Tech trade group comes out against Indian cybersecurity law over reporting mandate
A technology trade group that represents Apple, Google, Microsoft and other tech giants has come out against a new directive from the Indian government mandating companies report cybersecurity incidents to CERT-IN within six hours of an incident.
On April 28, the Indian government updated section 70B of the Information Technology (IT) Act, 2000 to add several measures. Service providers, intermediaries, data centers, companies and government organizations have six hours to report a range of intrusions to CERT-IN.
The new rules take effect in 60 days.
“The directions cover aspects relating to synchronization of ICT system clocks; mandatory reporting of cyber incidents to CERT-In; maintenance of logs of ICT systems; subscriber/customer registrations details by Data centers, Virtual Private Server (VPS) providers, VPN Service providers, Cloud service providers; KYC norms and practices by virtual asset service providers, virtual asset exchange providers and custodian wallet providers,” CERT-IN said in a statement.
“These directions shall enhance overall cyber security posture and ensure safe & trusted Internet in the country.”
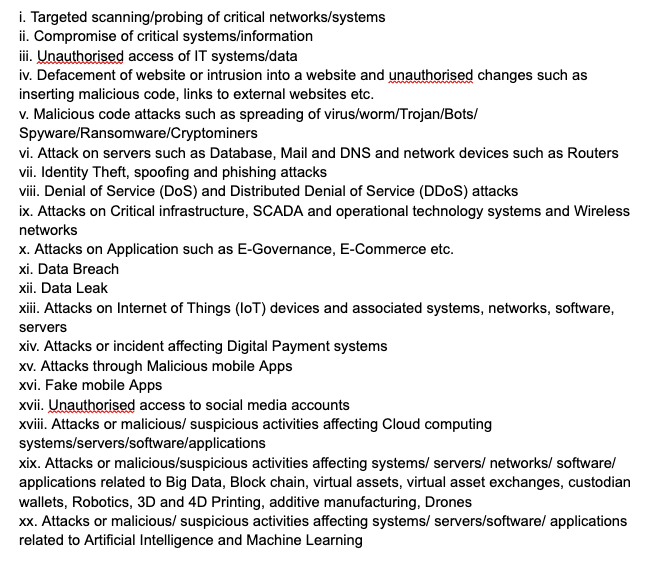
The directive includes a list of the incidents that now need to be reported to CERT-IN.
ITI – a more than 100-year-old global tech trade association whose members include Google, Microsoft, Adobe, Visa and most of the world's largest tech companies – came out fiercely against the new rules on Friday.
In a letter, ITI’s Kumar Deep and Courtney Lang claimed the new rules “may negatively impact Indian and global enterprises and actually undermine cybersecurity in India.”
“In particular, we have concerns with several of the incident reporting obligations, including the mandatory reporting of cyber incidents within 6 hours of noticing, the requirement to enable logs of all ICT systems and maintain them securely within Indian jurisdiction for a rolling period of 180 days, the overbroad definition of reportable incidents, and the requirement that companies connect to the servers of Indian government entities,” the two wrote.
“If left unaddressed, these provisions may have severe consequences for enterprises and their global customers without solving the genuine security concerns.”
They argued the six-hour timespan should be extended to 72 hours and the scope of reportable incidents is “far too broad given probes and scans are everyday occurrences.”
“It would not be useful for companies or Cert-In to spend time gathering, transmitting, receiving, and storing such a large volume of insignificant information that arguably will not be followed up on,” the two argued.
The letter adds that the logging requirement would require too much manpower to handle and that it would “make such repositories of logged information a target for global threat actors.”
Deep and Lang noted that forcing companies to connect to NTP servers “could negatively affect companies’ security operations as well as the functionality of their systems, networks, and applications, amongst other reasons.”
The letter ends with a request for the rules to be delayed and revised following “a wider stakeholder consultation.”
ITI’s membership pool includes several cybersecurity firms, including Fortinet, Palo Alto, NortonLifeLock, Rapid7, Tenable and more.
Wired reported on Thursday that several of the biggest VPN providers have also come out against India's new rules as well.
Legislation around cybersecurity incident reporting has long been hamstrung in the U.S. and other countries by companies reluctant to provide information about intrusions, breaches and attacks.
In March, U.S. legislators finally managed to pass a law mandating critical infrastructure owners report if their organization has been hacked or made a ransomware payment. Several efforts to pass wider cyber incident reporting bills in the U.S. have failed.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



