Ransomware gang takedowns causing explosion of new, smaller groups
The ransomware ecosystem continues to splinter, with new gangs proliferating in the wake of law enforcement takedowns that have scattered affiliates and prompted criminal rebrands.
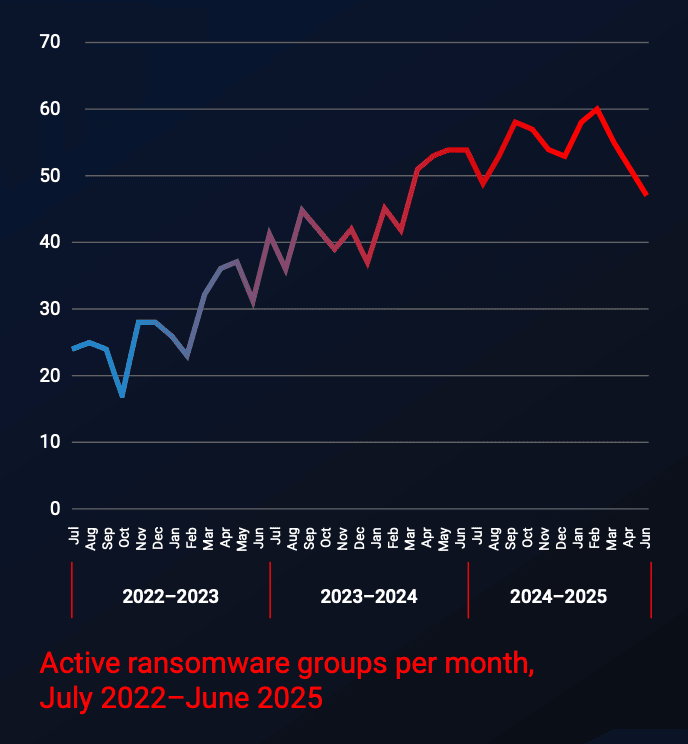
Observers have raised alarms about the explosion of new groups this year. MalwareBytes tracked 41 newcomers between July 2024 and June 2025, with more than 60 total ransomware gangs operating at once for the first time since they began tracking the data.
Researchers at the company attributed an increase in overall ransomware attacks to the growth in active groups, which has doubled over the last three years.
“Whether this reflects more participants or smaller group sizes, it suggests that something — perhaps a mix of domain experience, commoditized malware, and abundant AI — is lowering the barrier to entry,” the company said last week.
“This steady growth in active ransomware groups has been fueled by consistent patterns of formation, closure, and activity. Over the last three years, approximately 50 new groups have appeared each year, around 30 have exited, and a typical group has attacked around five targets per month.”
Law enforcement agencies in the U.S. and Europe have been successful in takedowns of large operations like LockBit, BlackCat/AlphV and Hive. The operations have been able to destroy the infrastructure used by the groups but have struggled to secure arrests, allowing many threat actors to simply spin up new gangs.
Credit: MalwareBytes
Cybersecurity firm Flashpoint released a study of ransomware-as-a-service (RaaS) groups last week, noting that many of the new groups are simply rebrands of defunct operations. The company noted that groups have emerged using leaked ransomware source code in their operations.
“For example, top ransomware group SafePay shares code with LockBit. The fingerprints of other notable ransomware groups, like Conti, are also apparent in the codebase of other ransomware groups,” they said.
Recorded Future ransomware expert Allan Liska said it is now “incredibly dangerous” to be a large RaaS group, noting the successes of the international Ransomware Task Force established under former U.S. President Joe Biden. The Record is an editorially independent unit of Recorded Future.
Liska explained that it is risky for ransomware operations to have a low bar for accepting affiliates because of the possibility they could be infiltrated by law enforcement.
“So, ransomware affiliates are left with two choices: try to join one of the still operating closed groups like Qilin or Akira or start up their own ransomware operation,” Liska said.
“All the tools are still there for small groups: there is plenty of leaked ransomware code, so you don’t have to program something new, you can still buy access to victim networks from initial access brokers and almost all of the tools experienced ransomware operators used are free/cracked/open source with lots of documentation. So, it’s not that hard to go out on your own.”
The fragmentation of the ransomware ecosystem is reflected in the numbers. MalwareBytes said the top-10 most active groups now only account for half of all attacks, down from 69% in 2022.
The company’s researchers echoed Liska’s assessment that hackers no longer need to rely on large RaaS operations to conduct attacks.
But Malwarebytes noted that the ransomware ecosystem has always been volatile, with dominant groups often rising and falling annually. At times, the top 15 active groups in one year had little or no footprint in the next year.
“This churn at the top is exemplified by groups like RansomHub, which emerged out of nowhere to become the leading ransomware group following the demise of LockBit and ALPHV,” the company said.
“While less dominant than its predecessors, RansomHub accounted for about 10% of all known attacks over the last 12 months, but its reign lasted less than a year and the group’s leak site and negotiation portals went silent after March 31, 2025, for unknown reasons.”
Distrust and infighting
John Fokker, head of threat intelligence at Trellix, said another important aspect of the fracturing trend is the lack of trust between the affiliates and core members of ransomware gangs.
The way U.K. officials infiltrated LockBit and the FBI burrowed into the Hive group eroded trust in the cybercriminal underworld, causing infighting and suspicion among any new members.
Fokker, a former police official from the Netherlands, compared the situation to a Mexican standoff — where the members of a ransomware gang have guns pointed at each other.
One negative byproduct of the distrust is an increase in exit scams and affiliates offering stolen data on multiple ransomware leak sites, he said.
He used the ransomware attack on Change Healthcare as an example. That hacker launched the devastating attack as part of the AlphV/BlackCat ransomware gang but once that group went under due to law enforcement action, the threat actor offered the stolen data through the RansomHub operation.
Almost a year later, that same threat actor was kicked out of RansomHub, illustrating how fragile the ties are between some hackers and the groups they join. Groups are also attacking each other and disclosing information, showing that the law enforcement efforts have created distrust.
“The hierarchy days of big groups, in my opinion, are over — which is a normal evolution because if you look at how the underground operates, a lot of people are entrepreneurs,” Fokker explained.
He said groups typically employed people who specialized in certain tasks. Some members would be good at money laundering, others would be good at coding or attacking VPN services.
As groups like REvil and Conti grew in size and prominence, it became harder and harder to control affiliates, many of whom felt like they were not getting paid enough.
“So a bunch of them say ‘screw this, I'm doing it myself.’ We track a lot of the leak sites and you could see from 2024 we had about 40 different groups that turned into hundreds a year later,” he said. “So we can see it's getting more scattered.”
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



