Pipeline cyberattack comes after years of government warnings
Government authorities and watchdogs have warned for years that U.S. pipelines are vulnerable to cyberattacks that could potentially disrupt operations—and an attack against a major U.S. gasoline and jet fuel pipeline on Friday threatens to show how bad these incidents can be.
Colonial Pipeline Company said yesterday that it had shut down 5,500 miles of pipeline supplying the East Coast with fuel in an effort to contain a breach of its computer networks. Earlier in the day the company said network issues were causing disruptions in its pipeline system, which were later blamed on ransomware. “We proactively took certain systems offline to contain the threat, which has temporarily halted all pipeline operations, and affected some of our IT systems,” Colonial Pipeline said in a statement. “Upon learning of the issue, a leading, third-party cybersecurity firm was engaged, and they have already launched an investigation into the nature and scope of this incident, which is ongoing.”
The attack is shaping up to be the exact type of scenario that government watchdogs and other cybersecurity experts have been warning about in recent years. In 2018, the U.S. Government Accountability Office issued an 86-page report about weaknesses in the Transportation Security Administration’s pipeline security program management. The TSA, which sits under the Department of Homeland Security, has traditionally been responsible for pipeline security, and has collaborated with the Cybersecurity and Infrastructure Security Agency since that agency was formed in 2018.
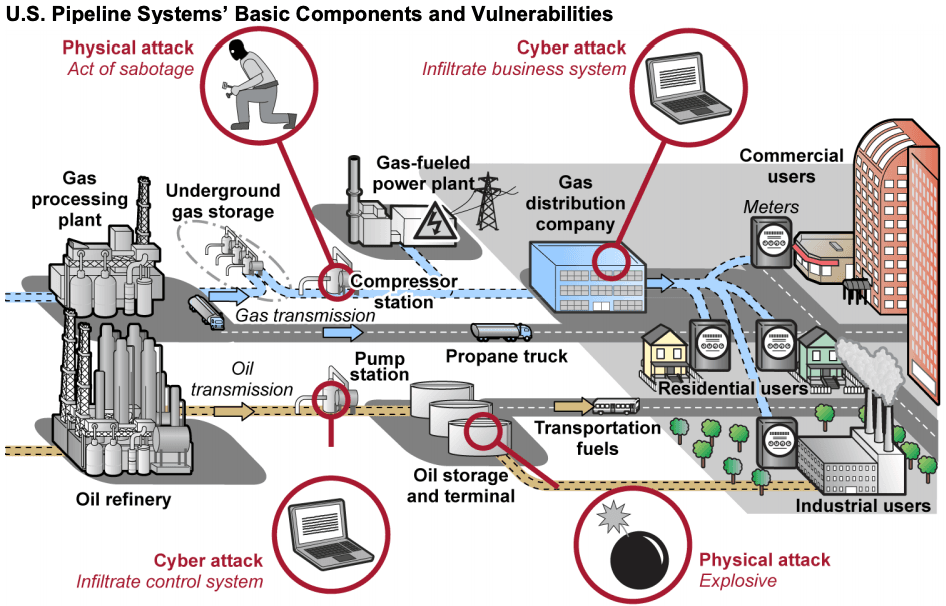
“Pipelines increasingly rely on sophisticated networked computerized systems and electronic data, which are vulnerable to cyber attack or intrusion,” the GAO said in its report. “Given that many pipelines transport volatile, flammable, or toxic oil and liquids, and given the potential consequences of a successful physical or cyber attack on life, property, the economy, and the environment, pipeline systems are attractive targets for terrorists, hackers, foreign nations, criminal groups, and others with malicious intent.”
The TSA’s pipeline cybersecurity shortcomings included not having a documented review process to ensure its guidelines reflect the latest known standards and best practices for cybersecurity. Additionally, the administration couldn’t ensure pipeline operators applied its guidance and that all critical facilities across the pipeline sector had been identified or that their vulnerabilities had been addressed, the GAO said.
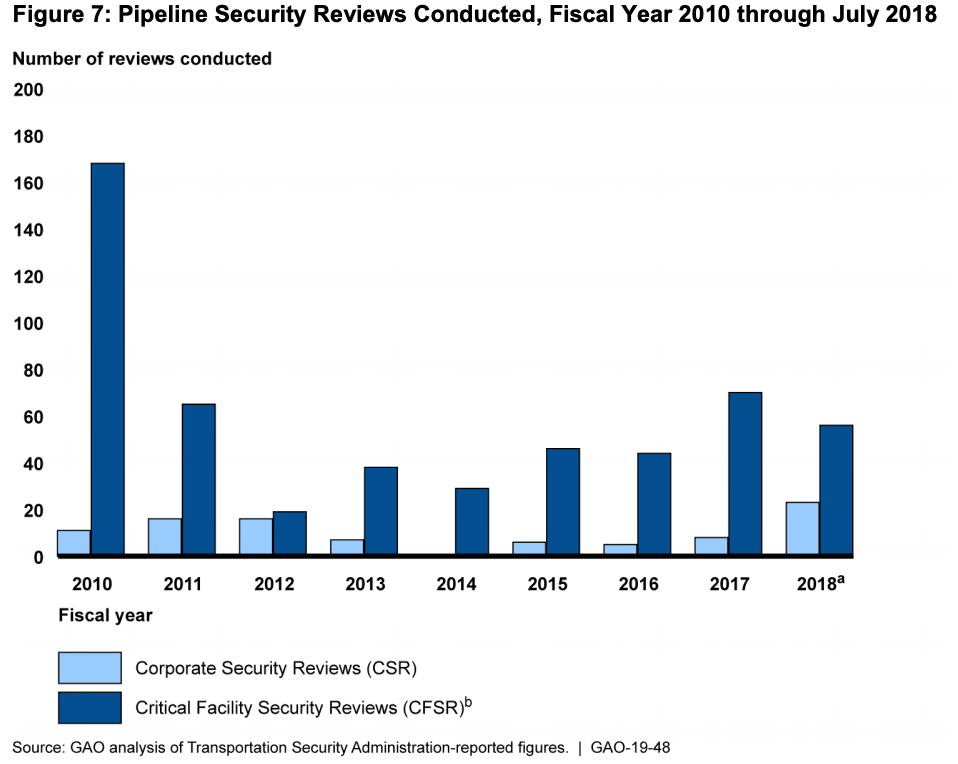
TSA officials have also said that staffing limitations have prevented them from conducting more pipeline security reviews, which would help identify vulnerabilities and the implementation of security guidelines.
I continue to have serious concerns about the TSA’s ability here... 80% doesn't cut it—we need to have a success rate of 100%."
— Richard Glick, Commissioner of the Federal Energy Regulatory Commission, during a 2019 House testimony.
At a June 2019 hearing held by the House Committee on Energy and Commerce, Rep. Fred Upton (R., Michigan) said that TSA had “less than a handful” of its 50,000 employees overseeing pipelines, and that the administration refused to testify before the committee despite bipartisan efforts.
“I continue to have serious concerns about the TSA’s ability here,” said Richard Glick, Commissioner of the Federal Energy Regulatory Commission, in response to Upton’s questions about the TSA’s handling of pipeline cybersecurity.
“We had a technical conference on cybersecurity just a few months ago and I asked [a TSA participant] about the success rate of their voluntary guidance, and she said, ‘Our hope is to have a success rate of 80%...’ 80% doesn’t cut it—we need to have a success rate of 100%,” Glick said.
Later in 2018, DHS created the Pipeline Cybersecurity Initiative—a public-private partnership that included CISA, the TSA, and other federal and private sector partners—to enhance the sector’s defenses. The initiative has three main components: assessing the cybersecurity posture and preparedness of pipeline companies, analyzing findings of pipeline cybersecurity risks, and engaging with interagency and industry partners on information sharing.
The National Risk Management Center, which is also involved in the initiative, published a Pipeline Cybersecurity Resources Library in February aimed at supplying the sector with free cybersecurity tools and information. The implementation of these resources, however, are voluntary—federal cybersecurity officials estimate that about 80% of the nation’s critical infrastructure is owned by the private sector, making mandatory rules harder to implement.
Adam Janofsky
is the founding editor-in-chief of The Record from Recorded Future News. He previously was the cybersecurity and privacy reporter for Protocol, and prior to that covered cybersecurity, AI, and other emerging technology for The Wall Street Journal.



