SickKids: 80% of hospital priority systems back online after LockBit ransomware attack
Toronto’s Hospital for Sick Children, Canada’s largest pediatric health center, said it has restored 80% of its systems that have a direct impact on hospital operations following a ransomware attack.
A spokesperson for the hospital told The Record that patients and families dealt with diagnostic and treatment delays because clinical teams struggled to receive lab reports and imaging results after the LockBit ransomware group launched an attack on the night of December 18.
While the hospital’s electronic medical record system was not affected by the attack, several other tools connected to the system were damaged – including dictation services, pharmacy systems and the ability to view diagnostic imaging results. The hospital’s internal timekeeping system for staff and intranet were also affected by the ransomware attack.
“Ransomware and other malware attacks are becoming more and more frequent and sophisticated across organizations and industries. We know those behind these attacks are always trying to find new ways to get past digital defenses,” said Nimira Dhalwani, Chief Technology Officer at SickKids, a common name for the hospital.
“We are working with our experts and industry partners to strengthen our collective systems wherever possible.”
The hospital – founded in 1875 – issued a “Code Grey” notice when they realized many of their systems were inaccessible, kickstarting their incident response processes and led to the hiring of a cybersecurity firm to deal with the response.
Experts are still working with the hospital’s Information Management Technology team to restore downed systems but the “Code Grey” notice has been lifted since most critical systems are back to normal.
“I want to express my deepest gratitude and thanks to our staff, patients, families and community partners for their patience and support, as well as the broader community for the overwhelming offers of assistance and expertise over the past two weeks,” said SickKids CEO Ronald Cohn.
“Without the extremely hard work of our staff and expertise of external advisors over the holidays, we would not have been able to lift the Code Grey as efficiently as we have.”
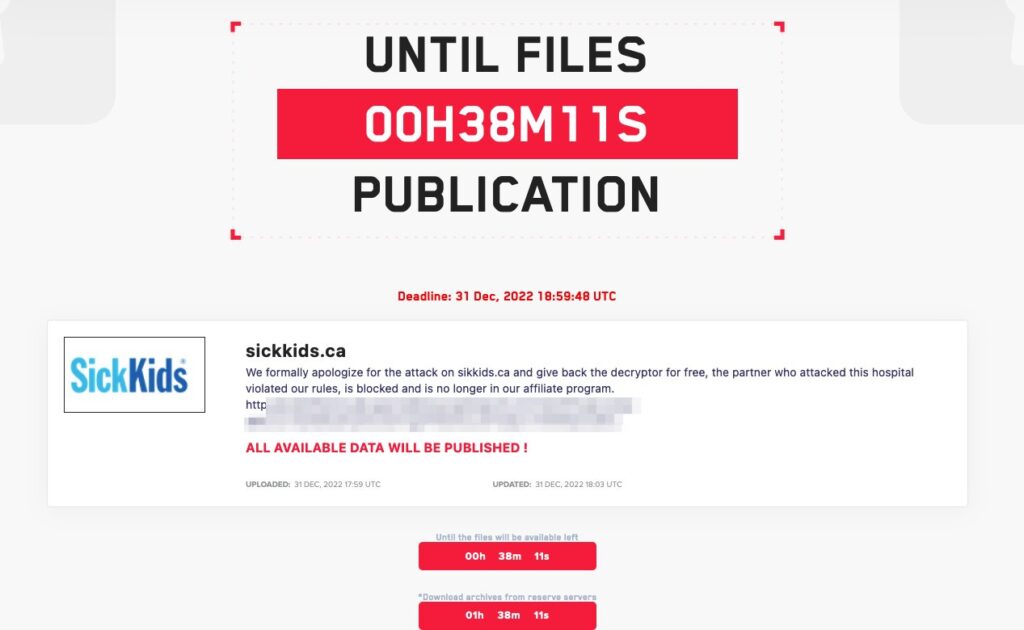
The hospital noted that it has not yet used the decryptor offered to them by LockBit operators, who took the extraordinary step of apologizing for the attack after it drew international attention.
A spokesperson for the hospital said it is still in the process of working with cybersecurity experts to determine whether they should use the decryptor.
“SickKids continues to consult with its third-party experts to determine the most efficient and effective means to restore its impacted systems, including the possible use of the decryptor,” a spokesperson said.
In a message posted to their leak site on Saturday, the ransomware gang said it “formally apologizes for the attack on Sick Kids.”
“The partner who attacked this hospital violated our rules, is blocked and is no longer in our affiliate program,” the group said.
LockBit, like a number of ransomware groups, has tenuous rules for its hackers and affiliates warning them not to attack certain institutions, like hospitals. These rules have done little to stop the group from frequently targeting hospitals.
Three weeks ago the group was accused of attacking Hospital Centre of Versailles in France and in August, LockBit proudly took credit for a crippling attack on Center Hospital Sud Francilien in Corbeil-Essonnes. The attack knocked out the hospital’s “business software, storage systems (in particular medical imaging) and the information system relating to patient admissions.”
This is not the first time a ransomware group has offered a decryptor to a hospital after an attack. Both the Conti and DoppelPaymer ransomware gangs offered free decryptors following massive attacks on Ireland’s healthcare system and Helios University Hospital, respectively.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



