Security firm warns of ransomware attacks targeting Microsoft cloud 'versioning' feature
Researchers said they have discovered a way ransomware groups can encrypt files stored on Microsoft’s SharePoint and OneDrive applications that would make them “unrecoverable without dedicated backups or a decryption key from the attacker.”
The attack centers on the "versioning" feature within SharePoint and OneDrive. SharePoint Online and OneDrive allow users to set the number of saved versions of every document library. Users do not need to be an administrator or have elevated privileges to do this.
Cybersecurity company Proofpoint said that if a ransomware group hijacked a user’s identity and gained access to one or more SharePoint Online or OneDrive accounts, they could reduce the versioning limit of files to a low number "such as 1."
Once the versioning limit is changed, threat actors could encrypt the file more times than the versioning limit.
“This step is unique to cloud ransomware compared to the attack chain for endpoint-based ransomware. In some cases, the attacker may exfiltrate the unencrypted files as part of a double extortion tactic,” Proofpoint researchers explained.
“Now all original (pre-attacker) versions of the files are lost, leaving only the encrypted versions of each file in the cloud account. At this point, the attacker can ask for a ransom from the organization.”
The researchers noted that the steps they outlined could be automated “using Microsoft APIs, command line interface (CLI) scripts and PowerShell scripts.”
As users reduce the document library version limit, it becomes harder and harder to restore previous versions. Proofpoint laid out two different ways threat actors could damage document libraries: creating too many versions of a file or drastically reducing the version limits.
It is unlikely threat groups would go through the effort of exceeding the default version limit of 500 due to the machine resources needed. The easiest method would be to reduce the versioning number to 1, meaning only the most recent version of the file before the last edit is saved and can be restored by a user.
Files can then be encrypted twice, making it so organizations are unable to restore the original versions without the decryption key.
A Microsoft spokesperson told The Record that the technique “requires a user to have already been fully compromised by an attacker.”
“We encourage our customers to practice safe computing habits, including exercising caution when clicking on links to webpages, opening unknown file attachments, or accepting file transfers,” the spokesperson said.
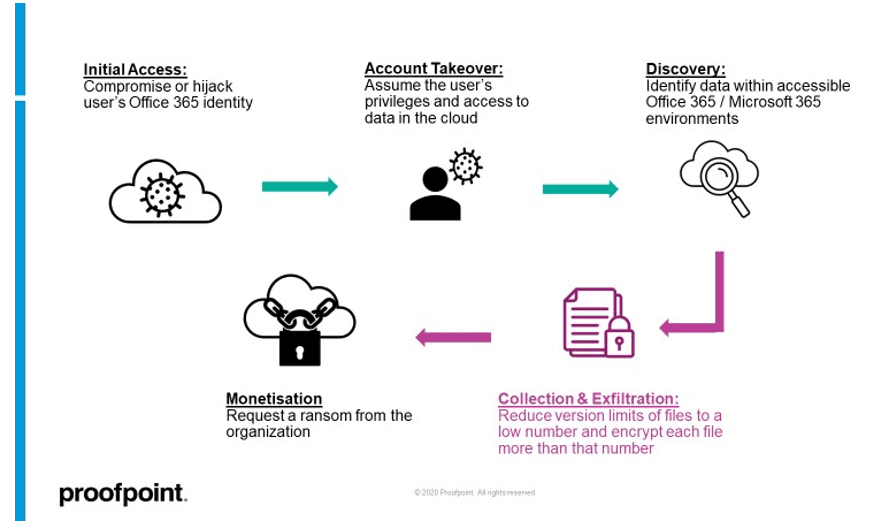
Proofpoint’s report laid out three different ways attackers could gain access to SharePoint Online or OneDrive accounts, including account compromise through phishing or brute force attacks or tricking users into authorizing third-party OAuth apps with application scopes for SharePoint or OneDrive access.
Ransomware groups could also hijack the web session of a logged-in user or take over a live API token for SharePoint Online or OneDrive.
Proofpoint’s researchers added that Microsoft told them the configuration functionality for versioning settings are “working as intended” and said older versions of files “can be potentially recovered and restored for an additional 14 days with the assistance of Microsoft Support.”
A Microsoft spokesperson said in a statement that for business accounts, they encourage administrators "to consider the use of Conditional Access to block or limit access to SharePoint and OneDrive content from unmanaged devices."
Recorded Future ransomware expert Allan Liska said SharePoint used to be a more common attack vector for ransomware groups, but isn’t targeted as often now. SharePoint was primarily the initial access vector before files were encrypted, but versioning controls were never touched, Liska told The Record.
“A resurfaced attack on SharePoint like this could be attractive to ransomware groups. And this attack wouldn’t necessarily just apply to SharePoint and Office 365. Other services, like DropBox, use a similar versioning process to protect against ransomware,” Liska explained.
“I think it is potentially a real threat but not something that ransomware groups have done.”
Several other security experts were alarmed by the findings, noting that cloud storage is typically seen as more resilient. Netenrich’s John Bambenek noted that thousands of businesses rely on SharePoint and OneDrive for file storage, believing Microsoft will keep them secure.
Versioning is also a tool that has allowed users to quickly recover corrupted or deleted documents. But he said the settings for versioning should require multi-factor authentication and generate immediate security alerts.
Vulcan Cyber senior technical engineer Mike Parkin said he always keeps local copies at various stages in his work, explaining that while cloud storage is generally more robust and secure than local storage, the report highlights that it is not immune to all security challenges.
“If anything, it should make organizations more aware of the potential pitfalls of completely trusting the cloud. It also shows the idea of ‘external backups’ is not dead,” he said.
“The challenge here is that Microsoft isn’t wrong about the feature. This is a case of an intended feature being used in unintended and malicious ways. The nature of this attack makes it easy to identify, which means it should be easy to mitigate with policies and tools.”
3rd party “off-site” backups for OneDrive and SharePoint have been available from several vendors for years, and this is exactly the use case, if not the detailed attack, those vendors were talking about, Parkin added.
Proofpoint said the impact of the attack vector will be reduced if files are stored in a hybrid state on both endpoints and in the cloud through cloud sync folders.
Vectra CTO Aaron Turner also suggested assuring that all browsers are up-to-date to avoid browser pass-through attacks to M365 and OneDrive.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



