Price of IPv4 addresses, one of the Internet's hottest commodities, reaches all-time high
Companies that own or manage IPv4 address blocks should be on the lookout for an increased risk of hijacking attempts in the coming months as the price for an IPv4 address has reached an all-time high, which might encourage threat actors to go after unused or unsecured IPv4 inventory.
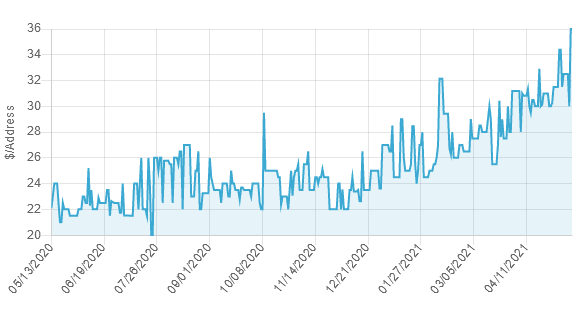
"Our data shows that prices jumped up quite substantially from 2020 into 2021," said IPv4.Global, the operator of an online marketplace for IPv4 addresses.
"Back in 2020, prices peaked in the summer at around $23-24. But in the first quarter of 2021, prices reached $32 in February— which is nearly 30% higher than 2020's peak. In fact, this year's floor prices are about the same as last year's peaks at $23-26," the company said in its 2021 Q1 round-up.
Currently, IPv4 prices are still going up. Today's peak on the IPv4.Global marketplace reached a new high at $36 per IPv4 address.
Marketplaces like IPv4.Global have sprung up in recent years after the organizations that allocate IPv4 addresses in North America (ARIN), Central and South America (LACNIC), and Europe, Russia, and the Middle East (RIPE NCC) announced that they run out of IPv4 addresses.
But while some marketplaces provide a legal way for owners of IPv4 address blocks to sell or rent unused IPv4 addresses, there is also an underground market for these operations, mainly fueled by cybercrime groups who hijack IPv4 addresses from companies that have failed to secure their inventories.
With IPv4 depletion reaching critical levels and with prices reaching an all-time high, it is expected that criminal groups attempt new hijacking attacks throughout 2021.
A history of previous high-profile IPv4 hijacking incidents
IPv4 hijacking incidents, while not as common as other forms of cybercrime, have been happening on a steady basis for years.
Many of these incidents have happened after crooks realized they could register expired domains for companies that once owned an IPv4 address block or create new companies with lookalike names and then contact organizations like ARIN, APNIC, RIPE NCC, AFRINIC, or LACNIC to hijack legitimate IPv4 address blocks from their real owners using fake or forged documents. [see talk below]
IPv4 hijacks were also made easy because some organizations that host these IPv4 address blocks also don't always verify if IPv4 address block transfers are legitimate.
The perfect example of this is a now-infamous Spamhaus blog post from January 2016 in which the internet anti-spam group accused Verizon of hosting more than 4 million hijacked IPv4 addresses, which cybercrime groups were abusing to send email spam campaigns undisturbed.
Since then, IPv4 hijacking incidents have continued to rise as IPv4 address availability got scarcer.
Some notorious IPv4 hijackers were caught and disconnected by the big internet service providers, but these incidents were rare.
In May 2019, the US Justice Department charged a North Carolina man with hijacking 757,760 IP addresses from ARIN, but criminal charges like these, in general, have been very rare.
But the biggest IPv4 address heist took place in Africa, at AFRINIC, where a former exec stole more than 4.1 million IP addresses from the organization in 2019, an IPv4 inventory that was estimated to be worth around $80 million.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.