Twitch source code and business data leaked on 4chan
An unknown individual has leaked the source code and business data of video streaming platform Twitch via a torrent file posted on the 4chan discussion board earlier today.
The leaker said they shared the data as a response to the recent "hate raids" —coordinated bot attacks posting hateful and abusive content in Twitch chats— that have plagued the platform's top streamers over the summer.
"Their community is [...] a disgusting toxic cesspool, so to foster more disruption and competition in the online video streaming space, we have completely pwned them, and in part one, are releasing the source code from almost 6,000 internal Git repositories," the leaker said earlier today.
The Record has downloaded parts of the 125 GB torrent file shared by the leaker in order to confirm its authenticity.
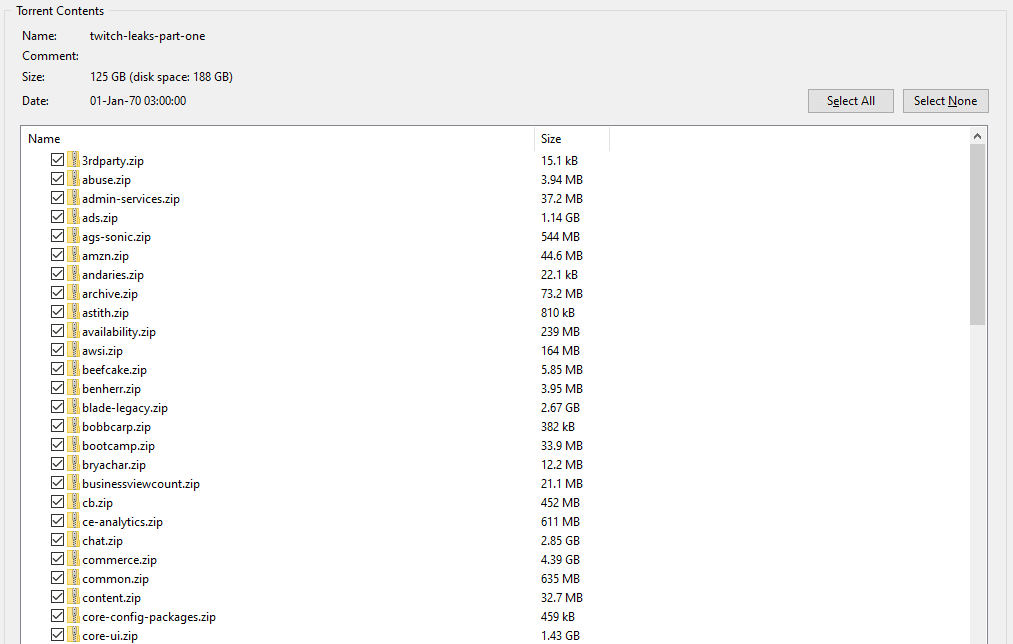
The content of the leak is in tune with what the leaker claimed to have shared earlier today, quoted below:
- Entirety of Twitch.tv, with commit history going back to its early beginnings
- Mobile, desktop and video game console Twitch clients
- Various proprietary SDKs and internal AWS services used by Twitch
- Every other property that Twitch owns including IGDB and CurseForge
- An unreleased Steam competitor from Amazon Game Studios
- Twitch SOC internal red teaming tools (lol)
- AND: Creator payout reports from 2019 until now. Find out how much your favorite streamer is really making!
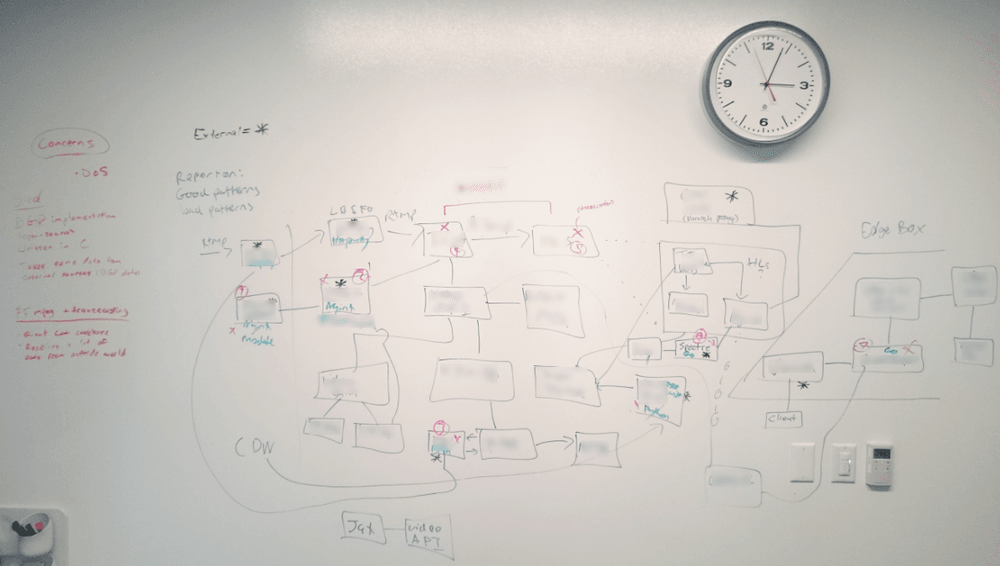
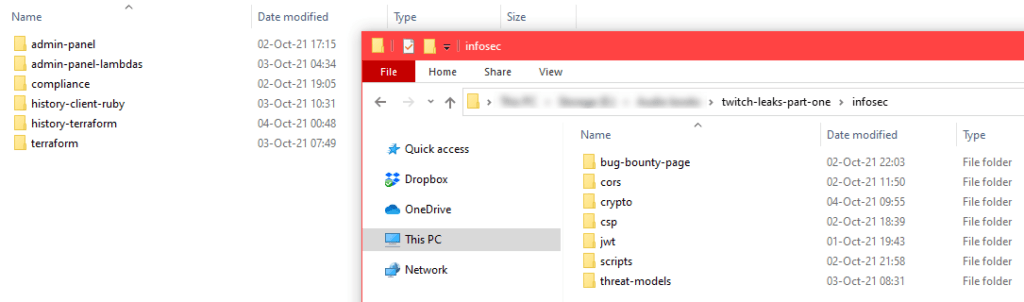
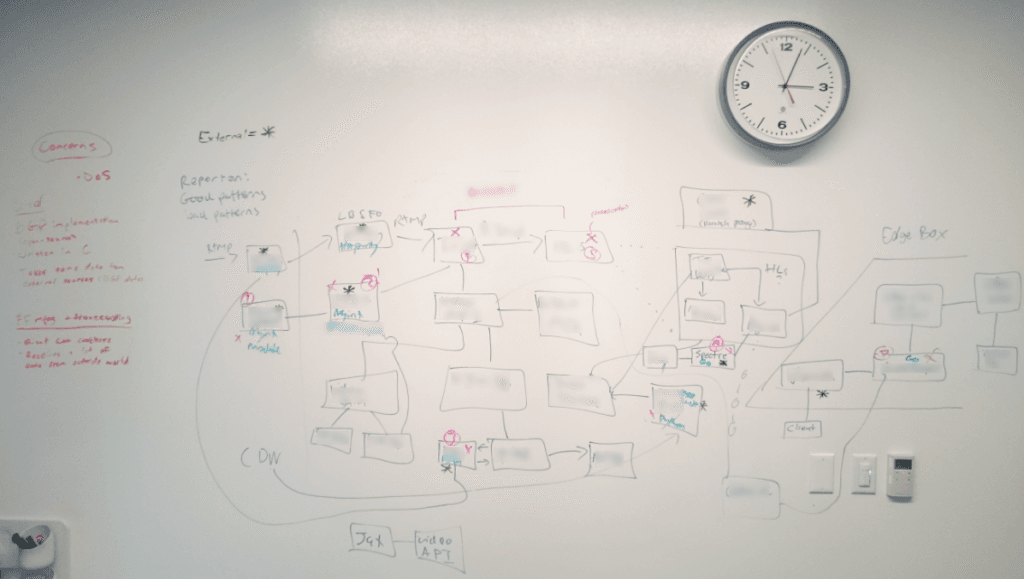
Among the treasure trove of data, the most sensitive folders are the ones holding information about Twitch's user identity and authentication mechanisms, admin management tools, and data from Twitch's internal security team, including white-boarded threat models describing various parts of Twitch's backend infrastructure [see redacted image below].
While at the time of writing, The Record was unable to find personal details for any Twitch users, the leak also contained payout schemes for the platform's top streamers, some of which had already confirmed its accuracy [1, 2, 3, 4].
The data, which we will not be linking or sharing in any way, is exposing the monthly revenues for some of the platform's biggest earners, some of which reach six-figure sums; data that could be a boon for extortionists and criminal groups.
Reached out for comment, Twitch confirmed the breach via email:
We can confirm a breach has taken place. Our teams are working with urgency to understand the extent of this. We will update the community as soon as additional information is available. Thank you for bearing with us.
Ashley Lloyd, Twitch EMEA Communications Manager
The source of the leak is currently believed to be an internal Git server. Git servers are typically used by companies to allow large teams of programmers to make controlled and easily reversible changes to source code repositories.
The leak was also labeled as "part one," suggesting that more data will be leaked in the future.
Although no user data was found in the leak, several security researchers have urged users to change their passwords and enable a multi-factor authentication solution for their account as a precaution.
The leak comes a month after thousands of Twitch streams organized the #ADayOffTwitch walkout on September 1, refusing to stream in response to the ever-increasing hate raids.
In August, Twitch promised to address the hate raids in a message posted on Twitter, asking for patience as the spam attacks did not have "a simple fix."
Article text has been updated with additional screenshots of the leak and confirmations from Twitch and its streamers. Title and text have updated to remove mention of Anonymous hacker collective as the source of the leak.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.