Police shut down Android app that turned smartphones into proxies
Spanish police have seized servers and arrested the operators of an Android app designed to broadcast pirate video streams, but which also secretly sold users' personal data and ensnared smartphones into proxy and DDoS botnets.
Named Mobdro, the app was downloaded more than 100 million times, according to Spanish National Police.
Although on its official websites, the app used benign descriptions, once installed, it allowed users to access and view pirated video streams, usually for online sporting events.
Spanish officials said they began an investigation into the app in 2018 after receiving complaints from the English Premier League, the Spanish Football League, and other creative associations.
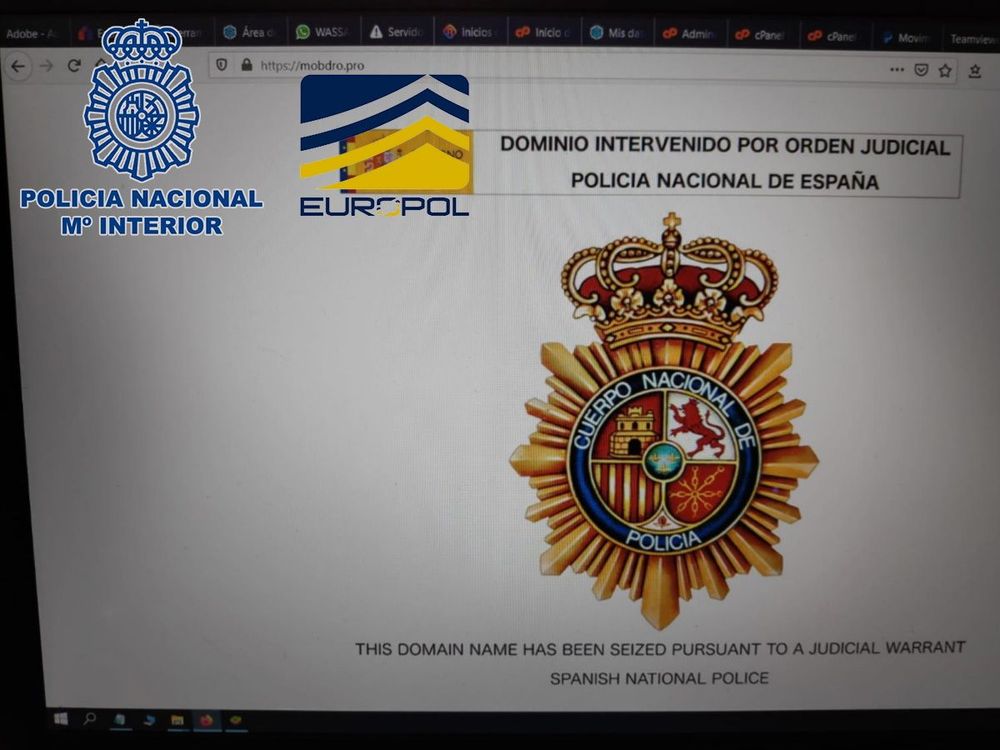
Starting last month, investigators began cracking down on the app's authors, with the help of Europol, Interpol, Eurojust, and authorities in Andorra.
These efforts targeted the operation's leader, a former Spanish citizen relocated to Andorra, and three engineers, and included the following:
- Three house searches (2 in Spain and 1 in Andorra)
- Four arrests (3 in Spain and 1 in Andorra)
- Four court orders to take down domains
- 20 web domains and servers blocked
- Bank accounts frozen
- One server was taken down in Portugal, and another one under investigation in Czechia
Investigators said the Spanish company behind the app and server infrastructure made more than €5 million, based on seized documents.
The profits primarily came from showing ads inside the app and selling users' personal data to online advertisers.
But Spanish authorities said that "with the progress of the investigation," their agents also identified another source of revenue that consisted of enrolling user devices into another company's network.
According to Spanish and Europol officials, this unnamed company used the devices as proxy bots in its anonymization offering and for DDoS attacks.
However, industry experts to whom The Record spoke today were not surprised by these revelations. The app was always considered high-risk, as it was never submitted and distributed through the official Google Play Store, and a 2019 Digital Citizens report [PDF] firmly classified it as malware, even warning about features in its code that could be abused to ensnare devices into a botnet.
Among the other findings there were:
- Researchers discovered malware on apps used to illegally watch movies, sports, and other content that came pre-loaded on devices.
- As soon as a researcher downloaded the ad-supported illicit movie and live sports streaming app "Mobdro," malware within the app forwarded the researcher's Wi-Fi network name and password to a server that appeared to be in Indonesia.
- Malware probed the researchers' network, searching for vulnerabilities that would enable it to access files and other devices. The malware uploaded, without permission, 1.5 terabytes of data from the researcher's device.
- Mobdro sought access to media content and other legitimate apps on the researcher's network.
- The researchers uncovered a clever scheme that enabled criminals to pose as well-known streaming sites, such as Netflix, to facilitate illegal access to a legitimate subscription of an actual Netflix subscriber.
- Compromised versions of streaming devices – including Amazon Fire TV Sticks and "Kodi boxes" – are being sold on mainstream digital marketplaces such as eBay, Craigslist, and Facebook Marketplace.
- Researchers found pirate apps supported by advertising, including ads for premium brands such as Amazon and Mini Cooper. The use of premium ads to both fund and legitimize criminal or rogue websites or apps is an ongoing cause of concern for the advertising industry as well as premium brands.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.