SFile (Escal) ransomware ported for Linux attacks
The operators of the SFile ransomware, also known as Escal, have ported their malware to work and encrypt files on Linux-based operating systems.
Attacks with this new Linux variant were spotted late last year, Chinese security firm Rising said in a report last week, confirmed by The Record with MalwareHunterTeam, one of the people behind the ID-Ransomware project.
- The SFile (Escal) ransomware was first seen in attacks in February 2020.
- Initial versions were written for encrypting Windows systems only.
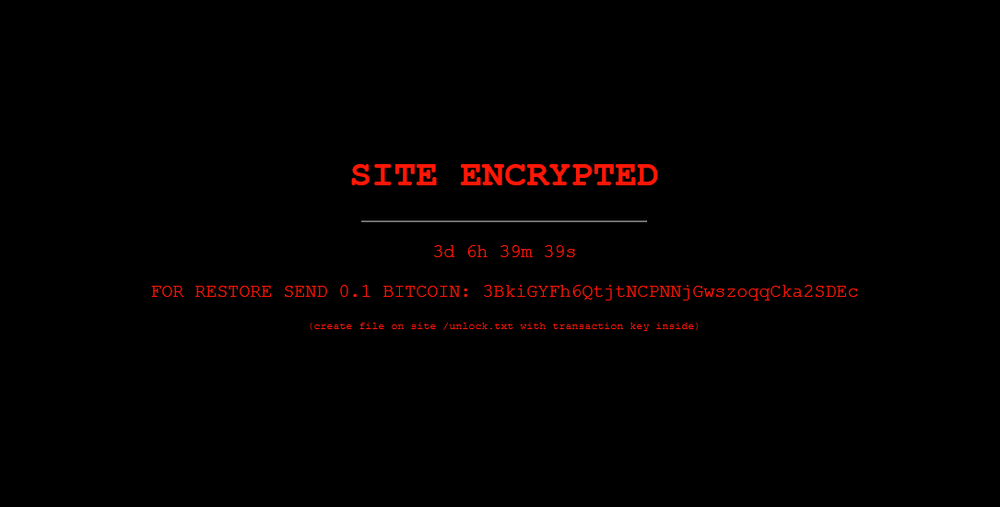
- Over the past two years, the ransomware has been used as part of targeted attacks against corporate and government networks. During these attacks, SFile is usually deployed to encrypt files, and leave a ransom note for victims telling them to contact the attackers via one of three emails and negotiate a ransom for the decryption key.
- Following a general trend in the ransomware ecosystem where gangs have created Linux versions of their payloads, a SFile Linux variant was spotted late last year, with an encryption scheme similar to its original Windows variant, but with a few improvements as well.
- According to MalwareHunterTeam, the most interesting of these was the ability to encrypt files based on a time range—as a way to encrypt recent files, which may be of more importance for some victims, and typically not included in recent backups.
- But the SFile ransomware is also one of the rare cases where the victim's name is used in the extension added at the end of each encrypted file.
- Among recent victims of SFile attacks, there were several Chinese companies.
- The Rising report suggests that one of these victims was Chinese tech firm Nuctech, a company sanctioned by the US in late 2020 for passing air travel passenger info to the Chinese government—as the company's name was found added to encrypted files in a sample found by Rising researchers.
Despite the appearance of a Linux port, the number of SFile attacks remains small in scale compared to activity from more known and established ransomware families, such as Conti, LockBit, Grief, and STOP.
#ESETresearch discovered an SFile #ransomware variant for the FreeBSD platform, targeting a partially state-owned company in #China. It encrypts files with the following file extensions @cherepanov74 1/3 pic.twitter.com/miyIlH1IdI
— ESET Research (@ESETresearch) December 21, 2021
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.