Researchers find bugs in IKEA smart lighting system
Two vulnerabilities have been discovered in a line of IKEA smart lights that would allow an attacker to take control of the system and make the bulbs rapidly blink on and off.
Kari Hulkko and Tuomo Untinen at the Synopsys Cybersecurity Research Center said they approached Ikea about the bugs — tagged as CVE-2022-39064 and CVE-2022-39065 — in June 2021.
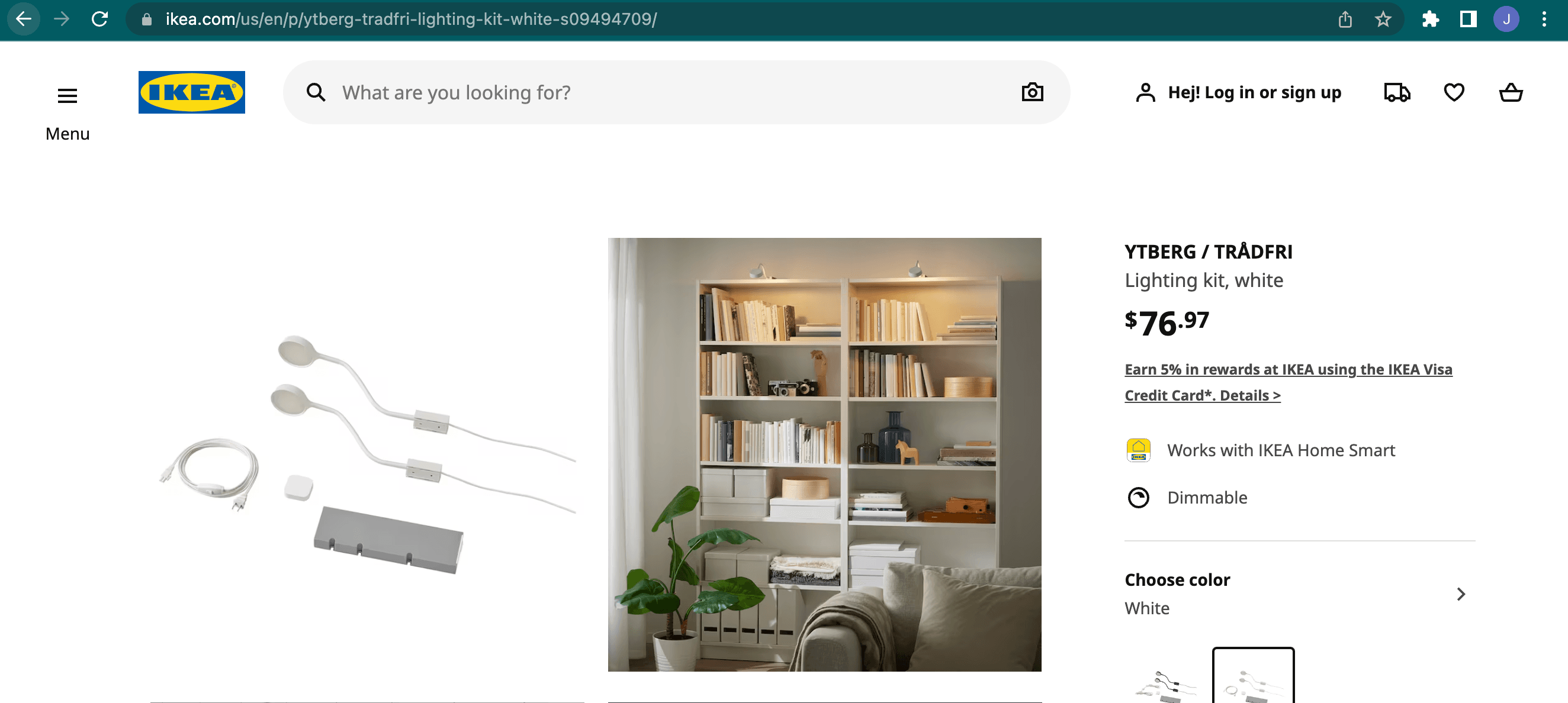
The issues affect IKEA’s Trådfri Gateway type E1526 version 1.17.44 and earlier. The product runs for about $80 and is typically used to light bookshelves and dressers.
By the end of October 2021, IKEA responded to the inquiry and said it was producing a fix for the vulnerabilities. The company published a fix for CVE-2022-39065 on February 16, 2022 and a partial remedy for CVE-2022-39064 in June.
Hulkko and Untinen said CVE-2022-39064 carries a CVSS score of 7.1 and centers on the Zigbee protocol — a type of wireless network used for low-power, low data rate devices like radios, medical devices and home automation tools.
The vulnerability allows an attacker to send a malicious frame through the protocol to make IKEA's TRÅDFRI bulb blink. If they resend the malicious message multiple times, the bulb performs a factory reset.
“This causes the bulb to lose configuration information about the Zigbee network and current brightness level. After this attack, all lights are on with full brightness, and a user cannot control the bulbs with either the IKEA Home Smart app or the TRÅDFRI remote control,” Synopsys researchers explained.
The second related bug can make it so the TRÅDFRI is unresponsive to the device remote control and the IKEA Home Smart app.
Hulkko and Untinen said all vulnerable devices “within radio range are affected” and noted that it has a CVSS score of 6.5.
“To recover from this attack, a user could manually power cycle the gateway. However, an attacker could reproduce the attack at any time,” they said.
An IKEA spokesperson told The Record that the company has worked with Synopsys since the disclosures to improve the “safety and functionality” of their smart devices.
“It is important to note that the identified issue is not jeopardizing the safety for our customers and can be replicated in other, already known ways due to the design of the Zigbee protocol,” the spokesperson said.
“We also want to clarify that it is not possible to gain access to sensitive information inside TRÅDFRI Gateway or our smart devices.”
Hulkko and Untinen said that while CVE-2022-39065 has been solved with all software versions 1.19.26 or later, CVE-2022-39064 has not been fully dealt with.
“Version V-2.3.091 fixes issues with some malformed frames but not with all known malformed frames,” they said, sharing a video of the exploit.
IKEA did not respond to requests for comment about when a full patch will be released.
'Thankful that this was just lightbulbs'
Bud Broomhead, CEO of IoT security firm Viakoo, explained that the danger of an exploit like this is it can cause a factory reset.
With many Zigbee and related IoT devices this can lead to the IoT device connecting into a threat actor-controlled Zigbee network, not the one it was intended to.
“Zigbee is a network of connected IoT devices; this form of IoT where devices work together in a tightly-coupled way is very attractive to threat actors, because of the ability to exploit multiple devices through a single network breach (as opposed to loosely coupled individual devices that do not impact each other if one is compromised),” he said.
Broomhead added that more work needs to be done on improving and securing Zigbee as a standard because he believes it is too easy for threat actors to intercept encrypted data transmissions and impact device operations or worse.
“I’m thankful that this was just lightbulbs, not door locks, cameras, or industrial control systems, all of which can be connected through Zigbee, yet can have more devastating consequences from being breached and exploited,” he noted.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



