She was traveling to a cybersecurity event—then her hotel got hit by ransomware
Nordic Choice Hotels, a major Norwegian hospitality chain, was hit by a ransomware attack at the same time that security expert Runa Sandvik stayed at one of their hotels while traveling to lead a security training.
The company’s IT systems were infected on December 2 and the attack primarily affected reservation and room key creation systems, according to a press statement. The chain says it reported the incident to local law enforcement and had no indication that credit card information was affected. The release cited the attack as being associated with Conti—a well-known ransomware-as-a-service operation.
The Record spoke with Sandvik—who previously helped secure journalists at The New York Times and at the Freedom of the Press Foundation—about what it was like to experience the attack first-hand, and what she wished the hotel chain would have done differently while communicating with guests during the disruption. Our conversation is below, lightly edited for length and clarity.
Andrea Peterson: For readers who might not know, who are you in the security world and what was the context of your recent hotel stay?
Runa Sandvik: For the last ten years or so I’ve been focused on security for journalists, whether it’s freelancers or larger media organizations—trying to figure out how you design and then build a security program, and integrate that into the larger enterprise. That’s work that I’m still doing and really passionate about.
Last week, I was in Oslo because there are three organizations in Norway that organized a sort of master class for journalists who had been invited for the Nobel Peace Prize Ceremony that was on Friday. It was a two or three day program for what turned out to be a fairly small group of journalists, that included a two or three hour session on digital security that I got to teach.
AP: And it sounds like that digital security work intersected with your trip in ways that were a bit unexpected. What happened at the hotel where you stayed?
RS: So I got to my hotel late Sunday [December 5], checked in at 9pm and at first they had the wrong dates for my check in—though I don’t think that was necessarily related to the IT troubles—but they had free rooms and were very helpful and reassured me they would figure it out. Then as they were trying to get keycards ready, it kept needing to redo it and they referenced general IT problems and the system being slow.
This was the type of hotel where you had the reception desk and then right across was the elevator, but you needed the keycard to request the elevator so the woman would try to make a keycard and open the elevator to make sure that it worked.
After a couple of tries she gave me a card she confirmed worked in the elevator, but I got up to the room and it didn't work there. So I took the elevator back down and said the keycard doesn’t work, and they say: “Ok, well, unfortunately we are just going to have to escort you to the room and open it for you,” which meant for the next few days, everytime I needed to leave my room I could not get back in on my own.
AP: So you had your own little security escort taking you to and from your room?
RS: Exactly. It was a very interesting experience.
AP: Not sure that would make me feel more secure to be honest…
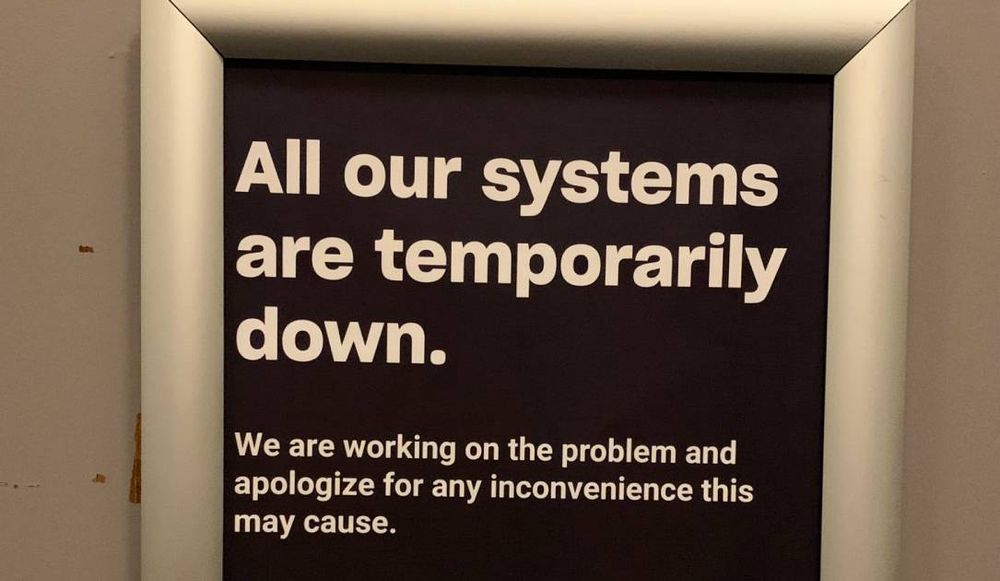
RS: It was actually in the elevator up to the room the first time where I saw the poster that I took a photo of that essentially said, “All of our systems are down, we’re working on it…”
That’s when it dawned on me, “Oh wait, this is that hotel chain—the one that’s having trouble this week.” It’s not something I considered until I saw the poster.
AP: What information did you receive as a guest at the time?
RS: None. Upon checking in, clearly there was something slow or off with the systems, and there was the poster in the elevator.
Then the next morning I asked them what’s going on and at that point they still said the system was still just slow and said there was IT trouble—some sort of virus. I asked, “Well, what kind of virus?” And they said well, we’ve probably been hacked. That was the message.
Aside from that, there was no message directly to guests, not during, not afterwards—what I know now, I know through my own research. The group that organized the trip did book the reservation for me, so it’s possible that they received some communication. But I haven’t seen any other guests receive anything, I don’t know.
[Note: Sandvik shared a message she received from the hotel chain the day after this interview on Twitter, which references delays and offers a discount on a stay through February of 2022, but did not appear to reference the ransomware specifically. ]
Nordic Choice Hotels offering a 50% discount on my next stay until end of Feb ‘22. No mention of ransomware. More related to yesterday’s news of yet another lockdown in Norway? pic.twitter.com/JmE3Si5lu9
— Runa Sandvik (@runasand) December 14, 2021
AP: Later the company did put out a public press release and FAQ acknowledging it was the victim of an attack.
RS: Yeah, that would have been about an hour after I spoke with reception that morning.
AP: And from your Twitter thread, you were able to get a keycard the next day.
RS: Yep.
AP: How do you wish the organization would have responded to this sort of situation?
RS: I was thinking about that. This was a case where Nordic Choice could have come out very early on and been transparent about what was going on, what they knew and when, and we would have all remembered them as a company that was very transparent about a security incident—like FireEye with SolarWinds. Instead, it left me questioning that poster in the elevator and the framing of words they are using in updates to the media.
There are still so many questions about exactly what was taken, and when, and what was the scope including just how far back it goes. For example, I’ve stayed at this hotel chain before on my own, but I haven’t had any sort of notice from the hotel chain related to past visits. There are questions about what happened and what it means for me and other customers, including those that organized this trip for me.
AP: Do you think you’d have all of these questions if you weren’t yourself a security researcher?
RS: Probably not. I think if I wasn’t in this field and I didn’t really pay attention to this part of the news, given that there’s been no notice from the hotel chain itself I would have chalked it up to an IT problem. I don’t think I would have considered all these other bits and pieces.
AP: It’s interesting the ways that we’re not seeing ransomware is showing up in our lives more and more in unexpected ways. I had an experience where I went to visit my family, and ended up reporting on the neighboring county suffering an attack. Have you had any other recent ransomware encounters?
RS: None that I can think of, but it’s been a pandemic so I’ve spent a lot more time at home… I did think in the case of the hotel and one of the things I raised on Twitter was… should I use the Wi-Fi? I ultimately did, because I knew the former chief information security officer who did a really good job explaining how the system was set up separately. But imagine you’re staying at the hotel that’s infected and being told there are IT troubles—the systems are down and they’re working on it—so you use the free Wi-Fi and it isn’t set up the same way? What if that introduced more risk based on just how the hotel chain has decided to design the network? It brings up all these interesting “what-if” questions.
Andrea Peterson
(they/them) is a longtime cybersecurity journalist who cut their teeth covering technology policy at ThinkProgress (RIP) and The Washington Post before doing deep-dive public records investigations at the Project on Government Oversight and American Oversight.