind these activities.”
It contributes to the U.K.’s national cybersecurity strategy, which involves advancing Britain's “global leadership and influence” by engaging diplomatically with other nations to establish ground rules for cyber conflict.
Sir Jeremy Fleming, the outgoing director of GCHQ, said the agency hoped the document “provides a benchmark for the UK’s approach and a basis for like-minded governments to come together internationally to establish a shared vision and values for the responsible use of cyber operations.”
Aside from diplomatic engagements with like-minded governments, the U.K. has also attributed irresponsible activities to their perpetrators, which has been met with “whataboutism” from Russia and China.
Russia's Deputy Foreign Minister Oleg Syromolotov claimed last year that the United States and European Union were conducting a campaign of cyber "sabotage" against Russia, following several allegations that Russian state-sponsored cyber units had attempted to sabotage civilian infrastructure in Ukraine.
When China was blamed for the hacking campaign against Microsoft Exchange servers, one of the foreign ministry’s most influential spokespeople accused the U.S. of being “the world's largest source of cyber attacks.”
Alexander Martin
is the UK Editor for Recorded Future News. He was previously a technology reporter for Sky News and is also a fellow at the European Cyber Conflict Research Initiative.