Scammers Are Trying To Capitalize on the Race To Deliver COVID-19 Vaccines
In March and April, when fear and uncertainty about the coronavirus pandemic reached a high point in the U.S., hackers and scammers started incorporating language about COVID-19 into phishing attacks and new web domains to trick anxious victims into downloading malware, a U.S. cybersecurity agency warned.
New research and legal actions suggest that scammers are now pivoting their efforts: As governments and healthcare organizations race to deliver inoculations, hackers are embracing vaccine-related phishing lures.
On Friday, the U.S. Attorney’s Office for the District of Maryland seized two websites—mordernatx.com and regeneronmedicals.com—that purported to be related to actual biotechnology companies developing COVID-19 treatments. Instead, the sites were used to collect information from visitors, with the goal of using the data for fraud, phishing attacks, and malware deployment, according to the Department of Justice.
“These individuals took advantage of fear during the global pandemic and attempted to steal personal information for nefarious purposes,” said Homeland Security Investigations - Baltimore Special Agent in Charge John Eisert.
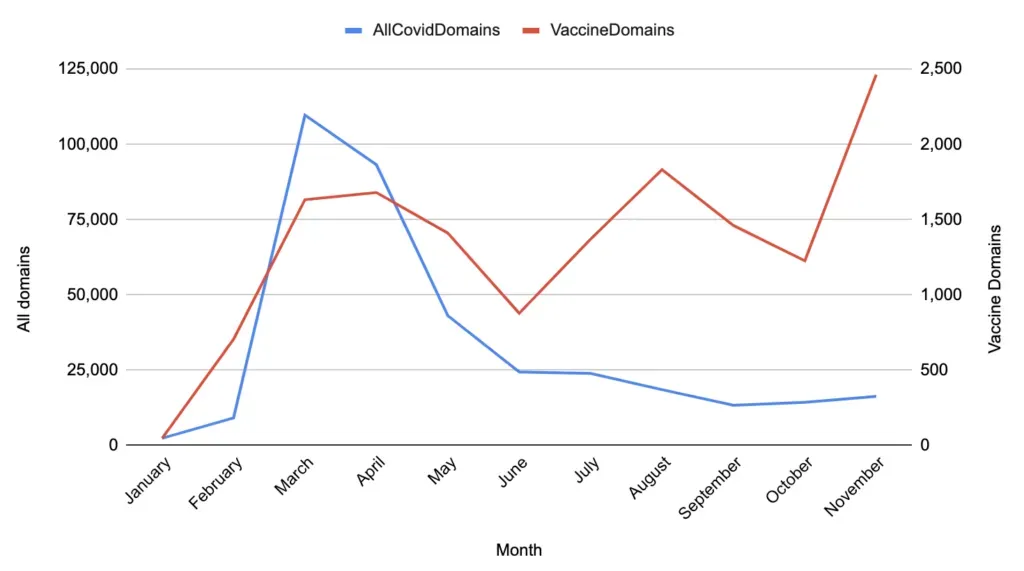
Newly-registered web domains that mention vaccines surged in November to about 2,500 over the course of the month, according to data collected by Recorded Future. That’s about double the vaccine-related domains registered in October. At the same time, new COVID-19 related domains have plateaued at around 25,000 a month since June, down from a high of about 110,000 in March, according to the data.
Although it’s difficult to know what proportion of these newly-registered domains are malicious or are being used in scam campaigns, there’s no legitimate reason for a surge in new vaccine-related domains, said Bill Ladd, chief data scientist at Recorded Future. Additionally, a closer examination of the newly-registered domains reveals that many are tied to past malicious activity—some contain the names of vaccine developers, but are not actually linked to those companies.
On Thursday, for example, researchers from cybersecurity firm Avanan published a scam email that purportedly came from the head of vaccine distribution for BioNTech, which recently received emergency use authorization for the vaccine it developed with Pfizer. Although the email doesn’t contain links—a strategy aimed at bypassing phishing filters—it does list a website that appears to be related to BioNTech.
“If the user was to Google the domain, they would be directed to a fully functional website that includes contact information matching what's in the email,” according to the post. “Pfizer-BioNTech announced an effective vaccine candidate on November 9th. The attackers registered the domain "biontechvaccines.org" on November 11th and within days, had duplicated the entire BioNTech website with a WordPress version on the fake domain.”
Avanan said its researchers were seeing “a massive rise in sophisticated vaccine-related” phishing scams.
Other cybersecurity companies, including Tel Aviv-based Check Point, have also identified similar campaigns that use vaccine-related language to hook potential victims. In a recent email campaign containing the subject line “pfizer’s Covid vaccine: 11 things you need to know”, cybercriminals included an executable file disguised as vaccine-related information that actually contained a remote access trojan known as Agent Tesla, according to Check Point researchers.
“We expect that this vaccine-related campaign is the first of many more that will target both organizations and individuals over the coming months, as the race to deliver vaccines globally approaches the final stages,” the report read. Check Point said it has also observed a “sharp rise” in ew vaccine-related domains in November.
Adam Janofsky
is the founding editor-in-chief of The Record from Recorded Future News. He previously was the cybersecurity and privacy reporter for Protocol, and prior to that covered cybersecurity, AI, and other emerging technology for The Wall Street Journal.



