Researchers, NSA cybersecurity director warn of hackers targeting Zyxel vulnerability
A widespread, critical vulnerability affecting Zyxel firewalls is being exploited by hackers, according to several researchers and the director of cybersecurity for the NSA.
Cybersecurity nonprofit Shadowserver Foundation said it began seeing exploitation attempts starting on May 13. CVE-2022-30525 was first discovered by cybersecurity firm Rapid7 and the firewalls affected by the vulnerability are sold to both small companies and corporate headquarters. The tools are used for VPN solutions, SSL inspection, web filtering, intrusion protection, and email security.
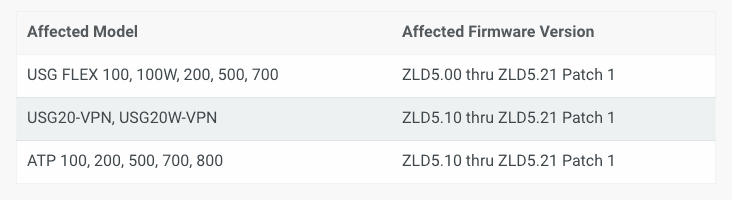
The vulnerability allows attackers to modify specific files and then execute some OS commands on a vulnerable device. It has a CVSS v3 score of 9.8 — indicating a high severity — and affects Zyxel firewalls supporting Zero Touch Provisioning (ZTP), which includes the ATP series, VPN series, and the USG FLEX series.
Netenrich principal threat hunter John Bambenek noted that the devices tend to cater to small-to-medium businesses.
“These organizations are most likely in no position to know there is a vulnerability, much less have an expert that they can ask to patch it,” Bambenek said.
Bugcrowd founder Casey Ellis told The Record that while the vulnerability is fairly remedial, it does “have a propensity to turn up on networking and embedded equipment.”
“Despite command injection being well-known and avoidable, it continues to show up and be impactful on the internet,” Ellis said. “This demonstrates the continued need for assurance and coverage of code and systems by security researchers and those who ‘think differently’ to the developers of these products, and have the ability to catch what may have been missed.”
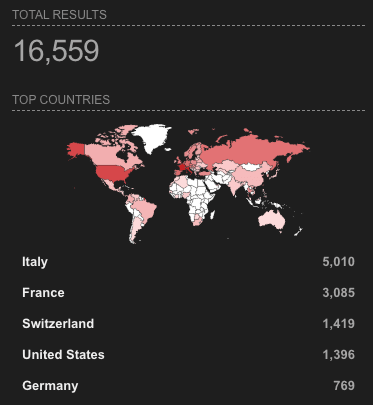
Shadowserver said it found even more systems that may be vulnerable.
“We see at least 20 800 of the potentially affected Zyxel firewall models (by unique IP) accessible on the Internet. Most popular are USG20-VPN (10K IPs) and USG20W-VPN (5.7K IPs). Most of the CVE-2022-30525 affected models are in the EU - France (4.5K) and Italy (4.4K),” Shadowserver explained.
Zyxel patched the vulnerability after it was discovered in April. But on Sunday morning, NSA director of cybersecurity Rob Joyce confirmed that the vulnerability was being exploited in the wild.
Exploitation underway. Check your Zyxel firewall version and patch. CVE-2022-30525 https://t.co/EpVwlb8jeQ
— Rob Joyce (@NSA_CSDirector) May 15, 2022
Rapid7 also had a fair amount of criticism for how Zyxel handled the vulnerability. After notifying the company of the issue and proposing a coordinated disclosure date in June, Zyxel instead released patches to address the issue on April 28.
“Zyxel did not publish an associated CVE or security advisory. On May 9, Rapid7 independently discovered Zyxel’s uncoordinated disclosure. The vendor then reserved CVE-2022-30525. This patch release is tantamount to releasing details of the vulnerabilities, since attackers and researchers can trivially reverse the patch to learn precise exploitation details, while defenders rarely bother to do this,” the company explained.
“Therefore, we're releasing this disclosure early in order to assist defenders in detecting exploitation and to help them decide when to apply this fix in their own environments, according to their own risk tolerances. In other words, silent vulnerability patching tends to only help active attackers, and leaves defenders in the dark about the true risk of newly discovered issues.”
In the patch document, Zyxel only said there was a “miscommunication” with Rapid7 and did not respond to requests for comment.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



