Spyware features found in Chinese state benefits app
Spyware-like features have been discovered inside an app named "Beijing One Pass" that foreign companies operating in China are forced to install on their systems in order to access a digital platform to manage employee state benefits.
The spyware behavior was discovered last month by Insikt Group, the threat research division of Recorded Future, which analyzed a copy received from a customer who was forced to install the suspicious on its systems.
According to the team's analysis, the app contained features that could be considered "suspicious for a benefits software application" and which are ordinarily found in malware strains. This included features such as:
- Disabling of security and backup services on the host device
- Reading data from the clipboard
- Recording screenshots
- Capturing and retrieving keystrokes
- Attempt to read, create, or modify system registry ROOT certificates
- Check periodically for human interaction with the operating system as the file is run
- Allow-listing domains for ActiveX use, which would allow it to connect to external internet resources
- The ability to autorun at Windows startup to ensure persistence
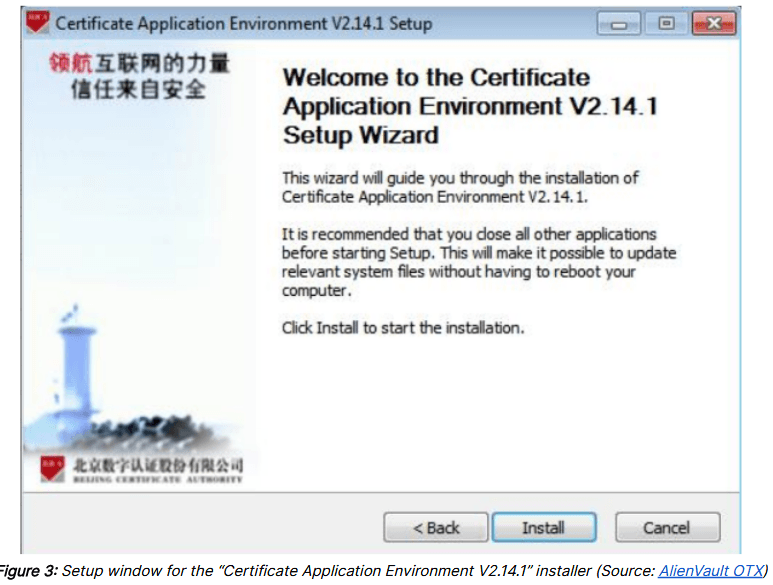
The suspicious app, shown in the image above, was developed by the Beijing Certificate Authority (BJCA), a Chinese state-owned company primarily known for its certificate authority (CA) business.
At the time of writing, it is unclear if the spyware features were added inside the Beijing One Pass software on purpose or if they were inserted after a compromise of the company's software development pipeline.
Contacted by phone, a BJCA spokesperson did not want to comment.
While information about how the spyware functionality made it inside the app is still shrouded in mystery, their presence is undeniable. Furthermore, companies doing business in China may not have an option and may be forced to install the software.
For this reason, Insikt Group analysts recommend that companies run the app only on systems that do not store sensitive corporate information.
The Insikt Group's discovery is also reminiscent of the findings of Trustwave Labs, which found in June 2020 that a Chinese bank was forcing foreign companies operating in China to install a backdoored app in order to file taxes with local governments.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.



