Researchers tie Ukraine cyber intrusion attempt to suspected Chinese threat actor ‘Scarab’
Ukraine’s Computer Emergency Response Team (CERT-UA) published evidence this week indicating that Chinese threat actors are targeting their systems publicly for the first time since Russia invaded Ukraine.
CERT-UA released an alert on Tuesday about an attempted intrusion by a threat actor they tagged as UAC-0026 and cybersecurity firm SentinelOne confirmed on Thursday that the culprit is ‘Scarab,’ a group that was first identified in 2015.
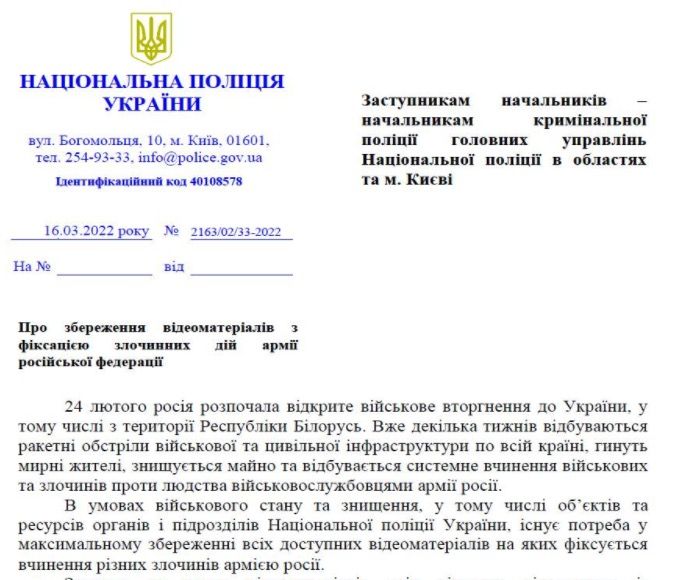
“The government team for responding to computer emergencies in Ukraine, CERT-UA, found the RAR-archive, ‘On the preservation of video recordings of the criminal actions of the army of the Russian Federation.rar,’ which contains the EXE-file of the same name,” CERT-UA explained.
“Running the executable file will create a lure document ‘# 2163_02_33-2022.pdf’ on the computer (applies to a letter from the National Police of Ukraine), as well as a DLL file with the MZ header ‘officecleaner.dat’ and the BAT file ‘officecleaner’ removed. .bat,’ which will ensure the formation of the correct DLL-file, run it and write to the Windows registry to ensure consistency. The mentioned DLL-file is classified as a malicious program HeaderTip, the main purpose of which is to download and execute other DLL-files.”
CERT-UA, which did not mention China or Scarab in its alert, added that similar attacks were seen in September 2020.
SentinelOne said Scarab has been operating since at least 2012 and has previously targeted people in Russia, the US and several other countries.
The cybersecurity firm said it was able to tie UAC-0026 to Scarab through an analysis of the malware used in the attack.
“Further relationships can be identified through the reuse of actor-unique infrastructure between the malware families associated with the groups,” SentinelOne explained, adding that there is evidence showing that the creator of the malware is using the Windows operating system in a Chinese language setting.
“Based on known targets since 2020, including those against Ukraine in March 2022, in addition to specific language use, we assess with moderate confidence that Scarab is Chinese speaking and operating under geopolitical intelligence collection purposes.”
CERT-UA shared copies of the lure documents used in the attack, which attempted to mimic documents from the National Police of Ukraine.
Ukraine continues to face a barrage of cyberattacks, DDoS incidents and defacements, predominantly from threat actors based in Russia.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



