Russian hacking group spoofed Microsoft login page of US military supplier: report
A well-known hacking group with ties to Russia spoofed the Microsoft login page of a U.S. military weapons and hardware supplier as a phishing lure, according to a new report.
Researchers from Recorded Future’s Insikt Group found that starting in July, a group known as SEABORGIUM – but also referred to as Callisto, COLDRIVER and TA446 — used infrastructure, tactics and techniques to further credential harvesting efforts linked to the Russian state. The Record is an editorially independent unit of Recorded Future.
These tactics included the use of domain names employing a specific pattern construct along with Let’s Encrypt TLS certificates, the use of a specific cluster of hosting providers, and the use of a small cluster of autonomous systems.
The report notes that both Microsoft and Google have published reports in recent months about SEABORGIUM’s phishing operations. All of the reports tie the group’s activity to Russia and said most of their work is centered on “phishing and credential theft campaigns that have led to intrusions and data theft.”
Google said in March and May that the group conducted “credential phishing campaigns using Gmail accounts targeting nongovernmental organizations and think tanks, journalists, and government and defense officials.” The phishing emails typically contain malicious PDF or DOC file links that are hosted on Google Drive and Microsoft OneDrive.
“SEABORGIUM primarily focuses its targeting on NATO countries, including a specific emphasis on the United States and the United Kingdom. The group also targeted Ukraine in the run-up to Russia’s full-scale invasion of the country in February 2022,” the researchers said.
Insikt Group found 38 registered domains used by the group since January – with most registered with NameCheap, Porkbun, REG.RU, and regway.
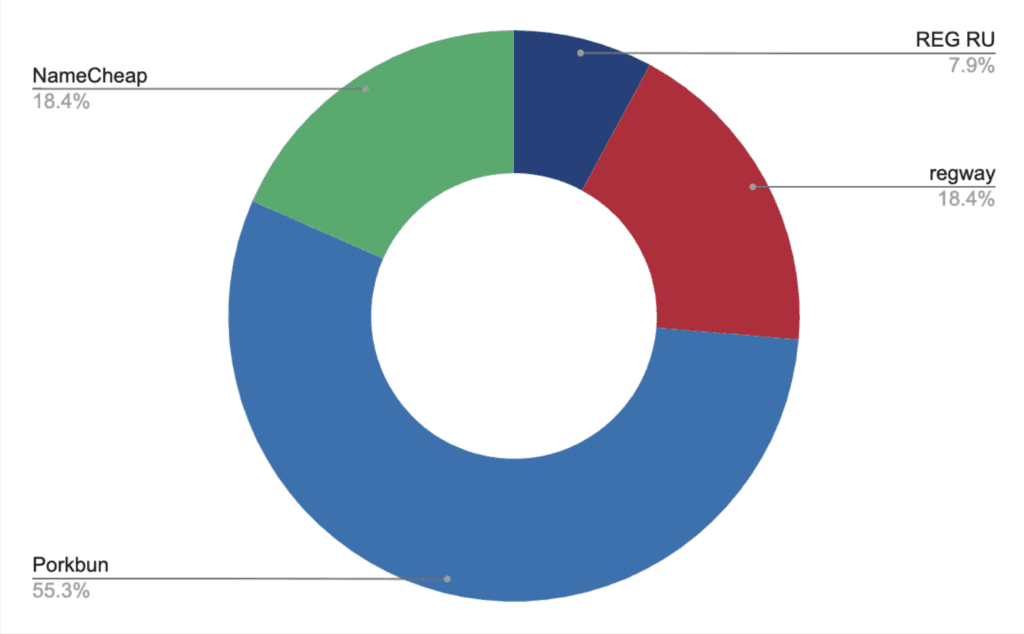
Most of the domains found by the researchers used similar names and styles meant to resemble legitimate online sources – like “cloud-safety[.]online,” “share-drive-ua[.]com” and “nonviolent-conflict-service[.]com.”
All of the domains had X.509 TLS certificates provided by Let’s Encrypt – a non-profit that serves as the world’s largest certificate authority and is used by more than 300 million websites.
Of the 38 domains identified, at least nine of them had explicit references to organizations that the group may be targeted. The researchers did not have explanations for why certain domains were used other than simple attempts to spoof the real entities and potentially lure in victims or targets.
The domains included attempts to spoof defense companies like UMO Poland, Global Ordnance and Sangrail LTD as well as organizations like The Commission for International Justice and Accountability and satellite company Blue Sky Network.
“Analysis of the 9 domains reveals that 7 share a focus around industry verticals that would likely be of interest to Russia-nexus threat groups, especially in light of the war in Ukraine. The 2 outlier domains are probably intended to masquerade as the Ministry of Internal Affairs of the Russian Federation,” they wrote.
“The TAG-53 domain “drive-globalordnance[.]com” includes a spoofed sign-in page for the legitimate company Global Ordnance, a military weapons and hardware supplier in the US. The spoofed sign-in page uses Global Ordnance branding and is suspected to be used for follow-on credential harvesting after a target has been phished.”
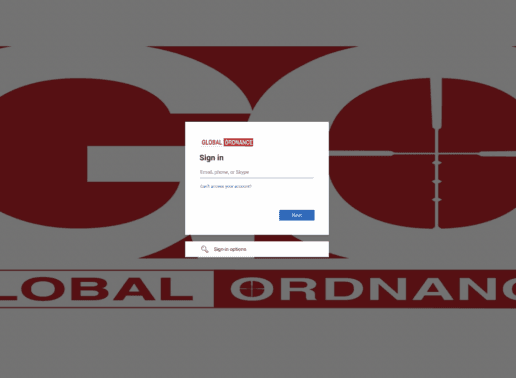
THE SPOOFED GLOBAL ORDNANCE WEBSITE.
The group has been implicated in several campaigns over the years, with Microsoft revealing in August that SEABORGIUM has carried out cyberespionage attacks against government organizations, think tanks, and defense contractors in NATO countries since at least 2017.
In May, Reuters reported that the group was behind a hack-and-leak operation that tried to build a narrative around high-level Brexit proponents planning a coup. The group has also been implicated in other campaigns targeting experts in Russian affairs, Russian citizens abroad and former intelligence officials, Microsoft researchers said.
Insikt Group noted that the use of specifically tailored infrastructure by the group indicates the “long-term use of similar techniques for their strategic campaigns.”
The report follows another from Microsoft last Friday that said Russia was coordinating cyberattacks alongside missile strikes targeting critical infrastructure in Ukraine.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.