U.S. Ramps Up Pressure on Chinese Hackers With New Charges Against 5 Chinese Nationals
Federal law enforcement officials on Wednesday announced that five alleged members of a Chinese hacking group known as APT41 had been charged for their role in “unprecedented” efforts to compromise and siphon sensitive data from more than 100 companies.
Two Malaysian businessmen have also been arrested and face extradition to the U.S. in a separate indictment that charged them with helping the Chinese hackers defraud video game companies.
Although the Justice Department did not go so far as to say that the hackers were working on behalf of the Chinese government, a number of details revealed in the indictments suggest that they had tacit approval to target foreign organizations.
“You see targets that were pro-democracy groups, think tanks, and universities. A hacker for profit is not going to hack a pro-democracy group,” Acting U.S. Attorney for the District of Columbia Michael Shirwin said at a press conference. “This is a breadcrumb that shows that these individuals were working for private personal gain but were also proxies for the Chinese government.”
Additionally, defendants allegedly boasted that they had contacts with members of the Chinese state apparatus, such as the Ministry of State Security, and mentioned that they had agreements not to hack domestic targets, according to documents unsealed Wednesday.
The indictments come about two months after the U.S. charged two Chinese spies for an alleged global hacking campaign, and can be seen as a broader effort by the Trump administration to expose Chinese cyberoperations. In late May, the FBI and the Department of Homeland Security’s CISA unit in a rare joint statement accused top Chinese hackers of trying to steal coronavirus research, calling it a “significant threat” to the nation’s coronavirus response.
In its announcement on Wednesday, top Justice Department officials praised the Malaysian government and private sector partners while criticizing the Chinese government for effectively shielding hackers who operate within its borders.
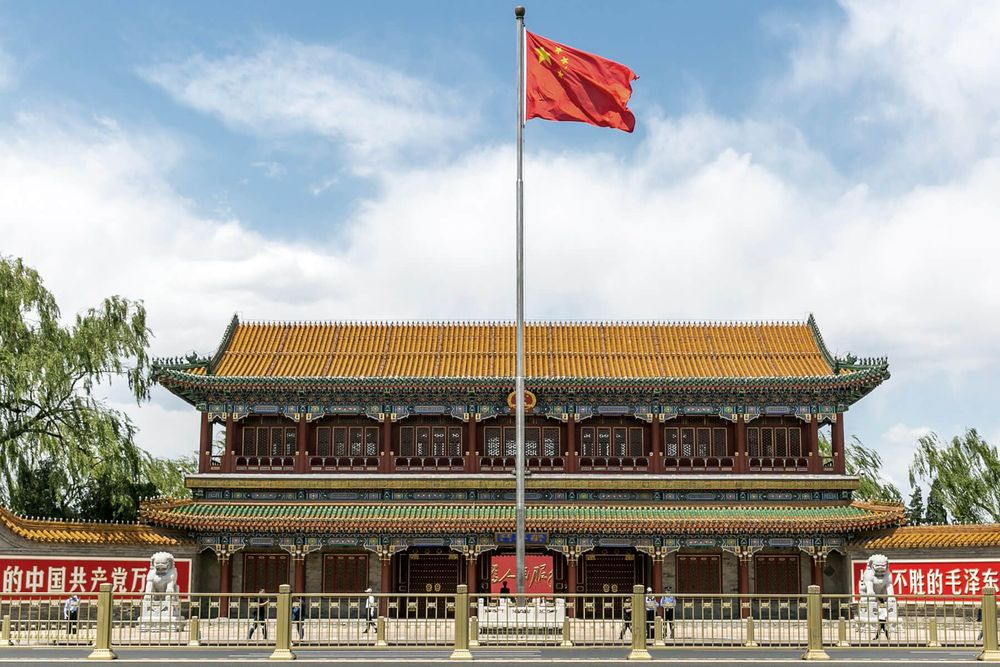
“Ideally I would be thanking Chinese law enforcement authorities for their cooperation in this matter and the five Chinese hackers would now be in custody awaiting trial,” said Deputy Attorney General Jeffrey Rosen at the press briefing. “Unfortunately… the Chinese Communist Party has a demonstrated history of choosing a different path, that of making China safe for their own cybercriminals, so long as they help with its goals of stealing intellectual property.”
The five Chinese nationals named in the indictments are Zhang Haoran, Tan Dailin, Qian Chuan, Fu Qiang, and Jiang Lizhi.
The hacking activities described in the indictments paint a detailed picture of a group that has a wide range of targets, deep pockets, and a variety of tools in its hacking arsenal.
In the indictment against Zhang Haoran, for example, DoJ officials described how the defendant allegedly used sophisticated supply chain attacks to compromise a variety of organizations without actually targeting them. “[Conspirators] would gain unauthorized access to a victim software company’s computer network and modify the software company’s otherwise legitimate software with malicious code. The victim software company — unaware of the malicious changes to its product — would subsequently distribute the modified software to its third-party customers, who were thereby defrauded into installing malicious software code on their own computers,” the indictment reads.
Cybersecurity specialists have tied APT41 to several supply chain attacks in recent years, according to a Recorded Future analyst, who called the tactic one of the group’s “calling cards.”
Another notable aspect of the group, which is detailed in the indictments, is that it straddles the line between cybercrime and state-sponsored hacking.
“These operators have been effectively moonlighting — they have a day job of stealing secrets and intellectual property at what appears to be the behest of the Chinese government, while at the same time they use their hacking tools for cybercrime,” according to the analyst.
One of the indictments unsealed Wednesday describes efforts defendants have taken since at least November 2014 to hack the networks of video game companies and fraudulently obtain or generate in-game currency, which they would sell for a profit. At the same time, the hackers would use their unauthorized access to the corporate networks to monitor and evade the video game firms’ fraud detection teams.
“We see this as a new area in which hackers are exploiting — I’m sure this isn’t the end, and we’re going to see much more of this criminal conduct unfortunately,” Shirwin said, referring to attacks against the multibillion-dollar video game industry.
Adam Janofsky
is the founding editor-in-chief of The Record from Recorded Future News. He previously was the cybersecurity and privacy reporter for Protocol, and prior to that covered cybersecurity, AI, and other emerging technology for The Wall Street Journal.