Ransomware gang tries to extort Apple hours ahead of Spring Loaded event
The operators of the REvil ransomware are demanding that Apple pay a ransom demand to avoid having confidential information leaked on the dark web.
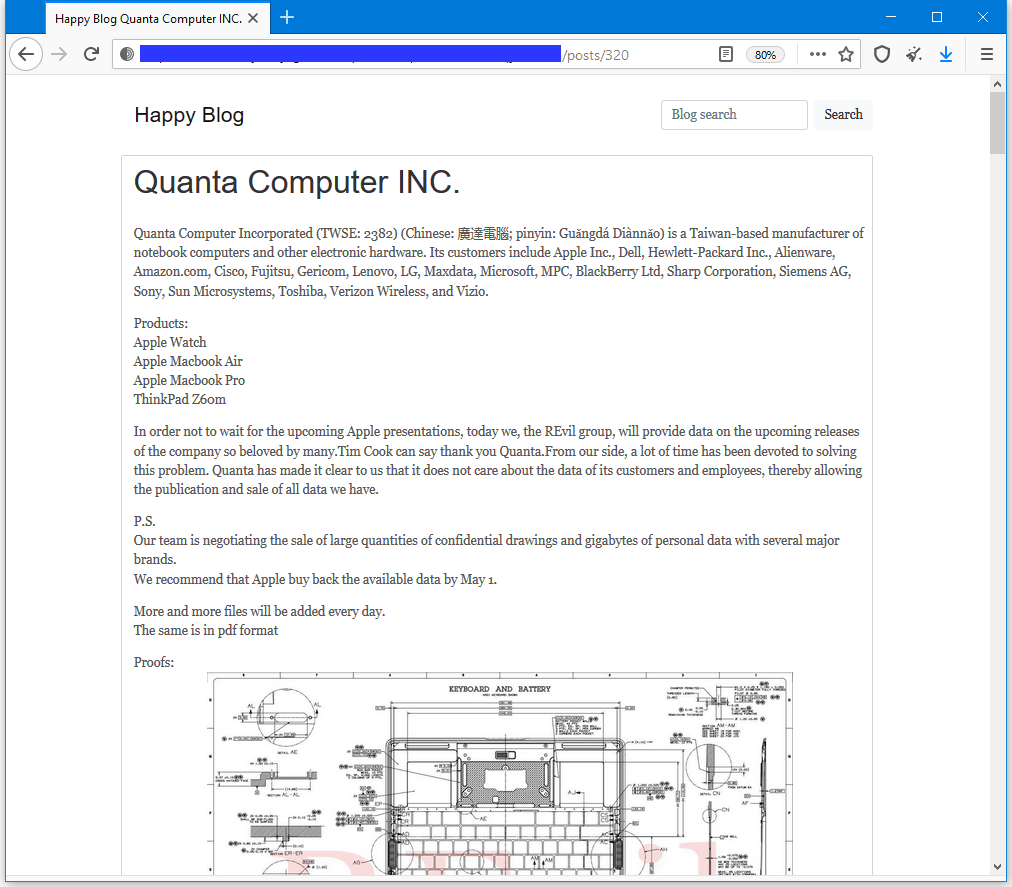
The REvil crew claims it came into possession of Apple product data after breaching Quanta Computer, a Taiwanese company that is the biggest laptop manufacturer in the world and which is also one of the companies that assemble official Apple products based on pre-supplied product designs and schematics.
In a message posted on a dark web portal where the ransomware gang usually threatens victims and leaks their data, the REvil gang said that Quanta refused to pay to get its stolen data back and, as a result, the REvil operators have now decided to go after the company's primary customer instead.
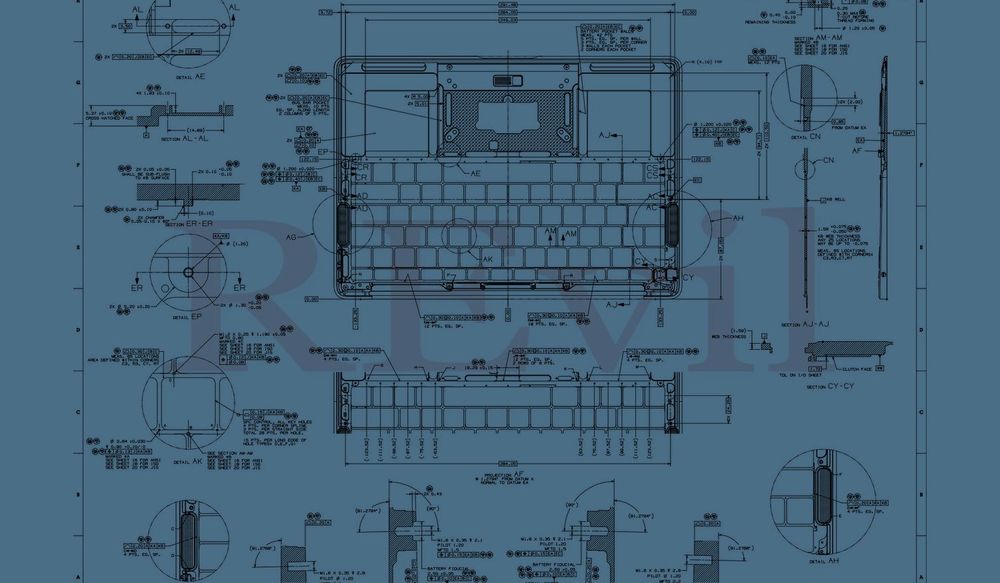
The REvil gang posted 21 screenshots depicting Macbook schematics and threatened to publish new data every day until Apple or Quanta paid the ransom demand.
Furthermore, the ransomware gang also hinted that the data of other companies might also be leaked online.
"Our team is negotiating the sale of large quantities of confidential drawings and gigabytes of personal data with several major brands," the REvil operators wrote. "We recommend that Apple buy back the available data by May 1."
Known customers of Quanta Computer include some of the biggest laptop vendors in the world, such as HP, Dell, Microsoft, Toshiba, LG, Lenovo, and many others.
A source familiar with the Quanta negotiations said the REvil gang asked for a $50 million ransom demand, similar to the sum they requested from laptop maker Acer last month. It is unclear how much money the REvil gang is expecting from Apple now.
Extortion attempt perfectly timed with Apple event
The extortion attempt was also perfectly timed for maximum visibility to coincide with the Spring Loaded event, where Apple announced new products and software updates.
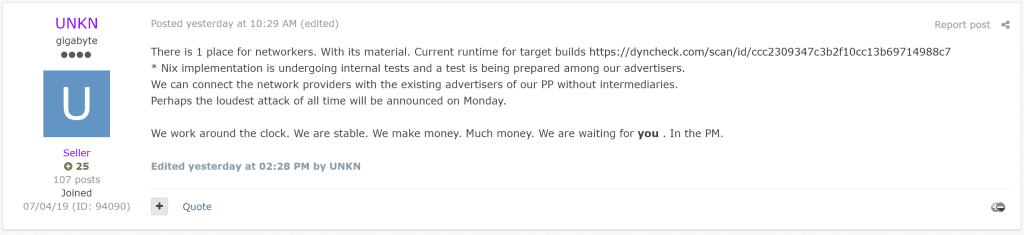
Dmitry Smilyanets, a Recorded Future threat intel analyst, told The Record that the REvil public spokesperson, an individual going by the nickname of UNKN, hinted at today's announcement in a forum post on Sunday, calling today's leak as the "loudest attack ever."
Smilyanets told The Record that this is also the first major incident where a ransomware gang has publicly requested a ransom demand from a victim's customer after the attacked company refused to pay a ransom fee.
This is a new approach in the double extortion name-and-shame technique, where the threat actor engages with the affected third parties after the unsuccessful attempt to negotiate ransom with the primary victim.
Dmitry Smilyanets, Recorded Future threat intel analyst
Reached out for comment, Apple said it was looking into the incident and had nothing to share at the moment. A Quanta Computer spokesperson could not be reached for comment, and a person taking calls asked call back the next day.
It is still highly possible that both companies downplay the incident and categorize the stolen data as non-sensitive.
Files leaked today show schematics for Macbook laptops, none of which are particularly sensitive nor appear to include anything beyond assembly information and technical details. One of the file was dated March 9, 2021, but is unclear if the depicted product was new or just updated technical specs.
While Quanta is considered the largest laptop manufacturer in the world, the second one, fellow Taiwanese company Compal suffered its own ransomware incident in November 2020 when it had some of its files stolen and internal network encrypted by the DoppelPaymer ransomware gang.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.